CVE-2019-1003000
Jenkins Script Security Plugin Sandbox Bypass RCE Vulnerability
Description
A sandbox bypass vulnerability exists in Script Security Plugin 1.49 and earlier in src/main/java/org/jenkinsci/plugins/scriptsecurity/sandbox/groovy/GroovySandbox.java that allows attackers with the ability to provide sandboxed scripts to execute arbitrary code on the Jenkins master JVM.
INFO
Published Date :
Jan. 22, 2019, 2:29 p.m.
Last Modified :
Nov. 21, 2024, 4:17 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2019-1003000
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 2.0 | MEDIUM | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Refer to vendor advisory for details.
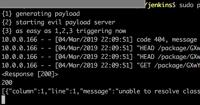
Public PoC/Exploit Available at Github
CVE-2019-1003000 has a 44 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2019-1003000.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2019-1003000 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2019-1003000
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Attack Surface Monitoring Framework for Security Researchers | Subdomain enumeration, CVE correlation, continuous monitoring
Python HTML
None
Java JavaScript HTML Groovy
Comprehensive containerized security lab with 158+ vulnerable services (OWASP, CVEs, Databases, DevOps). Features an isolated network, unified orchestration, and a production-grade automated OpenVAS/GVM scanning framework.
automation ctf cve-reproduction cybersecurity devsecops docker-lab gvm openvas owasp-top-10 penetration-testing python vulnerability-scanners
Python Shell
JenkinsBreaker: Offensive CI/CD security research framework focused on Jenkins exploitation, CVE chaining, and pipeline compromise scenarios.
ci-cd cicd-security cve-scanning devops-security exploit exploitation-framework fuzzer jenkins offensive-ci offensive-security penetration penetration-testing-framework pentest pipeline-security redteam
Python PowerShell Shell Dockerfile Groovy
Сканер уязвимостей.
Rust
Testing Docker
Dockerfile Shell HTML
PoC_cve_list
A curated collection of Proof of Concept (PoC) tools, scripts, and techniques designed for red team operations, penetration testing, and cybersecurity research. This repository focuses on providing practical resources for exploring vulnerabilities
attack cybersecurity exp hw penetration-testing poc red-team security-tools vulnerability-poc
这是一个每天同步Vulnerability-Wiki中docs-base中内容的项目
HTML
红队武器库漏洞利用工具合集整理
HTML
一款Jenkins的综合漏洞利用工具
Java CSS
Pentest Jenkins CI/CD
bounty collection
Shell Python Dockerfile Ruby JavaScript ASP.NET Classic ASP HTML PHP Jupyter Notebook
在公网收集的gobypoc+部分自己加的poc
List of awesome starred repositories
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2019-1003000 vulnerability anywhere in the article.
-
carnal0wnage.com
Jenkins - CVE-2018-1000600 PoC
second exploit from the blog post https://blog.orange.tw/2019/01/hacking-jenkins-part-1-play-with-dynamic-routing.html Chained with CVE-2018-1000600 to a Pre-auth Fully-responded SSRF https://jenkins. ... Read more
-
carnal0wnage.com
Jenkins - messing with exploits pt3 - CVE-2019-1003000
References: https://www.exploit-db.com/exploits/46453 http://blog.orange.tw/2019/02/abusing-meta-programming-for-unauthenticated-rce.html This post covers the Orange Tsai Jenkins pre-auth exploit Vuln ... Read more

-
carnal0wnage.com
Jenkins - SECURITY-180/CVE-2015-1814 PoC
Forced API token change SECURITY-180/CVE-2015-1814 Affected Versions All Jenkins releases <= 1.605 All LTS releases <= 1.596.1 PoC Tested against Jenkins 1.605 POST /user/user2/descriptorByName/jenkin ... Read more

-
carnal0wnage.com
Jenkins - SECURITY-200 / CVE-2015-5323 PoC
API tokens of other users available to admins SECURITY-200 / CVE-2015-5323 API tokens of other users were exposed to admins by default. On instances that don’t implicitly grant RunScripts permission t ... Read more
-
carnal0wnage.com
Jenkins Master Post
A collection of posts on attacking Jenkins http://www.labofapenetrationtester.com/2014/08/script-execution-and-privilege-esc-jenkins.html Manipulating build steps to get RCE https://medium.com/@uraniu ... Read more

-
carnal0wnage.com
Jenkins - messing with exploits pt2 - CVE-2019-1003000
After the release of Orange Tsai's exploit for Jenkins. I've been doing some poking. PreAuth RCE against Jenkins is something everyone wants. While not totally related to the blog post and tweet the f ... Read more

-
carnal0wnage.com
Jenkins - messing with new exploits pt1
Jenkins notes for: https://blog.orange.tw/2019/01/hacking-jenkins-part-1-play-with-dynamic-routing.html http://blog.orange.tw/2019/02/abusing-meta-programming-for-unauthenticated-rce.html to download ... Read more
-
carnal0wnage.com
Kubernetes: Master Post
I have a few Kubernetes posts queued up and will make this the master post to index and give references for the topic. If i'm missing blog posts or useful resources ping me here or twitter. Talks you ... Read more
The following table lists the changes that have been made to the
CVE-2019-1003000 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://packetstormsecurity.com/files/152132/Jenkins-ACL-Bypass-Metaprogramming-Remote-Code-Execution.html Added Reference http://www.rapid7.com/db/modules/exploit/multi/http/jenkins_metaprogramming Added Reference https://access.redhat.com/errata/RHBA-2019:0326 Added Reference https://access.redhat.com/errata/RHBA-2019:0327 Added Reference https://jenkins.io/security/advisory/2019-01-08/#SECURITY-1266 Added Reference https://www.exploit-db.com/exploits/46453/ Added Reference https://www.exploit-db.com/exploits/46572/ -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CVE Modified by [email protected]
Oct. 25, 2023
Action Type Old Value New Value Removed CWE Jenkins Project CWE-693 Removed CWE Reason CWE-693 / Outside of 1003 -
Modified Analysis by [email protected]
Sep. 29, 2020
Action Type Old Value New Value Removed CVSS V3 NIST AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Added CVSS V3.1 NIST AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Removed CWE NIST CWE-254 Added CWE NIST NVD-CWE-Other -
CVE Modified by [email protected]
Oct. 09, 2019
Action Type Old Value New Value Added CWE Jenkins Project CWE-693 -
CVE Modified by [email protected]
May. 17, 2019
Action Type Old Value New Value Changed Description A sandbox bypass vulnerability exists in Script Security Plugin 2.49 and earlier in src/main/java/org/jenkinsci/plugins/scriptsecurity/sandbox/groovy/GroovySandbox.java that allows attackers with the ability to provide sandboxed scripts to execute arbitrary code on the Jenkins master JVM. A sandbox bypass vulnerability exists in Script Security Plugin 1.49 and earlier in src/main/java/org/jenkinsci/plugins/scriptsecurity/sandbox/groovy/GroovySandbox.java that allows attackers with the ability to provide sandboxed scripts to execute arbitrary code on the Jenkins master JVM. -
Modified Analysis by [email protected]
Apr. 26, 2019
Action Type Old Value New Value Changed Reference Type https://www.exploit-db.com/exploits/46572/ No Types Assigned https://www.exploit-db.com/exploits/46572/ Exploit, Third Party Advisory, VDB Entry Changed Reference Type http://packetstormsecurity.com/files/152132/Jenkins-ACL-Bypass-Metaprogramming-Remote-Code-Execution.html No Types Assigned http://packetstormsecurity.com/files/152132/Jenkins-ACL-Bypass-Metaprogramming-Remote-Code-Execution.html Exploit, Third Party Advisory, VDB Entry Changed Reference Type https://access.redhat.com/errata/RHBA-2019:0327 No Types Assigned https://access.redhat.com/errata/RHBA-2019:0327 Third Party Advisory Changed Reference Type http://www.rapid7.com/db/modules/exploit/multi/http/jenkins_metaprogramming No Types Assigned http://www.rapid7.com/db/modules/exploit/multi/http/jenkins_metaprogramming Third Party Advisory -
CVE Modified by [email protected]
Apr. 24, 2019
Action Type Old Value New Value Added Reference https://access.redhat.com/errata/RHBA-2019:0327 [No Types Assigned] -
CVE Modified by [email protected]
Mar. 21, 2019
Action Type Old Value New Value Added Reference https://www.exploit-db.com/exploits/46572/ [No Types Assigned] Added Reference http://www.rapid7.com/db/modules/exploit/multi/http/jenkins_metaprogramming [No Types Assigned] Added Reference http://packetstormsecurity.com/files/152132/Jenkins-ACL-Bypass-Metaprogramming-Remote-Code-Execution.html [No Types Assigned] -
Modified Analysis by [email protected]
Mar. 14, 2019
Action Type Old Value New Value Changed Reference Type https://access.redhat.com/errata/RHBA-2019:0326 No Types Assigned https://access.redhat.com/errata/RHBA-2019:0326 Third Party Advisory Added CPE Configuration OR *cpe:2.3:a:redhat:openshift_container_platform:3.11:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Mar. 14, 2019
Action Type Old Value New Value Added Reference https://access.redhat.com/errata/RHBA-2019:0326 [No Types Assigned] -
Modified Analysis by [email protected]
Mar. 05, 2019
Action Type Old Value New Value Changed Reference Type https://www.exploit-db.com/exploits/46453/ No Types Assigned https://www.exploit-db.com/exploits/46453/ Exploit, Third Party Advisory, VDB Entry -
CVE Modified by [email protected]
Mar. 05, 2019
Action Type Old Value New Value Added Reference https://www.exploit-db.com/exploits/46453/ [No Types Assigned] -
Initial Analysis by [email protected]
Feb. 07, 2019
Action Type Old Value New Value Added CVSS V2 (AV:N/AC:L/Au:S/C:P/I:P/A:P) Added CVSS V3 AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://jenkins.io/security/advisory/2019-01-08/#SECURITY-1266 No Types Assigned https://jenkins.io/security/advisory/2019-01-08/#SECURITY-1266 Vendor Advisory Added CWE CWE-254 Added CPE Configuration OR *cpe:2.3:a:jenkins:script_security:*:*:*:*:*:jenkins:*:* versions up to (including) 1.49