CVE-2020-12271
Sophos SFOS SQL Injection Vulnerability - [Actively Exploited]
Description
A SQL injection issue was found in SFOS 17.0, 17.1, 17.5, and 18.0 before 2020-04-25 on Sophos XG Firewall devices, as exploited in the wild in April 2020. This affected devices configured with either the administration (HTTPS) service or the User Portal exposed on the WAN zone. A successful attack may have caused remote code execution that exfiltrated usernames and hashed passwords for the local device admin(s), portal admins, and user accounts used for remote access (but not external Active Directory or LDAP passwords)
INFO
Published Date :
April 27, 2020, 4:15 a.m.
Last Modified :
Nov. 7, 2025, 7:32 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Sophos Firewall operating system (SFOS) firmware contains a SQL injection vulnerability when configured with either the administration (HTTPS) service or the User Portal is exposed on the WAN zone. Successful exploitation may cause remote code execution to exfiltrate usernames and hashed passwords for the local device admin(s), portal admins, and user accounts used for remote access (but not external Active Directory or LDAP passwords).
Apply updates per vendor instructions.
Known Detected Nov 03, 2021
https://nvd.nist.gov/vuln/detail/CVE-2020-12271
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 2.0 | HIGH | [email protected] | ||||
| CVSS 3.0 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Refer to the vendor advisory
Public PoC/Exploit Available at Github
CVE-2020-12271 has a 8 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2020-12271.
| URL | Resource |
|---|---|
| https://community.sophos.com/kb/en-us/135412 | Vendor Advisory |
| https://cwe.mitre.org/data/definitions/89.html | Third Party Advisory |
| https://news.sophos.com/en-us/2020/04/26/asnarok/ | Exploit Vendor Advisory |
| https://community.sophos.com/kb/en-us/135412 | Vendor Advisory |
| https://cwe.mitre.org/data/definitions/89.html | Third Party Advisory |
| https://news.sophos.com/en-us/2020/04/26/asnarok/ | Exploit Vendor Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2020-12271 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2020-12271 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2020-12271
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Perimeter security exploitation framework — 164 modules covering FW, NGFW, UTM, WAF, VPN, NAC, LB, and OT/ICS firewalls (Fortinet, Cisco, Palo Alto, F5, Citrix, Check Point, SonicWall, Ivanti, Siemens, Moxa, +13 vendors). GPU-accelerated, ML-driven, async concurrency, Rich TUI.
exploitation-framework firewall ics-security ngfw ot-security penetration-testing pentest python red-team security-testing vpn-exploit vulnerability-scanner waf-bypass
Shell Makefile Python
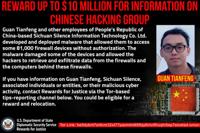
Salt Typhoon, APT41
Python
None
CSS HTML JavaScript
An automated repo to track Nuclei template scanning capabilities against the CISA KEV.
cisa-kev nuclei scanning vulnerabilities cisa
Makefile Python Shell
Resources for Security Matters talk 2022
Ostorlab KEV: One-command to detect most remotely known exploitable vulnerabilities. Sourced from CISA KEV, Google's Tsunami, Ostorlab's Asteroid and Bug Bounty programs.
cisa-kev vulnerability 0day cisa exploits
None
Python XSLT
essential templates for kenzer [DEPRECATED]
kenzer vulnerabilities kenzer-templates arpsyndicate
Python Shell Ruby
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2020-12271 vulnerability anywhere in the article.

-
Cybersecurity News
CVE-2024-9474 Exploited: LITTLELAMB.WOOLTEA Backdoor Discovered in Palo Alto Devices
Northwave Cyber Security has identified a sophisticated backdoor, LITTLELAMB.WOOLTEA, targeting Palo Alto Networks firewalls.The backdoor was uncovered during a forensic investigation into a compromis ... Read more

-
The Hacker News
Sophos Issues Hotfixes for Critical Firewall Flaws: Update to Prevent Exploitation
Firewall Security / Vulnerability Sophos has released hotfixes to address three security flaws in Sophos Firewall products that could be exploited to achieve remote code execution and allow privileged ... Read more

-
Cybersecurity News
336,000 Prometheus Servers at Risk: Urgent Security Alert
In a recent investigation, Aqua Nautilus uncovered alarming security vulnerabilities within the Prometheus ecosystem. Their research highlights critical flaws spanning information disclosure, denial-o ... Read more

-
Cybersecurity News
Abusing Microsoft’s UI Automation Framework: The New Evasion Technique Bypassing EDR
Akamai security researcher Tomer Peled has unveiled a novel attack technique exploiting Microsoft’s legacy UI Automation framework, a tool originally designed to enhance computer accessibility. The fi ... Read more

-
SentinelOne
The Good, the Bad and the Ugly in Cybersecurity – Week 50
The Good | Ragnarok Ransomware Operators & DDoS-For-Hire Servers Disrupted by LEAs Law enforcement agencies this week took decisive action to disrupt a Chinese firm for its involvement in a series of ... Read more

-
Cybersecurity News
Modular Java Backdoor Emerges in Cleo Exploitation Campaign (CVE-2024-50623)
Rapid7 Labs and its Managed Detection and Response (MDR) team uncovered a sophisticated modular Java-based Remote Access Trojan (RAT) deployed in a multi-stage attack targeting Cleo file transfer soft ... Read more

-
Cybersecurity News
$5 Million Reward Offered After Indictment of North Korean Cyber Operatives
A federal court in St. Louis, Missouri, has indicted 14 nationals of the Democratic People’s Republic of Korea (DPRK) for a series of long-running conspiracies involving sanctions violations, wire fra ... Read more

-
Hackread - Latest Cybersecurity, Tech, Crypto & Hacking News
US Sanctions Chinese Cybersecurity Firm for Firewall Exploit, Ransomware Attacks
SUMMARY Sanctions on Chinese Firm: The US sanctioned Sichuan Silence Information Technology and employee Guan Tianfeng for exploiting a firewall vulnerability in a major global cyberattack. Global Imp ... Read more
-
Cybersecurity News
CVE-2020-12271 Exploited: FBI Seeks Chinese Hacker Behind 81,000 Device Breach
The US Department of Justice announced the unsealing of an indictment against Guan Tianfeng, a Chinese national associated with Sichuan Silence Information Technology Co. Ltd., for his alleged role in ... Read more

-
Dark Reading
Chinese Hacker Pwns 81K Sophos Devices With Zero-Day Bug
Source: B Christopher via Alamy Stock PhotoNEWS BRIEFThe US government unsealed charges yesterday against a Chinese national who allegedly broke into approximately 81,000 of Sophos firewall devices ar ... Read more

-
The Hacker News
U.S. Charges Chinese Hacker for Exploiting Zero-Day in 81,000 Sophos Firewalls
The U.S. government on Tuesday unsealed charges against a Chinese national for allegedly breaking into thousands of Sophos firewall devices globally in 2020. Guan Tianfeng (aka gbigmao and gxiaomao), ... Read more

-
The Register
US names Chinese national it alleges was behind 2020 attack on Sophos firewalls
The US Departments of Treasury and Justice have named a Chinese business and one of its employees as the actors behind the 2020 exploit of a zero-day flaw in Sophos firewalls The attack was made possi ... Read more

-
Cybersecurity News
Ivanti Connect Secure and Policy Secure Updates Address Critical Vulnerabilities
Ivanti, a leader in unified endpoint and enterprise service management, has issued patches for several high and critical vulnerabilities affecting its Connect Secure and Policy Secure solutions. These ... Read more

-
Cybersecurity News
CVE-2024-52335 (CVSS 9.8): Siemens Healthineers Addresses Critical Flaw in Medical Imaging Software
Siemens Healthineers has released a critical security update to address an unauthenticated SQL injection vulnerability in its syngo.plaza VB30E medical imaging software. The vulnerability, identified ... Read more

-
Cybersecurity News
Google Chrome Patches High-Severity Vulnerabilities – CVE-2024-12381 & CVE-2024-12382
Google has announced its Chrome browser’s latest stable channel update, addressing several security vulnerabilities, including two classified as “High” severity. The update, rolling out progressively ... Read more

-
BleepingComputer
US sanctions Chinese firm for hacking firewalls in ransomware attacks
The U.S. Treasury Department has sanctioned Chinese cybersecurity company Sichuan Silence and one of its employees for their involvement in a series of Ragnarok ransomware attacks targeting U.S. criti ... Read more

-
Cybersecurity News
Beware of Celestial Stealer: New MaaS Targets Browsers and Crypto Wallets
A new report from Trellix Advanced Research Center has exposed the inner workings of Celestial Stealer, a sophisticated Malware-as-a-Service (MaaS) platform targeting developers, gamers, and cryptocur ... Read more

-
Cybersecurity News
Google Chrome Addresses High-Severity Flaw in V8 JavaScript Engine (CVE-2024-12053)
Google has released a security update for its Chrome web browser to mitigate a high-severity “type confusion” vulnerability (CVE-2024-12053) residing within the V8 JavaScript engine. This vulnerabilit ... Read more

-
The Hacker News
FBI Seeks Public Help to Identify Chinese Hackers Behind Global Cyber Intrusions
The U.S. Federal Bureau of Investigation (FBI) has sought assistance from the public in connection with an investigation involving the breach of edge devices and computer networks belonging to compani ... Read more

-
security.nl
FBI vraagt publiek om informatie over misbruik van lek in Sophos-firewalls
De FBI heeft het publiek om informatie gevraagd over personen die achter misbruik van een kritieke kwetsbaarheid in de firewalls van securitybedrijf Sophos zitten. Bedrijven en organisaties met een So ... Read more
The following table lists the changes that have been made to the
CVE-2020-12271 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Nov. 07, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2020-12271 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 22, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2020-12271 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2020-12271 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2020-12271 -
Modified Analysis by [email protected]
Apr. 03, 2025
Action Type Old Value New Value -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Feb. 04, 2025
Action Type Old Value New Value Added CWE CWE-89 -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://community.sophos.com/kb/en-us/135412 Added Reference https://cwe.mitre.org/data/definitions/89.html Added Reference https://news.sophos.com/en-us/2020/04/26/asnarok/ -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
Modified Analysis by [email protected]
Oct. 05, 2022
Action Type Old Value New Value Changed Reference Type https://cwe.mitre.org/data/definitions/89.html No Types Assigned https://cwe.mitre.org/data/definitions/89.html Third Party Advisory -
CVE Modified by [email protected]
Jul. 10, 2022
Action Type Old Value New Value Added Reference https://cwe.mitre.org/data/definitions/89.html [No Types Assigned] -
Initial Analysis by [email protected]
May. 01, 2020
Action Type Old Value New Value Added CVSS V2 NIST (AV:N/AC:L/Au:N/C:P/I:P/A:P) Added CVSS V3 MITRE AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://community.sophos.com/kb/en-us/135412 No Types Assigned https://community.sophos.com/kb/en-us/135412 Vendor Advisory Changed Reference Type https://news.sophos.com/en-us/2020/04/26/asnarok/ No Types Assigned https://news.sophos.com/en-us/2020/04/26/asnarok/ Exploit, Vendor Advisory Added CWE NIST CWE-89 Added CPE Configuration AND OR *cpe:2.3:o:sophos:sfos:17.0:*:*:*:*:*:*:* *cpe:2.3:o:sophos:sfos:17.1:*:*:*:*:*:*:* *cpe:2.3:o:sophos:sfos:17.5:*:*:*:*:*:*:* *cpe:2.3:o:sophos:sfos:18.0:*:*:*:*:*:*:* OR cpe:2.3:h:sophos:xg_firewall:-:*:*:*:*:*:*:* -
Initial Analysis by [email protected]
May. 01, 2020
Action Type Old Value New Value Added CVSS V2 NIST (AV:N/AC:L/Au:N/C:P/I:P/A:P) Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://community.sophos.com/kb/en-us/135412 No Types Assigned https://community.sophos.com/kb/en-us/135412 Vendor Advisory Changed Reference Type https://news.sophos.com/en-us/2020/04/26/asnarok/ No Types Assigned https://news.sophos.com/en-us/2020/04/26/asnarok/ Exploit, Vendor Advisory Added CWE NIST CWE-89 Added CPE Configuration AND OR *cpe:2.3:o:sophos:sfos:17.0:*:*:*:*:*:*:* *cpe:2.3:o:sophos:sfos:17.1:*:*:*:*:*:*:* *cpe:2.3:o:sophos:sfos:17.5:*:*:*:*:*:*:* *cpe:2.3:o:sophos:sfos:18.0:*:*:*:*:*:*:* OR cpe:2.3:h:sophos:xg_firewall:-:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Apr. 27, 2020
Action Type Old Value New Value Changed Description A SQL injection issue was found in SFOS 17.0, 17.1, 17.5, and 18.0 before 2020-04-25 on Sophos XG Firewall devices, as exploited in the wild in April 2020 for remote code execution. This affected devices configured with either the administration (HTTPS) service or the User Portal exposed on the WAN zone. A successful attack may have exfiltrated usernames and hashed passwords for the local device admin(s), portal admins, and user accounts used for remote access (but not external Active Directory or LDAP passwords). A SQL injection issue was found in SFOS 17.0, 17.1, 17.5, and 18.0 before 2020-04-25 on Sophos XG Firewall devices, as exploited in the wild in April 2020. This affected devices configured with either the administration (HTTPS) service or the User Portal exposed on the WAN zone. A successful attack may have caused remote code execution that exfiltrated usernames and hashed passwords for the local device admin(s), portal admins, and user accounts used for remote access (but not external Active Directory or LDAP passwords) -
CVE Modified by [email protected]
Apr. 27, 2020
Action Type Old Value New Value Changed Description A SQL injection issue was found in SFOS 17.0, 17.1, 17.5, and 18.0 before 2020-04-25 on Sophos XG Firewall devices, as exploited in the wild in April 2020. This affected devices configured with either the administration (HTTPS) service or the User Portal exposed on the WAN zone. A successful attack may have exfiltrated usernames and hashed passwords for the local device admin(s), portal admins, and user accounts used for remote access (but not external Active Directory or LDAP passwords). A SQL injection issue was found in SFOS 17.0, 17.1, 17.5, and 18.0 before 2020-04-25 on Sophos XG Firewall devices, as exploited in the wild in April 2020 for remote code execution. This affected devices configured with either the administration (HTTPS) service or the User Portal exposed on the WAN zone. A successful attack may have exfiltrated usernames and hashed passwords for the local device admin(s), portal admins, and user accounts used for remote access (but not external Active Directory or LDAP passwords).