CVE-2023-48788
Fortinet FortiClient EMS SQL Injection Vulnerability - [Actively Exploited]
Description
A improper neutralization of special elements used in an sql command ('sql injection') in Fortinet FortiClientEMS version 7.2.0 through 7.2.2, FortiClientEMS 7.0.1 through 7.0.10 allows attacker to execute unauthorized code or commands via specially crafted packets.
INFO
Published Date :
March 12, 2024, 3:15 p.m.
Last Modified :
Oct. 24, 2025, 12:54 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Fortinet FortiClient EMS contains a SQL injection vulnerability that allows an unauthenticated attacker to execute commands as SYSTEM via specifically crafted requests.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Known Detected Mar 25, 2024
https://www.fortiguard.com/psirt/FG-IR-24-007; https://nvd.nist.gov/vuln/detail/CVE-2023-48788
Affected Products
The following products are affected by CVE-2023-48788
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Upgrade to Fortinet FortiClient EMS version 7.0.11 / 7.2.3 or later.
Public PoC/Exploit Available at Github
CVE-2023-48788 has a 20 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2023-48788.
| URL | Resource |
|---|---|
| https://fortiguard.com/psirt/FG-IR-24-007 | Vendor Advisory |
| https://fortiguard.com/psirt/FG-IR-24-007 | Vendor Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2023-48788 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2023-48788 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2023-48788
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
Salt Typhoon, APT41
Python
Search exploits, vulnerabilities, and threat intelligence from the Exploit Intelligence Platform.
cve database exploit vulnerabiity
Makefile Python Dockerfile Shell
Exploit Intel MCP Server
Python Makefile
Exploit Intel CLI Search Tool
Python Makefile
An AI-automated tool designed to help Threat Intelligence (CTI) Analysts process the overwhelming volume of daily cybersecurity news and vendor reports.
ai ai-agents cti cyber-reports intelligence-analysis intelligence-automation osint python threat-intelligence
Python
Target Acquired. The Ultimate Web Scanner & Auto-Exploitation Tool. From Recon to RCE in a single strike.
Python
None
Python Dockerfile
A super simple Cisa KEV lookup CLI tool leveraging DuckDB
Python
CLI utility to query Shodan's CVE DB
cve-search shodan shodan-client
Go
None
None
Ini adalah repository kumpulan CVE v.5
allcve cve cvelist newcve
A improper neutralization of special elements used in an sql command ('sql injection') in Fortinet FortiClientEMS version 7.2.0 through 7.2.2, FortiClientEMS 7.0.1 through 7.0.10 allows attacker to execute unauthorized code or commands via specially crafted packets.
CVE-2023-48788 PoC SQLi----> RCE
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2023-48788 vulnerability anywhere in the article.

-
security.nl
'Kritiek SQL Injection-lek in Fortinet FortiClientEMS actief misbruikt bij aanvallen'
Een kritiek SQL Injection-beveiligingslek in Fortinet FortiClientEMS wordt al sinds een aantal dagen actief misbruikt bij aanvallen, zo waarschuwt securitybedrijf Defused. Fortinet kwam op 6 februari ... Read more

-
The Cyber Express
INC Ransom’s Franchise Model Is Putting Critical Infrastructure on the Chopping Block
When Australia’s cyber watchdog issued a fresh advisory on INC Ransom, security teams worldwide are bound to take note — not because INC is new, but because the group’s business model has quietly made ... Read more

-
Daily CyberSecurity
Endpoint Exposed: Critical FortiClient EMS Flaw (CVSS 9.1) Allows Unauthenticated RCE
Fortinet has issued a high-priority security advisory for its FortiClient Enterprise Management Server (EMS), warning of a critical SQL injection vulnerability that could allow attackers to execute ar ... Read more

-
security.nl
Fortinet waarschuwt voor SQL Injection beveiligingslek in FortiClientEMS
Fortinet waarschuwt klanten voor een kritiek beveiligingslek in FortiClientEMS waardoor SQL Injection mogelijk is. Twee jaar geleden werd een andere SQL Injection kwetsbaarheid actief misbruikt bij aa ... Read more

-
Daily CyberSecurity
“Osiris” Rises: New Ransomware Targets Southeast Asian Food Giant with Advanced Tactics
A new ransomware family, borrowing the name of the ancient Egyptian god of the dead, has emerged in a high-profile attack against a major food service franchisee in Southeast Asia. Dubbed Osiris, this ... Read more

-
Daily CyberSecurity
MSP Nightmare: Medusa & DragonForce Exploit SimpleHelp RMM Flaws for SYSTEM Access
Image: Zensec A new report from Zensec has exposed a critical vulnerability in the IT supply chain, detailing how two major Ransomware-as-a-Service (RaaS) groups, Medusa and DragonForce, are actively ... Read more

-
Daily CyberSecurity
Critical RCE (CVE-2025-10035) in GoAnywhere MFT Used by Medusa Ransomware Group
Microsoft Threat Intelligence has issued a warning following the discovery of active exploitation of a newly disclosed critical vulnerability in GoAnywhere Managed File Transfer (MFT) software by the ... Read more

-
CybersecurityNews
Qilin Ransomware Leads The Attack Landscape With 70+ Claimed Victims in July
The ransomware threat landscape witnessed a concerning surge in July 2025, with the Qilin ransomware group maintaining its dominant position for the third time in four months. The group successfully c ... Read more

-
Red Canary
Our favorite talks from fwd:cloudsec 2025
In June 2025, the cloud security community converged on Denver, Colorado, for fwd:cloudsec North America 2025, and Red Canary was thrilled to be a sponsor! Hundreds of passionate cloud security practi ... Read more

-
Daily CyberSecurity
Kaspersky Report Reveals Growing Threat from Old Exploits and OS Vulnerabilities in Q1 2025
Kaspersky’s latest “Exploits and vulnerabilities in Q1 2025” shows that attackers are doubling down on aging exploits, platform-specific weaknesses, and mismanaged updates. With over 9,700 vulnerabili ... Read more
-
Daily CyberSecurity
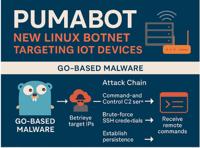
PumaBot: New Stealthy Linux Botnet Evades Detection, Targets IoT Devices
Cybersecurity researchers at Darktrace have exposed a stealthy and persistent Linux-based botnet dubbed PumaBot, which leverages Go binaries, SSH brute-force attacks, and custom backdoors to target In ... Read more

-
Daily CyberSecurity
SocGholish Reloaded: Darktrace Uncovers Ransomware-Primed Loader Campaign
In a recent report, Darktrace’s Threat Research team has detailed a sophisticated malware campaign involving the SocGholish loader—a JavaScript-based first-stage malware now weaponized by ransomware a ... Read more

-
security.nl
Mandiant: kwetsbaarheden in vpn-software vaakst aangevallen vorig jaar
Kwetsbaarheden in vpn-software blijven een zeer populair doelwit van aanvallers, zo stelt Mandiant. De helft van alle cyberincidenten die het securitybedrijf vorig jaar onderzocht begonnen via kwetsba ... Read more

-
Help Net Security
Understanding 2024 cyber attack trends
Mandiant has released the M-Trends 2025 report, which outlines global cyber attack trends based on their own incident response engagements from 2024. Key trends and insights In 2024, Mandiant handled ... Read more

-
Cybersecurity News
Google Streamlines “Results About You” Removal Process
Since 2021, Google has gradually introduced tools that allow users to exert greater control over the presence of their personal information in search results. More recently, the company has made it ev ... Read more

-
The Hacker News
Microsoft Uncovers Sandworm Subgroup's Global Cyber Attacks Spanning 15+ Countries
A subgroup within the infamous Russian state-sponsored hacking group known as Sandworm has been attributed to a multi-year initial access operation dubbed BadPilot that stretched across the globe. "Th ... Read more

-
The Register
Russia's Sandworm caught snarfing credentials, data from American and Brit orgs
An initial-access subgroup of Russia's Sandworm last year wriggled its way into networks within the US, UK, Canada and Australia, stealing credentials and data from "a limited number of organizations, ... Read more

-
Dark Reading
Microsoft: Russia's Sandworm APT Exploits Edge Bugs Globally
Source: Kenishirotie via Alamy Stock PhotoArguably, no advanced persistent threat (APT) enjoys as much notoriety as Sandworm, otherwise known as Military Unit 74455 within Russia's military intelligen ... Read more

-
BleepingComputer
BadPilot network hacking campaign fuels Russian SandWorm attacks
A subgroup of the Russian state-sponsored hacking group APT44, also known as 'Seashell Blizzard' and 'Sandworm', has been targeting critical organizations and governments in a multi-year campaign dubb ... Read more

-
Cybersecurity News
IBM’s HashiCorp Acquisition Under Scrutiny: CMA Investigates Competition Concerns
The United Kingdom’s Competition and Markets Authority (CMA) recently announced that it would launch an investigation into IBM’s $6.4 billion acquisition of HashiCorp, a software company specializing ... Read more
The following table lists the changes that have been made to the
CVE-2023-48788 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 24, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2023-48788 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2023-48788 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2023-48788 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2023-48788 -
Modified Analysis by [email protected]
Jan. 27, 2025
Action Type Old Value New Value Changed CPE Configuration OR *cpe:2.3:a:fortinet:forticlient_enterprise_management_server:*:*:*:*:*:*:*:* versions from (including) 7.0.1 up to (including) 7.0.10 *cpe:2.3:a:fortinet:forticlient_enterprise_management_server:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.2 OR *cpe:2.3:a:fortinet:forticlient_enterprise_management_server:*:*:*:*:*:*:*:* versions from (including) 7.0.1 up to (excluding) 7.0.11 *cpe:2.3:a:fortinet:forticlient_enterprise_management_server:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (excluding) 7.2.3 -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://fortiguard.com/psirt/FG-IR-24-007 -
CVE Modified by [email protected]
Jun. 04, 2024
Action Type Old Value New Value -
Modified Analysis by [email protected]
May. 23, 2024
Action Type Old Value New Value Changed Reference Type https://fortiguard.com/psirt/FG-IR-24-007 No Types Assigned https://fortiguard.com/psirt/FG-IR-24-007 Vendor Advisory -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Mar. 26, 2024
Action Type Old Value New Value Added Due Date 2024-04-15 Added Required Action Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. Added Vulnerability Name Fortinet FortiClient EMS SQL Injection Vulnerability Added Date Added 2024-03-25 -
CVE Modified by [email protected]
Mar. 19, 2024
Action Type Old Value New Value Added Reference Fortinet, Inc. https://fortiguard.com/psirt/FG-IR-24-007 [No types assigned] Removed Reference Fortinet, Inc. https://fortiguard.com/psirt/FG-IR-23-430 -
Initial Analysis by [email protected]
Mar. 15, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://fortiguard.com/psirt/FG-IR-23-430 No Types Assigned https://fortiguard.com/psirt/FG-IR-23-430 Vendor Advisory Added CPE Configuration OR *cpe:2.3:a:fortinet:forticlient_enterprise_management_server:*:*:*:*:*:*:*:* versions from (including) 7.0.1 up to (including) 7.0.10 *cpe:2.3:a:fortinet:forticlient_enterprise_management_server:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (including) 7.2.2 -
CVE Received by [email protected]
Mar. 12, 2024
Action Type Old Value New Value Added Description A improper neutralization of special elements used in an sql command ('sql injection') in Fortinet FortiClientEMS version 7.2.0 through 7.2.2, FortiClientEMS 7.0.1 through 7.0.10 allows attacker to execute unauthorized code or commands via specially crafted packets. Added Reference Fortinet, Inc. https://fortiguard.com/psirt/FG-IR-23-430 [No types assigned] Added CWE Fortinet, Inc. CWE-89 Added CVSS V3.1 Fortinet, Inc. AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H