CVE-2023-47039
Perl: perl for windows binary hijacking vulnerability
Description
A vulnerability was found in Perl. This security issue occurs while Perl for Windows relies on the system path environment variable to find the shell (`cmd.exe`). When running an executable that uses the Windows Perl interpreter, Perl attempts to find and execute `cmd.exe` within the operating system. However, due to path search order issues, Perl initially looks for cmd.exe in the current working directory. This flaw allows an attacker with limited privileges to place`cmd.exe` in locations with weak permissions, such as `C:\ProgramData`. By doing so, arbitrary code can be executed when an administrator attempts to use this executable from these compromised locations.
INFO
Published Date :
Jan. 2, 2024, 6:15 a.m.
Last Modified :
Nov. 21, 2024, 8:29 a.m.
Remotely Exploit :
No
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
Solution
- There is no known solution at this time.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2023-47039.
| URL | Resource |
|---|---|
| https://access.redhat.com/security/cve/CVE-2023-47039 | Third Party Advisory |
| https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1056746 | Mailing List Patch |
| https://bugzilla.redhat.com/show_bug.cgi?id=2249525 | Issue Tracking |
| https://access.redhat.com/security/cve/CVE-2023-47039 | Third Party Advisory |
| https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1056746 | Mailing List Patch |
| https://bugzilla.redhat.com/show_bug.cgi?id=2249525 | Issue Tracking |
| https://perldoc.perl.org/perl5382delta#CVE-2023-47039-Perl-for-Windows-binary-hijacking-vulnerability | |
| https://security.netapp.com/advisory/ntap-20240208-0005/ |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2023-47039 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2023-47039
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2023-47039 vulnerability anywhere in the article.

-
Daily CyberSecurity
CVE-2025-40909: Perl Threads Vulnerability Exposes File Operation Race Condition
A newly disclosed vulnerability in Perl’s threading mechanism, tracked as CVE-2025-40909, exposes systems to race conditions involving the working directory, potentially enabling local attackers to ma ... Read more

-
Daily CyberSecurity
Outlaw Botnet Exploits Weak SSH to Hijack Linux Systems for Crypto Mining
While high-profile ransomware and state-backed APT groups often dominate headlines, it’s crucial not to overlook quieter yet persistent threats. One such threat is Outlaw (also known as “Dota”), a Per ... Read more
-
Daily CyberSecurity
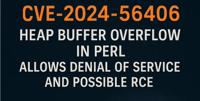
CVE-2024-56406: Heap Overflow Vulnerability in Perl Threatens Denial of Service and Potential Code Execution
Perl, a versatile programming language widely used for various tasks like system administration and web development, has been found to contain a security vulnerability. A recently discovered heap buff ... Read more

-
Cybersecurity News
Critical CVE-2024-45321 Flaw in Popular Perl Module Installer cpanminus, No Patch Available
In a significant security advisory, the Perl community has been alerted to a critical vulnerability, CVE-2024-45321, affecting the widely-used App::cpanminus (cpanm) tool. Rated with a CVSS score of 9 ... Read more
The following table lists the changes that have been made to the
CVE-2023-47039 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://access.redhat.com/security/cve/CVE-2023-47039 Added Reference https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1056746 Added Reference https://bugzilla.redhat.com/show_bug.cgi?id=2249525 Added Reference https://perldoc.perl.org/perl5382delta#CVE-2023-47039-Perl-for-Windows-binary-hijacking-vulnerability Added Reference https://security.netapp.com/advisory/ntap-20240208-0005/ -
CVE Modified by [email protected]
Nov. 06, 2024
Action Type Old Value New Value Removed Reference Red Hat, Inc. https://security.netapp.com/advisory/ntap-20240208-0005/ Removed Reference Red Hat, Inc. https://perldoc.perl.org/perl5382delta#CVE-2023-47039-Perl-for-Windows-binary-hijacking-vulnerability -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CVE Modified by [email protected]
Mar. 28, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://perldoc.perl.org/perl5382delta#CVE-2023-47039-Perl-for-Windows-binary-hijacking-vulnerability [No types assigned] -
CVE Modified by [email protected]
Feb. 08, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://security.netapp.com/advisory/ntap-20240208-0005/ [No types assigned] -
Initial Analysis by [email protected]
Jan. 08, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://access.redhat.com/security/cve/CVE-2023-47039 No Types Assigned https://access.redhat.com/security/cve/CVE-2023-47039 Third Party Advisory Changed Reference Type https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1056746 No Types Assigned https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1056746 Mailing List, Patch Changed Reference Type https://bugzilla.redhat.com/show_bug.cgi?id=2249525 No Types Assigned https://bugzilla.redhat.com/show_bug.cgi?id=2249525 Issue Tracking Added CWE NIST CWE-787 Added CPE Configuration AND OR *cpe:2.3:a:perl:perl:*:*:*:*:*:*:*:* versions up to (excluding) 5.32.1 OR cpe:2.3:o:microsoft:windows:-:*:*:*:*:*:*:* -
CVE Received by [email protected]
Jan. 02, 2024
Action Type Old Value New Value Added Description A vulnerability was found in Perl. This security issue occurs while Perl for Windows relies on the system path environment variable to find the shell (`cmd.exe`). When running an executable that uses the Windows Perl interpreter, Perl attempts to find and execute `cmd.exe` within the operating system. However, due to path search order issues, Perl initially looks for cmd.exe in the current working directory. This flaw allows an attacker with limited privileges to place`cmd.exe` in locations with weak permissions, such as `C:\ProgramData`. By doing so, arbitrary code can be executed when an administrator attempts to use this executable from these compromised locations. Added Reference Red Hat, Inc. https://access.redhat.com/security/cve/CVE-2023-47039 [No types assigned] Added Reference Red Hat, Inc. https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1056746 [No types assigned] Added Reference Red Hat, Inc. https://bugzilla.redhat.com/show_bug.cgi?id=2249525 [No types assigned] Added CWE Red Hat, Inc. CWE-122 Added CVSS V3.1 Red Hat, Inc. AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H