CVE-2024-0087
CVE
Description
NVIDIA Triton Inference Server for Linux contains a vulnerability where a user can set the logging location to an arbitrary file. If this file exists, logs are appended to the file. A successful exploit of this vulnerability might lead to code execution, denial of service, escalation of privileges, information disclosure, and data tampering.
INFO
Published Date :
May 14, 2024, 2:39 p.m.
Last Modified :
Sept. 19, 2025, 1:17 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-0087
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-0087.
| URL | Resource |
|---|---|
| https://nvidia.custhelp.com/app/answers/detail/a_id/5535 | Vendor Advisory |
| https://nvidia.custhelp.com/app/answers/detail/a_id/5535 | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-0087 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-0087
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-0087 vulnerability anywhere in the article.

-
Daily CyberSecurity
OpenAI Releases GPT-OSS-SafeGuard Models for Customizable AI Safety
Earlier in 2025, OpenAI released its own open-source artificial intelligence models, namely GPT-OSS-20B and GPT-OSS-120B, both of which demonstrated superior reasoning performance compared to many exi ... Read more

-
Daily CyberSecurity
AI’s New Attack Vector: How Real-Time Bots Are Straining Websites
The prominent U.S. CDN provider Fastly has released its Q2 2025 Threat Defense Report, revealing that AI-driven bots are reshaping web traffic patterns, with the most significant risks stemming not fr ... Read more

-
Daily CyberSecurity
Critical Triton Flaws (CVSS 9.8) Expose AI Servers to Remote Takeover – Patch Now!
NVIDIA has released urgent software updates to address a set of critical vulnerabilities discovered in its popular Triton Inference Server, a widely used open-source AI serving platform. The flaws, re ... Read more

-
Daily CyberSecurity
NVIDIA Ends Feature Support for GTX 7XX, 9XX, 10XX GPUs, Capping Driver Updates in October
NVIDIA recently announced that its legacy graphics cards based on the Maxwell and Pascal architectures will receive their final feature updates in October 2025. After that point, these GPUs will conti ... Read more
-
Daily CyberSecurity
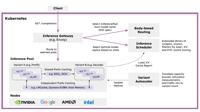
Red Hat Unveils llm-d: Scaling Generative AI for the Enterprise
Red Hat has recently unveiled an open-source initiative named llm-d, designed to address the most critical demand of the generative AI era: large-scale inference. The llm-d project is a collaborative ... Read more

-
Daily CyberSecurity
Python-Powered Triton RAT Exfiltrates Data via Telegram and Evades Analysis
Cado Security Labs has identified a Python-based Remote Access Tool (RAT) named Triton RAT. This open-source RAT is available on GitHub and enables users to remotely access and control a system using ... Read more
The following table lists the changes that have been made to the
CVE-2024-0087 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Sep. 19, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Added CPE Configuration AND OR *cpe:2.3:a:nvidia:triton_inference_server:*:*:*:*:*:*:*:* versions from (including) 20.10 up to (excluding) 24.04 OR cpe:2.3:o:linux:linux_kernel:-:*:*:*:*:*:*:* Added Reference Type CVE: https://nvidia.custhelp.com/app/answers/detail/a_id/5535 Types: Vendor Advisory Added Reference Type NVIDIA Corporation: https://nvidia.custhelp.com/app/answers/detail/a_id/5535 Types: Vendor Advisory -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://nvidia.custhelp.com/app/answers/detail/a_id/5535 -
CVE Received by [email protected]
May. 14, 2024
Action Type Old Value New Value Added Description NVIDIA Triton Inference Server for Linux contains a vulnerability where a user can set the logging location to an arbitrary file. If this file exists, logs are appended to the file. A successful exploit of this vulnerability might lead to code execution, denial of service, escalation of privileges, information disclosure, and data tampering. Added Reference NVIDIA Corporation https://nvidia.custhelp.com/app/answers/detail/a_id/5535 [No types assigned] Added CWE NVIDIA Corporation CWE-73 Added CVSS V3.1 NVIDIA Corporation AV:N/AC:L/PR:H/UI:N/S:C/C:H/I:L/A:H