CVE-2018-0824
Microsoft COM for Windows Deserialization of Untrusted Data Vulnerability - [Actively Exploited]
Description
A remote code execution vulnerability exists in "Microsoft COM for Windows" when it fails to properly handle serialized objects, aka "Microsoft COM for Windows Remote Code Execution Vulnerability." This affects Windows 7, Windows Server 2012 R2, Windows RT 8.1, Windows Server 2008, Windows Server 2012, Windows 8.1, Windows Server 2016, Windows Server 2008 R2, Windows 10, Windows 10 Servers.
INFO
Published Date :
May 9, 2018, 7:29 p.m.
Last Modified :
Oct. 28, 2025, 2:13 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Microsoft COM for Windows contains a deserialization of untrusted data vulnerability that allows for privilege escalation and remote code execution via a specially crafted file or script.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Unknown
https://msrc.microsoft.com/update-guide/en-US/advisory/CVE-2018-0824; https://nvd.nist.gov/vuln/detail/CVE-2018-0824
Affected Products
The following products are affected by CVE-2018-0824
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 2.0 | MEDIUM | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Apply the appropriate security updates or cumulative updates for your version of Windows.
- Reboot the system if prompted after updates are installed.
Public PoC/Exploit Available at Github
CVE-2018-0824 has a 16 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2018-0824.
| URL | Resource |
|---|---|
| http://www.securityfocus.com/bid/104030 | Broken Link Third Party Advisory VDB Entry |
| http://www.securitytracker.com/id/1040848 | Broken Link Third Party Advisory VDB Entry |
| https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-0824 | Patch Vendor Advisory |
| https://www.exploit-db.com/exploits/44906/ | Exploit Third Party Advisory VDB Entry |
| http://www.securityfocus.com/bid/104030 | Broken Link Third Party Advisory VDB Entry |
| http://www.securitytracker.com/id/1040848 | Broken Link Third Party Advisory VDB Entry |
| https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-0824 | Patch Vendor Advisory |
| https://www.exploit-db.com/exploits/44906/ | Exploit Third Party Advisory VDB Entry |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2018-0824 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2018-0824 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2018-0824
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
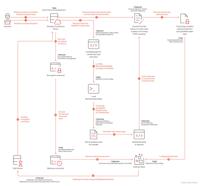
Comprehensive threat intelligence research focused on Advanced Persistent Threats (APTs), including APT41 (Wicked Panda), covering threat actor activity, MITRE ATT&CK mappings, IOCs, malware, detection strategies, and defensive recommendations.
Secra is a cutting-edge tool designed to identify and report security vulnerabilities.
analysis cybersecurity hacker kali-linux python security tools vulnerability vulnerability-scanners network-security pentest
Python
Vulnex is a fast and powerful tool for detecting service and device versions with high accuracy and identifying vulnerabilities in the discovered versions.
cve cve-scanning cybersecurity python scanner searching tool-hacking vulnerabilities
Python
None
An automated repo to track Nuclei template scanning capabilities against the CISA KEV.
cisa-kev nuclei scanning vulnerabilities cisa
Makefile Python Shell
None
An ongoing & curated collection of awesome software best practices and techniques, libraries and frameworks, E-books and videos, websites, blog posts, links to github Repositories, technical guidelines and important resources about Exploit Development.
code-execution developer developer-experience developer-tools development development-tools exploit exploitation exploitation-framework exploitation-frameworks exploitation-menu vulnerability-detection
Collection of Windows Privilege Escalation (Analyse/PoC/Exploit)
None
Windows Exploit Development Tutorial Series
Python PLSQL JavaScript
None
None
esoteric
None
POC for CVE-2018-0824
C++ C
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2018-0824 vulnerability anywhere in the article.
-
Cybersecurity News
Godzilla Backdoor: A Stealthy Threat Targeting Atlassian Confluence Flaw (CVE-2023-22527)
Attack chain | Image: TrendMicroA recent discovery by cybersecurity researchers at Trend Micro has unveiled a sophisticated new attack vector targeting Atlassian Confluence servers, leveraging the cri ... Read more

-
Cybersecurity News
Critical CVE-2024-45321 Flaw in Popular Perl Module Installer cpanminus, No Patch Available
In a significant security advisory, the Perl community has been alerted to a critical vulnerability, CVE-2024-45321, affecting the widely-used App::cpanminus (cpanm) tool. Rated with a CVSS score of 9 ... Read more

-
Cybersecurity News
Mirai Botnet Exploits Zero-Day Vulnerability CVE-2024-7029 in AVTECH IP Cameras
Akamai’s Security Intelligence Response Team (SIRT) has discovered a widespread Mirai botnet campaign exploiting a recently disclosed zero-day vulnerability (CVE-2024-7029) in AVTECH IP cameras. The v ... Read more

-
Cybersecurity News
Critical Vulnerabilities Expose Hitachi Energy MicroSCADA X SYS600 to Cyberattacks
Hitachi Energy has issued a cybersecurity advisory addressing multiple critical vulnerabilities discovered in their MicroSCADA X SYS600 product, widely used for monitoring and controlling power system ... Read more

-
Cybersecurity News
New Attack on Microsoft 365 Copilot Steals Personal Data
A cybersecurity researcher has uncovered a critical vulnerability in the AI-powered assistant Copilot, integrated into Microsoft 365, which enables malicious actors to exfiltrate sensitive data.The ex ... Read more

-
Cybersecurity News
BlackByte Ransomware Group Exploits VMware CVE-2024-37085 Flaw, Shifts Tactics
The BlackByte ransomware group has re-emerged with an unsettling surge in activity and a refined set of tactics, techniques, and procedures (TTPs) that pose a heightened risk to organizations. Cisco T ... Read more

-
Cybersecurity News
CVE-2024-38206: SSRF Vulnerability in Microsoft Copilot Studio Exposes Internal Infrastructure
Tenable Research has discovered a critical server-side request forgery (SSRF) vulnerability in Microsoft’s Copilot Studio, potentially allowing attackers to gain access to sensitive internal resources ... Read more

-
Cybersecurity News
SolarWinds Web Help Desk Hit by Critical Vulnerability (CVE-2024-28987)
SolarWinds has issued an urgent security advisory for its Web Help Desk (WHD) software, warning of a critical hardcoded credential vulnerability (CVE-2024-28987) that poses a significant risk to organ ... Read more

-
Cybersecurity News
Lazarus Group Exploits Microsoft Zero-Days CVE-2024-38193, Patch Urgently
Last week, Microsoft addressed multiple high-severity security vulnerabilities in its security updates, some of which have already been exploited by hackers. For instance, the CVE-2024-38193 (CVSS 7.8 ... Read more

-
Cybersecurity News
Windows Sandbox Gets Supercharged: Clipboard and File Sharing Arrive
Microsoft continues to refine its Windows 11 experience with the introduction of significant updates to the Windows Sandbox application in the latest Windows 11 Canary Build 27686. Designed as a secur ... Read more

-
Cybersecurity News
Critical Vulnerability Found in Flatpak: CVE-2024-42472 (CVSS 10) Exposes Files Outside Sandbox
Please enable JavaScriptA serious security flaw has been discovered in Flatpak, a popular system for distributing and running sandboxed desktop applications on Linux. The vulnerability, tracked as CVE ... Read more

-
Cybersecurity News
Windows Users Beware: CVE-2024-6768 – New ‘Blue Screen of Death’ Vulnerability Affects All
A newly discovered vulnerability in the Windows operating system has raised concerns among cybersecurity experts due to its potential to trigger the infamous “Blue Screen of Death” (BSOD). Identified ... Read more

-
TheCyberThrone
TheCyberThrone Security Week In Review – August 10, 2024
Welcome to TheCyberThrone cybersecurity week in review will be posted covering the important security happenings. This review is for the week ending Saturday, August 10, 2024.Google Fixes Android Zero ... Read more

-
TheCyberThrone
Google Fixes Android Zeroday Vulnerability CVE-2024-36971
Google has released patches for 46 bugs affecting its Android operating system in its August 2024 security update. This includes an actively exploited kernel vulnerability tracked as CVE-2024-36971 af ... Read more

-
Cybersecurity News
Warning: Fake WinRar Websites Distributing Malware
SonicWall has recently issued a cybersecurity alert about a deceptive website that mimics the official WinRar site. This fake site, win-rar.co, not only closely resembles the legitimate WinRar site bu ... Read more

-
TheCyberThrone
CISA adds CVE-2018-0824 to its KEV Catalog
The U.S. CISA added a deserialization of untrusted data vulnerability in Microsoft COM for Windows, tracked as CVE-2018-0824 with a CVSS score of 7.5, to its Known Exploited Vulnerabilities (KEV) cata ... Read more

-
security.nl
Cisco meldt misbruik van zes jaar oud Windows-lek bij recente aanvallen
dinsdag 6 augustus 2024, 10:27 door Redactie, 0 reactiesLaatst bijgewerkt: Vandaag, 10:32 Aanvallers maken misbruik van een zes jaar oude kwetsbaarheid in Windows, ook al is een update sinds 8 mei 201 ... Read more

-
The Hacker News
Google Patches New Android Kernel Vulnerability Exploited in the Wild
Mobile Security / Vulnerability Google has addressed a high-severity security flaw impacting the Android kernel that it has been actively exploited in the wild. The vulnerability, tracked as CVE-2024- ... Read more

-
Cyber Security News
APT41 Hackers Attacking Research Institute with ShadowPad and Cobalt Strike
Cisco Talos has unearthed a sophisticated cyber-espionage campaign targeting a Taiwanese government-affiliated research institute. The attack, attributed to the notorious Chinese hacking group APT41, ... Read more

-
The Register
Google gamed into advertising a malicious version of Authenticator
Infosec in brief Scammers have been using Google's own ad system to fool people into downloading a borked copy of the Chocolate Factory's Authenticator software. A team at security shop Malwarebytes s ... Read more
The following table lists the changes that have been made to the
CVE-2018-0824 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 28, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2018-0824 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 22, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2018-0824 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2018-0824 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2018-0824 -
Modified Analysis by [email protected]
Mar. 31, 2025
Action Type Old Value New Value -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://www.securityfocus.com/bid/104030 Added Reference http://www.securitytracker.com/id/1040848 Added Reference https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-0824 Added Reference https://www.exploit-db.com/exploits/44906/ -
Modified Analysis by [email protected]
Aug. 08, 2024
Action Type Old Value New Value Removed CVSS V3 NIST AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H Changed Reference Type http://www.securityfocus.com/bid/104030 Third Party Advisory, VDB Entry http://www.securityfocus.com/bid/104030 Broken Link, Third Party Advisory, VDB Entry Changed Reference Type http://www.securitytracker.com/id/1040848 Third Party Advisory, VDB Entry http://www.securitytracker.com/id/1040848 Broken Link, Third Party Advisory, VDB Entry Changed CPE Configuration OR *cpe:2.3:o:microsoft:windows_10:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1607:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1703:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1709:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1803:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_8.1:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_rt_8.1:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:itanium:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:x64:* *cpe:2.3:o:microsoft:windows_server_2012:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:1709:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:1803:*:*:*:*:*:*:* OR *cpe:2.3:o:microsoft:windows_10_1507:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10_1607:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10_1703:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10_1709:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10_1803:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_8.1:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_rt_8.1:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_1709:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_1803:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:itanium:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:x64:* *cpe:2.3:o:microsoft:windows_server_2012:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:-:*:*:*:*:*:*:* -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Aug. 06, 2024
Action Type Old Value New Value Added CWE CISA-ADP CWE-502 Added CVSS V3.1 CISA-ADP AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Aug. 06, 2024
Action Type Old Value New Value Added Date Added 2024-08-05 Added Required Action Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. Added Due Date 2024-08-26 Added Vulnerability Name Microsoft COM for Windows Deserialization of Untrusted Data Vulnerability -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
Modified Analysis by [email protected]
Mar. 12, 2019
Action Type Old Value New Value Changed Reference Type https://www.exploit-db.com/exploits/44906/ No Types Assigned https://www.exploit-db.com/exploits/44906/ Exploit, Third Party Advisory, VDB Entry Changed CPE Configuration OR *cpe:2.3:o:microsoft:windows_10:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1607:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1703:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1709:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1803:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_8.1:*:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_rt_8.1:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:*:sp2:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2012:*:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:1709:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:1803:*:*:*:*:*:*:* OR *cpe:2.3:o:microsoft:windows_10:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1607:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1703:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1709:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1803:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_8.1:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_rt_8.1:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:itanium:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:x64:* *cpe:2.3:o:microsoft:windows_server_2012:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:1709:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:1803:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Jun. 21, 2018
Action Type Old Value New Value Added Reference https://www.exploit-db.com/exploits/44906/ [No Types Assigned] -
Initial Analysis by [email protected]
Jun. 14, 2018
Action Type Old Value New Value Added CVSS V2 Metadata Victim must voluntarily interact with attack mechanism Added CVSS V2 (AV:N/AC:H/Au:N/C:P/I:P/A:P) Added CVSS V3 AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H Changed Reference Type https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-0824 No Types Assigned https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-0824 Patch, Vendor Advisory Changed Reference Type http://www.securitytracker.com/id/1040848 No Types Assigned http://www.securitytracker.com/id/1040848 Third Party Advisory, VDB Entry Changed Reference Type http://www.securityfocus.com/bid/104030 No Types Assigned http://www.securityfocus.com/bid/104030 Third Party Advisory, VDB Entry Added CWE CWE-502 Added CPE Configuration OR *cpe:2.3:o:microsoft:windows_10:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1607:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1703:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1709:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10:1803:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_8.1:*:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_rt_8.1:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:*:sp2:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2012:*:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:1709:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2016:1803:*:*:*:*:*:*:* -
CVE Modified by [email protected]
May. 11, 2018
Action Type Old Value New Value Added Reference http://www.securitytracker.com/id/1040848 [No Types Assigned] Added Reference http://www.securityfocus.com/bid/104030 [No Types Assigned]