CVE-2019-0683
Active Directory Elevation of Privilege
Description
An elevation of privilege vulnerability exists in Active Directory Forest trusts due to a default setting that lets an attacker in the trusting forest request delegation of a TGT for an identity from the trusted forest, aka 'Active Directory Elevation of Privilege Vulnerability'.
INFO
Published Date :
April 9, 2019, 12:29 a.m.
Last Modified :
Nov. 21, 2024, 4:17 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2019-0683
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 2.0 | MEDIUM | [email protected] | ||||
| CVSS 3.0 | MEDIUM | [email protected] |
Solution
- Apply the appropriate security update or cumulative update.
- Restart affected systems.
Public PoC/Exploit Available at Github
CVE-2019-0683 has a 17 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2019-0683.
| URL | Resource |
|---|---|
| https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0683 | Patch Vendor Advisory |
| https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0683 | Patch Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2019-0683 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2019-0683
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
None
Pentesting Active Directory
None
None
None
None
Attack and defend active directory using modern post exploitation adversary tradecraft activity
None
None
None
None
None
AD-Attack-Defense
Python
None
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2019-0683 vulnerability anywhere in the article.

-
Cyber Security News
Active Directory Attack Kill Chain Checklist & Tools List- 2025
The “Active Directory Kill Chain Attack & Defense” concept is a structured approach to understanding the sequence of events or stages involved in an Active Directory (AD) attack and the corresponding ... Read more
-
Active Directory & Azure AD/Entra ID Security
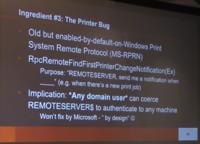
Domain Controller Print Server + Unconstrained Kerberos Delegation = Pwned Active Directory Forest
Oct 10 2018 By Sean Metcalf in ActiveDirectorySecurity, Exploit, Hacking, Microsoft Security, Security Conference Presentation/Video At DerbyCon 8 (2018) over the weekend Will Schroeder (@Harmj0y), Le ... Read more
The following table lists the changes that have been made to the
CVE-2019-0683 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0683 -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CWE Remap by [email protected]
Aug. 24, 2020
Action Type Old Value New Value Changed CWE CWE-264 CWE-276 -
Initial Analysis by [email protected]
Apr. 10, 2019
Action Type Old Value New Value Added CVSS V2 (AV:N/AC:M/Au:N/C:N/I:P/A:N) Added CVSS V3 AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:H/A:N Changed Reference Type https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0683 No Types Assigned https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-0683 Patch, Vendor Advisory Added CWE CWE-264 Added CPE Configuration OR *cpe:2.3:o:microsoft:windows_7:-:sp1:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:itanium:* *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:x64:*