CVE-2023-4295
Mali GPU Kernel Driver allows improper GPU memory processing operations
Description
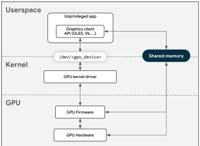
A local non-privileged user can make improper GPU memory processing operations to gain access to already freed memory.
INFO
Published Date :
Nov. 7, 2023, 4:15 p.m.
Last Modified :
March 24, 2025, 4:15 p.m.
Remotely Exploit :
No
Source :
[email protected]
Affected Products
The following products are affected by CVE-2023-4295
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Public PoC/Exploit Available at Github
CVE-2023-4295 has a 2 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2023-4295.
| URL | Resource |
|---|---|
| http://packetstormsecurity.com/files/176109/Arm-Mali-CSF-Overflow-Use-After-Free.html | Third Party Advisory |
| https://developer.arm.com/Arm%20Security%20Center/Mali%20GPU%20Driver%20Vulnerabilities | Vendor Advisory |
| http://packetstormsecurity.com/files/176109/Arm-Mali-CSF-Overflow-Use-After-Free.html | Third Party Advisory |
| https://developer.arm.com/Arm%20Security%20Center/Mali%20GPU%20Driver%20Vulnerabilities | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2023-4295 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2023-4295
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Arm mali open source drivers
Makefile C Assembly Starlark
A Huge Learning Resources with Labs For Offensive Security Players
api infrastructure learning security mobile web hack hacking owasp cybersecurity web-security mobile-security offensive offensive-security red-team owasp-top-10 redteam cloud-security api-security red-teaming
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2023-4295 vulnerability anywhere in the article.
-
Google Online Security Blog
Google & Arm - Raising The Bar on GPU Security
Posted by Xuan Xing, Eugene Rodionov, Jon Bottarini, Adam Bacchus - Android Red Team; Amit Chaudhary, Lyndon Fawcett, Joseph Artgole - Arm Product Security Team Who cares about GPUs? You, me, and the ... Read more
The following table lists the changes that have been made to the
CVE-2023-4295 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Mar. 24, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H -
CVE Modified by [email protected]
Feb. 13, 2025
Action Type Old Value New Value Changed Description A local non-privileged user can make improper GPU memory processing operations to gain access to already freed memory. A local non-privileged user can make improper GPU memory processing operations to gain access to already freed memory. -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://packetstormsecurity.com/files/176109/Arm-Mali-CSF-Overflow-Use-After-Free.html Added Reference https://developer.arm.com/Arm%20Security%20Center/Mali%20GPU%20Driver%20Vulnerabilities -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
Modified Analysis by [email protected]
Dec. 28, 2023
Action Type Old Value New Value Changed Reference Type http://packetstormsecurity.com/files/176109/Arm-Mali-CSF-Overflow-Use-After-Free.html No Types Assigned http://packetstormsecurity.com/files/176109/Arm-Mali-CSF-Overflow-Use-After-Free.html Third Party Advisory Removed CWE NIST CWE-119 Added CWE NIST CWE-190 Added CWE NIST CWE-416 -
CVE Modified by [email protected]
Dec. 08, 2023
Action Type Old Value New Value Added Reference Arm Limited http://packetstormsecurity.com/files/176109/Arm-Mali-CSF-Overflow-Use-After-Free.html [No types assigned] -
CVE Modified by [email protected]
Nov. 14, 2023
Action Type Old Value New Value Removed CVSS V3.1 Arm Limited AV:L/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H -
Initial Analysis by [email protected]
Nov. 14, 2023
Action Type Old Value New Value Added CVSS V3.1 NIST AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://developer.arm.com/Arm%20Security%20Center/Mali%20GPU%20Driver%20Vulnerabilities No Types Assigned https://developer.arm.com/Arm%20Security%20Center/Mali%20GPU%20Driver%20Vulnerabilities Vendor Advisory Added CWE NIST CWE-119 Added CPE Configuration OR *cpe:2.3:a:arm:mali_gpu_kernel_driver:*:*:*:*:*:*:*:* versions from (including) r41p0 up to (excluding) r43p0 *cpe:2.3:a:arm:valhall_gpu_kernel_driver:*:*:*:*:*:*:*:* versions from (including) r29p0 up to (including) r42p0 -
CVE Received by [email protected]
Nov. 07, 2023
Action Type Old Value New Value Added Description A local non-privileged user can make improper GPU memory processing operations to gain access to already freed memory. Added Reference Arm Limited https://developer.arm.com/Arm%20Security%20Center/Mali%20GPU%20Driver%20Vulnerabilities [No types assigned] Added CWE Arm Limited CWE-416 Added CWE Arm Limited CWE-190 Added CVSS V3.1 Arm Limited AV:L/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H