CVE-2023-47246
SysAid Server Path Traversal Vulnerability - [Actively Exploited]
Description
In SysAid On-Premise before 23.3.36, a path traversal vulnerability leads to code execution after an attacker writes a file to the Tomcat webroot, as exploited in the wild in November 2023.
INFO
Published Date :
Nov. 10, 2023, 6:15 a.m.
Last Modified :
Oct. 31, 2025, 2:38 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
SysAid Server (on-premises version) contains a path traversal vulnerability that leads to code execution.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Known Detected Nov 13, 2023
https://www.sysaid.com/blog/service-desk/on-premise-software-security-vulnerability-notification; https://nvd.nist.gov/vuln/detail/CVE-2023-47246
Affected Products
The following products are affected by CVE-2023-47246
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Upgrade to SysAid Server 23.3.36 or later.
Public PoC/Exploit Available at Github
CVE-2023-47246 has a 33 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2023-47246.
| URL | Resource |
|---|---|
| https://documentation.sysaid.com/docs/latest-version-installation-files | Product |
| https://documentation.sysaid.com/docs/on-premise-security-enhancements-2023 | Release Notes Vendor Advisory |
| https://www.sysaid.com/blog/service-desk/on-premise-software-security-vulnerability-notification | Exploit Vendor Advisory |
| https://documentation.sysaid.com/docs/latest-version-installation-files | Product |
| https://documentation.sysaid.com/docs/on-premise-security-enhancements-2023 | Release Notes Vendor Advisory |
| https://www.sysaid.com/blog/service-desk/on-premise-software-security-vulnerability-notification | Exploit Vendor Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2023-47246 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2023-47246 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2023-47246
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
护网2024-POC收录备份
备份的漏洞库,3月开始我们来维护
None
None
None
HTML
wy876
Python
A exploitation tool (webshell)
Shell
wy876 POC | wy876的poc仓库已删库,该项目为其仓库镜像
收集整理漏洞EXP/POC,大部分漏洞来源网络,目前收集整理了1100多个poc/exp,长期更新。
备份的漏洞库,3月开始我们来维护
2023HW漏洞整理,收集整理漏洞EXp/POC,大部分漏洞来源网络,目前收集整理了300多个poc/exp,长期更新。
漏洞文库 wiki.wy876.cn
HTML
None
CVE-2023-47246 是 SysAid On-Premise 软件(版本 23.3.36 之前)中的一个路径遍历漏洞。攻击者可以利用该漏洞将文件写入 Tomcat 的 webroot 目录,从而在服务器上执行任意代码。
exp poc rce
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2023-47246 vulnerability anywhere in the article.

-
BleepingComputer
CISA warns of hackers exploiting SysAid vulnerabilities in attacks
CISA has warned that attackers are actively exploiting two security vulnerabilities in the SysAid IT service management (ITSM) software to hijack administrator accounts. The two unauthenticated XML Ex ... Read more

-
Daily CyberSecurity
CISA Alert: Actively Exploited Zero-Days in CrushFTP, Chrome, and SysAid Added to KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has updated its Known Exploited Vulnerabilities (KEV) Catalog with four new entries that are currently under active exploitation. These ... Read more

-
Cyber Security News
SysAid ITSM Platform Vulnerabilities Allows Pre-authenticated Remote Command Execution
A critical vulnerability chain in SysAid’s On-Premise IT Service Management (ITSM) platform that allows attackers to achieve pre-authenticated Remote Command Execution (RCE). The findings detail how m ... Read more

-
Help Net Security
RCE flaw in MSP-friendly file sharing platform exploited by attackers (CVE-2025-30406)
A critical RCE vulnerability (CVE-2025-30406) affecting the Gladinet CentreStack file-sharing/remote access platform has been added to CISA’s Known Exploited Vulnerabilities catalog on Tuesday. Accord ... Read more

-
Cybersecurity News
CVE-2024-50623: Critical Vulnerability in Cleo Software Actively Exploited in the Wild
Huntress Labs has raised the alarm over the active exploitation of a critical vulnerability (CVE-2024-50623) in Cleo’s Harmony, VLTrader, and LexiCom software, commonly used for managing file transfer ... Read more

-
Cybersecurity News
SafePay Ransomware: A New Threat with Sophisticated Techniques
The SafePay ransomware leak site | Image: HuntressIn October 2024, Huntress analysts uncovered a previously unreported ransomware strain, dubbed SafePay, deployed across two distinct incidents. This r ... Read more

-
TheCyberThrone
CISA adds Palo Alto flaws to KEV Catalog
The US CISA has issued an urgent alert and added two new vulnerabilities related to Palo Alto Networks to its Known Exploited Vulnerabilities CatalogThe first vulnerability, CVE-2024-9463 with a CVSS ... Read more

-
huntress.com
Turning TTPs into CTF Challenges: Huntress CTF 2024 Retro | Huntress
On October 1, 2024, over six thousand people opened the Calculator application on their computer—all at the same time. But they weren’t solving any equations or doing any sort of calculations… in fact ... Read more
-
Cybersecurity News
Hackers Exploit Foundation Software, Exposing Sensitive Contractor Data
Attacker commands enumerating machine details | Image: HuntressRecently, the cybersecurity company Huntress reported a new wave of cyberattacks targeting the widely-used Foundation Accounting Software ... Read more

-
Cybersecurity News
PoC Exploit Releases for Cisco SSM On-Prem Account Takeover (CVE-2024-20419) Flaw
Image Credit: Mohammed AdelA critical vulnerability, identified as CVE-2024-20419, has been publicly disclosed by security researcher Mohammed Adel, who published a detailed writeup along with proof-o ... Read more

-
Cybersecurity News
Cisco Warns of Public PoC Exploit Code of Critical CVE-2024-20419 (CVSS 10) Flaw
Cisco has recently updated its security advisory, alerting users to a critical vulnerability identified as CVE-2024-20419. This flaw affects the Cisco Smart Software Manager On-Prem (Cisco SSM On-Prem ... Read more

-
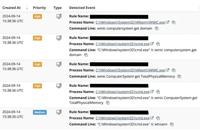
huntress.com
Critical Vulnerability: SysAid CVE-2023-47246 | Huntress
On November 8, 2023, SysAid published an advisory expressing that their on-premise server software had a previously undisclosed vulnerability and is aware of public in-the-wild exploitation. Days prio ... Read more
The following table lists the changes that have been made to the
CVE-2023-47246 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 31, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2023-47246 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2023-47246 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2023-47246 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2023-47246 -
Modified Analysis by [email protected]
Dec. 20, 2024
Action Type Old Value New Value -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://documentation.sysaid.com/docs/latest-version-installation-files Added Reference https://documentation.sysaid.com/docs/on-premise-security-enhancements-2023 Added Reference https://www.sysaid.com/blog/service-desk/on-premise-software-security-vulnerability-notification -
Modified Analysis by [email protected]
Aug. 14, 2024
Action Type Old Value New Value Changed Reference Type https://documentation.sysaid.com/docs/on-premise-security-enhancements-2023 Release Notes https://documentation.sysaid.com/docs/on-premise-security-enhancements-2023 Release Notes, Vendor Advisory Changed CPE Configuration OR *cpe:2.3:a:sysaid:sysaid_on-premises:*:*:*:*:*:*:*:* versions up to (excluding) 23.3.36 OR *cpe:2.3:a:sysaid:sysaid:*:*:*:*:on-premises:*:*:* versions up to (excluding) 23.3.36 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Jul. 08, 2024
Action Type Old Value New Value Added CWE CISA-ADP CWE-22 Added CVSS V3.1 CISA-ADP AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
Initial Analysis by [email protected]
Nov. 13, 2023
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://documentation.sysaid.com/docs/latest-version-installation-files No Types Assigned https://documentation.sysaid.com/docs/latest-version-installation-files Product Changed Reference Type https://documentation.sysaid.com/docs/on-premise-security-enhancements-2023 No Types Assigned https://documentation.sysaid.com/docs/on-premise-security-enhancements-2023 Release Notes Changed Reference Type https://www.sysaid.com/blog/service-desk/on-premise-software-security-vulnerability-notification No Types Assigned https://www.sysaid.com/blog/service-desk/on-premise-software-security-vulnerability-notification Exploit, Vendor Advisory Added CWE NIST CWE-22 Added CPE Configuration OR *cpe:2.3:a:sysaid:sysaid_on-premises:*:*:*:*:*:*:*:* versions up to (excluding) 23.3.36 -
CVE Received by [email protected]
Nov. 10, 2023
Action Type Old Value New Value Added Description In SysAid On-Premise before 23.3.36, a path traversal vulnerability leads to code execution after an attacker writes a file to the Tomcat webroot, as exploited in the wild in November 2023. Added Reference MITRE https://documentation.sysaid.com/docs/on-premise-security-enhancements-2023 [No types assigned] Added Reference MITRE https://www.sysaid.com/blog/service-desk/on-premise-software-security-vulnerability-notification [No types assigned] Added Reference MITRE https://documentation.sysaid.com/docs/latest-version-installation-files [No types assigned]