CVE-2015-5323
Jenkins Unauthorized API Token Escalation
Description
Jenkins before 1.638 and LTS before 1.625.2 do not properly restrict access to API tokens which might allow remote administrators to gain privileges and run scripts by using an API token of another user.
INFO
Published Date :
Nov. 25, 2015, 8:59 p.m.
Last Modified :
May 6, 2026, 10:30 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 2.0 | MEDIUM | [email protected] |
Solution
- Update the affected packages.
- Upgrade to a version after 1.638 or 1.625.2.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2015-5323.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2015-5323 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2015-5323
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2015-5323 vulnerability anywhere in the article.
-
carnal0wnage.com
Jenkins - CVE-2018-1000600 PoC
second exploit from the blog post https://blog.orange.tw/2019/01/hacking-jenkins-part-1-play-with-dynamic-routing.html Chained with CVE-2018-1000600 to a Pre-auth Fully-responded SSRF https://jenkins. ... Read more
-
carnal0wnage.com
Jenkins - messing with exploits pt3 - CVE-2019-1003000
References: https://www.exploit-db.com/exploits/46453 http://blog.orange.tw/2019/02/abusing-meta-programming-for-unauthenticated-rce.html This post covers the Orange Tsai Jenkins pre-auth exploit Vuln ... Read more

-
carnal0wnage.com
Jenkins - SECURITY-180/CVE-2015-1814 PoC
Forced API token change SECURITY-180/CVE-2015-1814 Affected Versions All Jenkins releases <= 1.605 All LTS releases <= 1.596.1 PoC Tested against Jenkins 1.605 POST /user/user2/descriptorByName/jenkin ... Read more

-
carnal0wnage.com
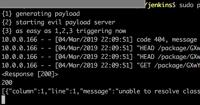
Jenkins - SECURITY-200 / CVE-2015-5323 PoC
API tokens of other users available to admins SECURITY-200 / CVE-2015-5323 API tokens of other users were exposed to admins by default. On instances that don’t implicitly grant RunScripts permission t ... Read more
-
carnal0wnage.com
Jenkins Master Post
A collection of posts on attacking Jenkins http://www.labofapenetrationtester.com/2014/08/script-execution-and-privilege-esc-jenkins.html Manipulating build steps to get RCE https://medium.com/@uraniu ... Read more

-
carnal0wnage.com
Jenkins - messing with exploits pt2 - CVE-2019-1003000
After the release of Orange Tsai's exploit for Jenkins. I've been doing some poking. PreAuth RCE against Jenkins is something everyone wants. While not totally related to the blog post and tweet the f ... Read more

-
carnal0wnage.com
Jenkins - messing with new exploits pt1
Jenkins notes for: https://blog.orange.tw/2019/01/hacking-jenkins-part-1-play-with-dynamic-routing.html http://blog.orange.tw/2019/02/abusing-meta-programming-for-unauthenticated-rce.html to download ... Read more
The following table lists the changes that have been made to the
CVE-2015-5323 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Status Change by [email protected]
May. 06, 2026
Action Type Old Value New Value -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://rhn.redhat.com/errata/RHSA-2016-0489.html Added Reference https://access.redhat.com/errata/RHSA-2016:0070 Added Reference https://wiki.jenkins-ci.org/display/SECURITY/Jenkins+Security+Advisory+2015-11-11 -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CPE Deprecation Remap by [email protected]
Dec. 17, 2019
Action Type Old Value New Value Changed CPE Configuration OR *cpe:2.3:a:redhat:openshift:2.0:*:enterprise:*:*:*:*:* OR *cpe:2.3:a:redhat:openshift:2.0:*:*:*:*:*:*:* -
Modified Analysis by [email protected]
Jun. 14, 2016
Action Type Old Value New Value Changed CPE Configuration Configuration 1 OR *cpe:2.3:a:cloudbees:jenkins:1.637:*:*:*:*:*:*:* *cpe:2.3:a:cloudbees:jenkins:1.625.1:*:*:*:lts:*:*:* Configuration 2 OR *cpe:2.3:a:redhat:openshift:3.1:*:*:*:enterprise:*:*:* (and previous) Configuration 3 OR *cpe:2.3:a:redhat:openshift:2.0:*:enterprise:*:*:*:*:* Configuration 1 OR *cpe:2.3:a:redhat:openshift:3.1:*:*:*:enterprise:*:*:* (and previous) Configuration 2 OR *cpe:2.3:a:redhat:openshift:2.0:*:enterprise:*:*:*:*:* Configuration 3 OR *cpe:2.3:a:jenkins:jenkins:1.625.1:*:*:*:lts:*:*:* (and previous) Configuration 4 OR *cpe:2.3:a:jenkins:jenkins:1.637:*:*:*:*:*:*:* (and previous) -
CVE Translated by [email protected]
Jun. 12, 2016
Action Type Old Value New Value Removed Translation CloudBees Jenkins en versiones anteriores a 1.638 y LTS en versiones anteriores a 1.625.2 no restringe adecuadamente el acceso a tokens de la API que podría permitir a administradores remotos obtener privilegios y ejecutar secuencias de comandos mediante el uso de un token de API de otro usuario. Added Translation Jenkins en versiones anteriores a 1.638 y LTS en versiones anteriores a 1.625.2 no restringe adecuadamente el acceso a tokens de la API lo que podría permitir a administradores remotos obtener privilegios y ejecutar secuencias de comandos mediante el uso de un token de API de otro usuario. -
CVE Modified by [email protected]
Jun. 11, 2016
Action Type Old Value New Value Changed Description CloudBees Jenkins before 1.638 and LTS before 1.625.2 do not properly restrict access to API tokens which might allow remote administrators to gain privileges and run scripts by using an API token of another user. Jenkins before 1.638 and LTS before 1.625.2 do not properly restrict access to API tokens which might allow remote administrators to gain privileges and run scripts by using an API token of another user. -
Modified Analysis by [email protected]
May. 19, 2016
Action Type Old Value New Value Changed CPE Configuration Configuration 1 OR *cpe:2.3:a:redhat:openshift:3.1:*:*:*:enterprise:*:*:* (and previous) Configuration 2 OR *cpe:2.3:a:cloudbees:jenkins:1.637:*:*:*:*:*:*:* *cpe:2.3:a:cloudbees:jenkins:1.625.1:*:*:*:lts:*:*:* Configuration 1 OR *cpe:2.3:a:cloudbees:jenkins:1.637:*:*:*:*:*:*:* *cpe:2.3:a:cloudbees:jenkins:1.625.1:*:*:*:lts:*:*:* Configuration 2 OR *cpe:2.3:a:redhat:openshift:3.1:*:*:*:enterprise:*:*:* (and previous) Configuration 3 OR *cpe:2.3:a:redhat:openshift:2.0:*:enterprise:*:*:*:*:* -
CVE Modified by [email protected]
Apr. 09, 2016
Action Type Old Value New Value Added Reference http://rhn.redhat.com/errata/RHSA-2016-0489.html -
Modified Analysis by [email protected]
Mar. 23, 2016
Action Type Old Value New Value Changed CPE Configuration Configuration 1 OR *cpe:2.3:a:cloudbees:jenkins:1.637:*:*:*:*:*:*:* *cpe:2.3:a:cloudbees:jenkins:1.625.1:*:*:*:lts:*:*:* Configuration 1 OR *cpe:2.3:a:redhat:openshift:3.1:*:*:*:enterprise:*:*:* (and previous) Configuration 2 OR *cpe:2.3:a:cloudbees:jenkins:1.637:*:*:*:*:*:*:* *cpe:2.3:a:cloudbees:jenkins:1.625.1:*:*:*:lts:*:*:* -
CVE Modified by [email protected]
Feb. 05, 2016
Action Type Old Value New Value Added Reference https://access.redhat.com/errata/RHSA-2016:0070 -
Modified Analysis by [email protected]
Nov. 27, 2015
Action Type Old Value New Value Added CPE Configuration Configuration 1 OR *cpe:2.3:a:cloudbees:jenkins:1.637:*:*:*:*:*:*:* *cpe:2.3:a:cloudbees:jenkins:1.625.1:*:*:*:lts:*:*:* Added CVSS V2 (AV:N/AC:L/Au:S/C:P/I:P/A:P) Changed Reference Type https://wiki.jenkins-ci.org/display/SECURITY/Jenkins+Security+Advisory+2015-11-11 No Types Assigned https://wiki.jenkins-ci.org/display/SECURITY/Jenkins+Security+Advisory+2015-11-11 Advisory Added CWE CWE-264 -
Initial Analysis by [email protected]
Nov. 27, 2015
Action Type Old Value New Value