CVE-2022-3075
Google Chromium Mojo Insufficient Data Validation Vulnerability - [Actively Exploited]
Description
Insufficient data validation in Mojo in Google Chrome prior to 105.0.5195.102 allowed a remote attacker who had compromised the renderer process to potentially perform a sandbox escape via a crafted HTML page.
INFO
Published Date :
Sept. 26, 2022, 4:15 p.m.
Last Modified :
Oct. 24, 2025, 2:10 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Google Chromium Mojo contains an insufficient data validation vulnerability that allows a remote attacker, who has compromised the renderer process, to potentially perform a sandbox escape via a crafted HTML page. This vulnerability could affect multiple web browsers that utilize Chromium, including, but not limited to, Google Chrome, Microsoft Edge, and Opera.
Apply updates per vendor instructions.
Unknown
https://chromereleases.googleblog.com/2022/09/stable-channel-update-for-desktop.html, https://msrc.microsoft.com/update-guide/vulnerability/CVE-2022-3075; https://nvd.nist.gov/vuln/detail/CVE-2022-3075
Affected Products
The following products are affected by CVE-2022-3075
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Upgrade to the latest version of Chrome, Edge, or Opera.
- Update the affected chromedriver and/or chromium packages.
Public PoC/Exploit Available at Github
CVE-2022-3075 has a 4 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2022-3075.
| URL | Resource |
|---|---|
| https://chromereleases.googleblog.com/2022/09/stable-channel-update-for-desktop.html | Release Notes Vendor Advisory |
| https://crbug.com/1358134 | Permissions Required |
| https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ | Third Party Advisory |
| https://security.gentoo.org/glsa/202209-23 | Third Party Advisory |
| https://chromereleases.googleblog.com/2022/09/stable-channel-update-for-desktop.html | Release Notes Vendor Advisory |
| https://crbug.com/1358134 | Permissions Required |
| https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ | Third Party Advisory |
| https://security.gentoo.org/glsa/202209-23 | Third Party Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2022-3075 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2022-3075 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2022-3075
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Research browsers
Research browsers
JavaScript HTML
Research browser
JavaScript HTML
Ostorlab KEV: One-command to detect most remotely known exploitable vulnerabilities. Sourced from CISA KEV, Google's Tsunami, Ostorlab's Asteroid and Bug Bounty programs.
cisa-kev vulnerability 0day cisa exploits
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2022-3075 vulnerability anywhere in the article.

-
Daily CyberSecurity
Google’s Chrome Browser Faces an Uncertain Future: Perplexity AI Makes a Bid
At present, U.S. antitrust regulators are pressuring Google to divest its Chrome browser as a remedy for its search monopoly—a move that would constitute a monumental setback for the company, which is ... Read more

-
Daily CyberSecurity
Google Proposes New Browser Security: Your Local Network, Your Permission!
A Google engineer recently published a proposal on GitHub recommending that websites be restricted from accessing devices on a local network through browsers such as Chrome—except in cases where the u ... Read more

-
Daily CyberSecurity
Critical SSRF Vulnerability Patched in LNbits Lightning Wallet Server
LNbits, the modular and extendable Lightning Network wallet server, has patched a critical Server-Side Request Forgery (SSRF) vulnerability that exposed internal services to potential exploitation via ... Read more

-
Daily CyberSecurity
High-Severity XXE Vulnerability Found in NAKIVO Backup & Replication
A high-severity security vulnerability has been identified in NAKIVO Backup & Replication, a popular data protection solution. The vulnerability, classified as an XML External Entity (XXE) issue and t ... Read more

-
Daily CyberSecurity
Critical Vulnerabilities: CISA Alerts to Windows CLFS and Gladinet CentreStack Threats
Recently, the Cybersecurity and Infrastructure Security Agency (CISA) added two significant vulnerabilities to its Known Exploited Vulnerabilities Catalog, highlighting the urgency for users to apply ... Read more

-
Daily CyberSecurity
Windows CLFS Zero-Day Exploited to Deploy Ransomware
Microsoft Threat Intelligence has disclosed active exploitation of a zero-day vulnerability in the Windows Common Log File System (CLFS), tracked as CVE-2025-29824. The exploit, used in the wild, enab ... Read more

-
Daily CyberSecurity
Siemens Security Alert: Critical Vulnerabilities in SENTRON 7KT PAC1260 Data Manager
In a recent security advisory, Siemens ProductCERT has revealed multiple critical vulnerabilities affecting the SENTRON 7KT PAC1260 Data Manager. The advisory, published on April 8, 2025, warns that t ... Read more

-
Daily CyberSecurity
Kibana Code Injection Vulnerability: Prototype Pollution Threat (CVE-2024-12556)
A newly disclosed vulnerability in Kibana, the popular open-source data visualization front-end for Elasticsearch, has been rated CVSS 8.7 due to its potential to allow remote code injection under spe ... Read more

-
Daily CyberSecurity
Chrome Update Fixes High-Severity “Use After Free” Vulnerability
The Chrome Stable channel has been updated to version 135.0.7049.84/.85 for Windows and Mac, and to 135.0.7049.84 for Linux. This update will be rolling out to users over the coming days and weeks. Th ... Read more

-
Daily CyberSecurity
Microsoft April 2025 Patch Tuesday: Critical Security Updates and Zero-Day Exploits
This April, Microsoft’s Patch Tuesday release addresses a significant number of vulnerabilities, highlighting the ever-present need for robust cybersecurity practices. The tech giant rolled out fixes ... Read more

-
Daily CyberSecurity
Apache mod_auth_openidc Vulnerability Exposes Protected Content
In a recently published security advisory, OpenIDC has revealed a vulnerability in mod_auth_openidc, the widely used OpenID Connect module for the Apache HTTP server. The flaw, tracked as CVE-2025-314 ... Read more

-
Daily CyberSecurity
Fortinet: Critical Unverified Password Change Flaw in FortiSwitch
Fortinet has released a security advisory addressing a critical vulnerability in FortiSwitch products. The vulnerability, identified as CVE-2024-48887 (CVSS 9.3), could allow attackers to gain unautho ... Read more

-
Daily CyberSecurity
Siemens Industrial Edge: Critical Authentication Flaw (CVE-2024-54092)
Siemens has issued security advisories SSA-634640 and SSA-819629 to address a weak authentication vulnerability affecting its Industrial Edge Devices and Industrial Edge Device Kit. The vulnerability, ... Read more
-
Daily CyberSecurity
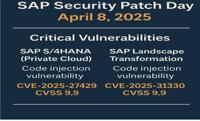
SAP April 2025 Patch Day: Critical Code Injection Risks
The SAP Security Patch Day on April 8, 2025, brought a wave of critical security updates, with a total of 18 new Security Notes and 2 updates to previously released notes. Among the fixes, several add ... Read more

-
Cybersecurity News
“Glic”: Google Chrome to Get Gemini Live Integration
Developers have discovered that Google appears to be planning the integration of the Gemini Live system into Chrome. This revelation comes from an X user known as Leopeva64, who delved into the Chromi ... Read more

-
Cybersecurity News
Apache Roller Patches CSRF Flaw CVE-2024-46911 in Latest Update
The Apache Software Foundation has released a security update for Apache Roller, a popular Java-based blogging platform. This update addresses a critical Cross-site Request Forgery (CSRF) vulnerabilit ... Read more

-
Cybersecurity News
Save uBlock Origin: How to Bypass Google’s Chrome Update and Extend Support
Google Chrome has begun automatically detecting and warning users on the extensions page that Manifest v2-based extensions are nearing deprecation. Although these extensions have not yet been fully di ... Read more
The following table lists the changes that have been made to the
CVE-2022-3075 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 24, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2022-3075 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 22, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2022-3075 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2022-3075 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2022-3075 -
Modified Analysis by [email protected]
Jul. 30, 2025
Action Type Old Value New Value -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Jul. 30, 2025
Action Type Old Value New Value Removed CWE CWE-20 -
Modified Analysis by [email protected]
Mar. 06, 2025
Action Type Old Value New Value Changed Reference Type CVE: https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ Types: Broken Link CVE: https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ Types: Third Party Advisory Changed Reference Type Chrome: https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ Types: Broken Link Chrome: https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ Types: Third Party Advisory -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Feb. 03, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H Added CWE CWE-20 -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://chromereleases.googleblog.com/2022/09/stable-channel-update-for-desktop.html Added Reference https://crbug.com/1358134 Added Reference https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ Added Reference https://security.gentoo.org/glsa/202209-23 -
Modified Analysis by [email protected]
Jun. 28, 2024
Action Type Old Value New Value Changed Reference Type https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ No Types Assigned https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ Broken Link -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Feb. 15, 2024
Action Type Old Value New Value Changed Vulnerability Name Google Chromium Insufficient Data Validation Vulnerability Google Chromium Mojo Insufficient Data Validation Vulnerability -
CVE Modified by [email protected]
Nov. 07, 2023
Action Type Old Value New Value Added Reference Chrome https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ [No types assigned] Removed Reference Chrome https://lists.fedoraproject.org/archives/list/[email protected]/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ -
Modified Analysis by [email protected]
Oct. 27, 2022
Action Type Old Value New Value Changed Reference Type https://lists.fedoraproject.org/archives/list/[email protected]/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ No Types Assigned https://lists.fedoraproject.org/archives/list/[email protected]/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ Mailing List, Third Party Advisory Added CPE Configuration OR *cpe:2.3:o:fedoraproject:fedora:37:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Oct. 03, 2022
Action Type Old Value New Value Added Reference https://lists.fedoraproject.org/archives/list/[email protected]/message/T4NMJURTG5RO3TGD7ZMIQ6Z4ZZ3SAVYE/ [No Types Assigned] -
Initial Analysis by [email protected]
Sep. 30, 2022
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H Changed Reference Type https://chromereleases.googleblog.com/2022/09/stable-channel-update-for-desktop.html No Types Assigned https://chromereleases.googleblog.com/2022/09/stable-channel-update-for-desktop.html Release Notes, Vendor Advisory Changed Reference Type https://crbug.com/1358134 No Types Assigned https://crbug.com/1358134 Permissions Required Changed Reference Type https://security.gentoo.org/glsa/202209-23 No Types Assigned https://security.gentoo.org/glsa/202209-23 Third Party Advisory Added CWE NIST CWE-20 Added CPE Configuration OR *cpe:2.3:a:google:chrome:*:*:*:*:*:*:*:* versions up to (excluding) 105.0.5195.102 -
CVE Modified by [email protected]
Sep. 29, 2022
Action Type Old Value New Value Added Reference https://security.gentoo.org/glsa/202209-23 [No Types Assigned]