CVE-2020-14883
Oracle WebLogic Server Unspecified Vulnerability - [Actively Exploited]
Description
Vulnerability in the Oracle WebLogic Server product of Oracle Fusion Middleware (component: Console). Supported versions that are affected are 10.3.6.0.0, 12.1.3.0.0, 12.2.1.3.0, 12.2.1.4.0 and 14.1.1.0.0. Easily exploitable vulnerability allows high privileged attacker with network access via HTTP to compromise Oracle WebLogic Server. Successful attacks of this vulnerability can result in takeover of Oracle WebLogic Server. CVSS 3.1 Base Score 7.2 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H).
INFO
Published Date :
Oct. 21, 2020, 3:15 p.m.
Last Modified :
Oct. 27, 2025, 5:09 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Oracle WebLogic Server contains an unspecified vulnerability in the Console component with high impacts to confidentilaity, integrity, and availability.
Apply updates per vendor instructions.
Unknown
https://nvd.nist.gov/vuln/detail/CVE-2020-14883
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 2.0 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Apply the appropriate patch according to the October 2020 Oracle Critical Patch Update advisory and the Oracle Security Alert advisory for CVE-2020-14750.
Public PoC/Exploit Available at Github
CVE-2020-14883 has a 58 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2020-14883.
| URL | Resource |
|---|---|
| http://packetstormsecurity.com/files/160143/Oracle-WebLogic-Server-Administration-Console-Handle-Remote-Code-Execution.html | Third Party Advisory VDB Entry |
| https://www.oracle.com/security-alerts/cpuoct2020.html | Vendor Advisory |
| http://packetstormsecurity.com/files/160143/Oracle-WebLogic-Server-Administration-Console-Handle-Remote-Code-Execution.html | Third Party Advisory VDB Entry |
| https://www.oracle.com/security-alerts/cpuoct2020.html | Vendor Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2020-14883 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2020-14883 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2020-14883
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
这是一个Vulfocus靶场的Exploit库,致力于快速flag获取。提供30+一键获取flag脚本,强大易用的Python 渗透工具集。
ctf ctf-tools cve exploit pentest rce red-team security-tools vulfocus flag
Python JavaScript Shell Java HTML C Batchfile
None
Python JavaScript Shell Dockerfile HTML
PoC for testing if a target is vulnerable to RCE
Shell
CVE-2020-14883
None
This is my starred repositories including the description for each tool. Makes search/filter over them easier.
None
HTML Python Shell
A curated collection of Proof of Concept (PoC) tools, scripts, and techniques designed for red team operations, penetration testing, and cybersecurity research. This repository focuses on providing practical resources for exploring vulnerabilities
attack cybersecurity exp hw penetration-testing poc red-team security-tools vulnerability-poc
中间件的exp
cm楚门加速器:app下载官网优惠码
Conducted a theoretical penetration test involving reconnaissance, vulnerability scanning, remediation, and documentation. Delivered a 15+ page technical report and 2-page executive summary. Utilized tools such as Nmap, Nessus, Netcat, OpenVAS, BurpSuite, and Wapiti.
NKU-COSC0030-实习实训
Python Dockerfile
oracle weblogic
Python
网络安全相关工具和文章链接总结
None
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2020-14883 vulnerability anywhere in the article.

-
CybersecurityNews
Hackers Actively Exploiting Critical WebLogic RCE Vulnerabilities in Attacks
A recent cybersecurity study reveals that threat actors are moving faster than ever to weaponize new software flaws. According to data collected from a high-interaction honeypot, hackers are actively ... Read more

-
AttackIQ
Emulating the Surging Hadooken Malware
On September 12, 2024, AquaSec reported the identification of a new Linux-based malware during an intrusion chain that abused misconfigurations on public-facing Oracle Weblogic Servers. Days later, on ... Read more
-
Cybersecurity News
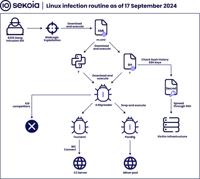
Hadooken & K4Spreader Malware: 8220 Gang’s Latest Cloud Hijacking Tools
Linux infection routine | Image: Sekoia’s Threat Detection & Research (TDR) teamThe notorious 8220 Gang, a China-based intrusion set first identified in 2018, continues to expand its arsenal with two ... Read more
The following table lists the changes that have been made to the
CVE-2020-14883 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 27, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2020-14883 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 22, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2020-14883 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2020-14883 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2020-14883 -
Modified Analysis by [email protected]
Feb. 07, 2025
Action Type Old Value New Value -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://packetstormsecurity.com/files/160143/Oracle-WebLogic-Server-Administration-Console-Handle-Remote-Code-Execution.html Added Reference https://www.oracle.com/security-alerts/cpuoct2020.html -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CWE Remap by [email protected]
Jul. 12, 2022
Action Type Old Value New Value Changed CWE NVD-CWE-noinfo NVD-CWE-Other -
Modified Analysis by [email protected]
Jul. 01, 2022
Action Type Old Value New Value Changed Reference Type http://packetstormsecurity.com/files/160143/Oracle-WebLogic-Server-Administration-Console-Handle-Remote-Code-Execution.html No Types Assigned http://packetstormsecurity.com/files/160143/Oracle-WebLogic-Server-Administration-Console-Handle-Remote-Code-Execution.html Third Party Advisory, VDB Entry -
CVE Modified by [email protected]
Nov. 19, 2020
Action Type Old Value New Value Added Reference http://packetstormsecurity.com/files/160143/Oracle-WebLogic-Server-Administration-Console-Handle-Remote-Code-Execution.html [No Types Assigned] -
Initial Analysis by [email protected]
Oct. 26, 2020
Action Type Old Value New Value Added CVSS V2 NIST (AV:N/AC:L/Au:S/C:C/I:C/A:C) Changed Reference Type https://www.oracle.com/security-alerts/cpuoct2020.html No Types Assigned https://www.oracle.com/security-alerts/cpuoct2020.html Vendor Advisory Added CWE NIST NVD-CWE-noinfo Added CPE Configuration OR *cpe:2.3:a:oracle:weblogic_server:10.3.6.0.0:*:*:*:*:*:*:* *cpe:2.3:a:oracle:weblogic_server:12.1.3.0.0:*:*:*:*:*:*:* *cpe:2.3:a:oracle:weblogic_server:12.2.1.3.0:*:*:*:*:*:*:* *cpe:2.3:a:oracle:weblogic_server:12.2.1.4.0:*:*:*:*:*:*:* *cpe:2.3:a:oracle:weblogic_server:14.1.1.0.0:*:*:*:*:*:*:*