CVE-2021-21311
Adminer Server-Side Request Forgery Vulnerability - [Actively Exploited]
Description
Adminer is an open-source database management in a single PHP file. In adminer from version 4.0.0 and before 4.7.9 there is a server-side request forgery vulnerability. Users of Adminer versions bundling all drivers (e.g. `adminer.php`) are affected. This is fixed in version 4.7.9.
INFO
Published Date :
Feb. 11, 2021, 9:15 p.m.
Last Modified :
Oct. 24, 2025, 2:48 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Adminer contains a server-side request forgery vulnerability that, when exploited, allows a remote attacker to obtain potentially sensitive information.
Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable.
Unknown
https://github.com/vrana/adminer/security/advisories/GHSA-x5r2-hj5c-8jx6 ; https://nvd.nist.gov/vuln/detail/CVE-2021-21311
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 2.0 | MEDIUM | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Upgrade Adminer to version 4.7.9 or later.
- Update the Adminer package.
Public PoC/Exploit Available at Github
CVE-2021-21311 has a 28 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2021-21311.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2021-21311 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2021-21311
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
A secure, zero-trust database management tool for WordPress. Fixes critical SSRF vulnerabilities (CVE-2021-21311) by enforcing local connections only.
adminer adminer-plugin cve-2021-21311
PHP CSS JavaScript
None
Dockerfile Python CSS HTML
管理Vulhub漏洞,支持添加新的漏洞,当前管理器只包含78个漏洞环境,并不包含所有的Vulhub环境,如果添加新的漏洞环境。
Python PHP Dockerfile Perl Shell Java CSS C JavaScript Batchfile
None
None
This thesis project focuses on the creation of an autonomous agent that is capable of understanding CVE description and create from its interpretation a vulnerable Docker container, which can then be used to gather attack patterns data. The Docker creation process is benchmarked in order to understand how well the agent is performing its tasks.
Dockerfile HTML Python Shell Groovy PHP Java SaltStack JavaScript CSS
此次更新共包含1314个自定义gobypoc,是否含有后门和重复自行判断,如果无红队版,可直接poc管理处导入自定义poc即可,共计1314个。
A curated collection of Proof of Concept (PoC) tools, scripts, and techniques designed for red team operations, penetration testing, and cybersecurity research. This repository focuses on providing practical resources for exploring vulnerabilities
attack cybersecurity exp hw penetration-testing poc red-team security-tools vulnerability-poc
这是一个每天同步Vulnerability-Wiki中docs-base中内容的项目
HTML
None
Dockerfile Python CSS HTML Shell Java Groovy Jupyter Notebook
All CVE - PoC in GitHub
poc proofofconcept tester allcve cvegithub cvenew cvepoc cveupdate
None
None
CSS HTML JavaScript
None
在公网收集的gobypoc+部分自己加的poc
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2021-21311 vulnerability anywhere in the article.

-
The Cyber Express
Hackers Exploited Cisco SD-WAN Zero-Day for Three Years Before Detection
Cisco Talos disclosed that a highly sophisticated threat actor exploited a critical authentication bypass vulnerability in Cisco SD-WAN infrastructure for at least three years before security research ... Read more

-
The Cyber Express
The Power of Two: Why MFA Matters More Than Ever
In a world where passwords are stolen, phished, or guessed every second, multifactor authentication (MFA) has quietly become one of the most effective shields against cyberattacks. Whether you call it ... Read more

-
The Cyber Express
Japan’s Beer Taps Fear Running Dry as Cyberattack on Asahi Disrupts Production
Japan’s largest brewery, Asahi Group Holdings, is racing against time as it struggles to recover from a cyberattack that has severely disrupted its operations. The Asahi cyberattack, which was first r ... Read more

-
The Cyber Express
Your Easiest Fix: The 3 Golden Rules for a Password that AI Can’t Crack
October is here, and Cybersecurity Awareness Month 2025 is about to come into being. Department of Homeland Security (DHS) and CISA have initiated this year’s campaign with the theme of ‘Building our ... Read more
-
The Cyber Express
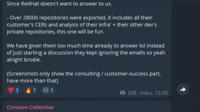
Hackers Claim Breach of Red Hat Customer Data
Hackers claim to have breached a Red Hat GitHub instance and stolen sensitive customer data. The claims were made in Telegram posts by a group calling itself “Crimson Collective,” which said it exfilt ... Read more

-
The Cyber Express
New VMware Vulnerability CVE-2025-41244 Actively Exploited Since October 2024
A newly listed VMware zero-day vulnerability has been actively exploited by Chinese state-sponsored threat actors for almost a year, according to security researchers. The vulnerability, CVE-2025-4124 ... Read more

-
TheCyberThrone
CISA Adds Five Actively Exploited Vulnerabilities to KEV Catalog
September 30, 2025The threat landscape continues to evolve rapidly and staying ahead of actively exploited vulnerabilities is key to effective cybersecurity defense. On September 28, 2025, the Cyberse ... Read more

-
The Cyber Express
Apple Security Update Addresses Critical Font Parser Vulnerability Across Multiple Platforms
Apple has rolled out a series of important security updates across multiple platforms, addressing a vulnerability affecting the system font parser. These Apple security updates cover iOS, iPadOS, macO ... Read more

-
The Cyber Express
CISA Adds Five Actively Exploited Vulnerabilities to KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has expanded its Known Exploited Vulnerabilities (KEV) Catalog by adding five new security flaws that are confirmed to be under active ... Read more

-
The Hacker News
CISA Sounds Alarm on Critical Sudo Flaw Actively Exploited in Linux and Unix Systems
Sep 30, 2025Ravie LakshmananVulnerability / Linux The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a critical security flaw impacting the Sudo command-line utility fo ... Read more
The following table lists the changes that have been made to the
CVE-2021-21311 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 24, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2021-21311 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 22, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2021-21311 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2021-21311 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2021-21311 -
Modified Analysis by [email protected]
Sep. 30, 2025
Action Type Old Value New Value Changed Reference Type CVE: https://github.com/vrana/adminer/commit/ccd2374b0b12bd547417bf0dacdf153826c83351 Types: Patch, Third Party Advisory CVE: https://github.com/vrana/adminer/commit/ccd2374b0b12bd547417bf0dacdf153826c83351 Types: Patch Changed Reference Type GitHub, Inc.: https://github.com/vrana/adminer/commit/ccd2374b0b12bd547417bf0dacdf153826c83351 Types: Patch, Third Party Advisory GitHub, Inc.: https://github.com/vrana/adminer/commit/ccd2374b0b12bd547417bf0dacdf153826c83351 Types: Patch -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Sep. 30, 2025
Action Type Old Value New Value Added Date Added 2025-09-29 Added Due Date 2025-10-20 Added Vulnerability Name Adminer Server-Side Request Forgery Vulnerability Added Required Action Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable. -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://github.com/vrana/adminer/commit/ccd2374b0b12bd547417bf0dacdf153826c83351 Added Reference https://github.com/vrana/adminer/files/5957311/Adminer.SSRF.pdf Added Reference https://github.com/vrana/adminer/security/advisories/GHSA-x5r2-hj5c-8jx6 Added Reference https://lists.debian.org/debian-lts-announce/2021/03/msg00002.html Added Reference https://packagist.org/packages/vrana/adminer -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
Reanalysis by [email protected]
Jun. 24, 2021
Action Type Old Value New Value Changed Reference Type https://packagist.org/packages/vrana/adminer Product https://packagist.org/packages/vrana/adminer Product, Third Party Advisory Changed CPE Configuration OR *cpe:2.3:a:adminer:adminer:*:*:*:*:*:*:*:* versions from (including) 4.0.0 up to (including) 4.7.9 OR *cpe:2.3:a:adminer:adminer:*:*:*:*:*:*:*:* versions from (including) 4.0.0 up to (excluding) 4.7.9 -
Modified Analysis by [email protected]
Mar. 15, 2021
Action Type Old Value New Value Changed Reference Type https://lists.debian.org/debian-lts-announce/2021/03/msg00002.html No Types Assigned https://lists.debian.org/debian-lts-announce/2021/03/msg00002.html Mailing List, Third Party Advisory Added CPE Configuration OR *cpe:2.3:o:debian:debian_linux:9.0:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Mar. 02, 2021
Action Type Old Value New Value Added Reference https://lists.debian.org/debian-lts-announce/2021/03/msg00002.html [No Types Assigned] -
Initial Analysis by [email protected]
Feb. 18, 2021
Action Type Old Value New Value Added CVSS V2 NIST (AV:N/AC:L/Au:N/C:P/I:P/A:N) Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:C/C:L/I:L/A:N Changed Reference Type https://github.com/vrana/adminer/commit/ccd2374b0b12bd547417bf0dacdf153826c83351 No Types Assigned https://github.com/vrana/adminer/commit/ccd2374b0b12bd547417bf0dacdf153826c83351 Patch, Third Party Advisory Changed Reference Type https://github.com/vrana/adminer/files/5957311/Adminer.SSRF.pdf No Types Assigned https://github.com/vrana/adminer/files/5957311/Adminer.SSRF.pdf Exploit, Third Party Advisory Changed Reference Type https://github.com/vrana/adminer/security/advisories/GHSA-x5r2-hj5c-8jx6 No Types Assigned https://github.com/vrana/adminer/security/advisories/GHSA-x5r2-hj5c-8jx6 Patch, Third Party Advisory Changed Reference Type https://packagist.org/packages/vrana/adminer No Types Assigned https://packagist.org/packages/vrana/adminer Product Added CPE Configuration OR *cpe:2.3:a:adminer:adminer:*:*:*:*:*:*:*:* versions from (including) 4.0.0 up to (including) 4.7.9