CVE-2024-10205
Authorization bypass vulnerability in Hitachi Infrastructure Analytics Advisor and Hitachi Ops Center Analyzer
Description
Authentication Bypass vulnerability in Hitachi Ops Center Analyzer on Linux, 64 bit (Hitachi Ops Center Analyzer detail view component), Hitachi Infrastructure Analytics Advisor on Linux, 64 bit (Hitachi Data Center Analytics component ).This issue affects Hitachi Ops Center Analyzer: from 10.0.0-00 before 11.0.3-00; Hitachi Infrastructure Analytics Advisor: from 2.1.0-00 through 4.4.0-00.
INFO
Published Date :
Dec. 17, 2024, 2:15 a.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-10205
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] |
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-10205.
| URL | Resource |
|---|---|
| https://www.hitachi.com/products/it/software/security/info/vuls/hitachi-sec-2024-151/index.html |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-10205 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-10205
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-10205 vulnerability anywhere in the article.
-
Daily CyberSecurity
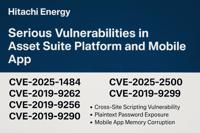
Hitachi Energy’s Asset Suite Hit by Multiple Critical Vulnerabilities
Hitachi Energy has issued a cybersecurity advisory warning of multiple vulnerabilities impacting its Asset Suite product—a widely used Enterprise Asset Management (EAM) solution in the power generatio ... Read more

-
Daily CyberSecurity
Hitachi Vantara Patches Critical Resource Injection Flaw in Pentaho
Hitachi Vantara has issued a critical security advisory addressing a serious vulnerability in its widely used Pentaho Data Integration & Analytics platform. Tracked as CVE-2025-0756 with a CVSS score ... Read more

-
Cybersecurity News
Critical Flaws Exploited: Cisco, Windows, Hitachi, WhatsUp Gold at Risk
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning for federal agencies to mitigate security vulnerabilities being actively exploited in Cisco routers, Windows syste ... Read more

-
Cybersecurity News
CVE-2024-37361 (CVSS 9.9): Critical Vulnerability in Pentaho Business Analytics Server
Hitachi Vantara has issued a security advisory addressing a vulnerability, designated as CVE-2024-37361, in its Pentaho Business Analytics Server. This vulnerability carries a CVSS score of 9.9, indic ... Read more

-
Cybersecurity News
CVE-2024-45387 (CVSS 9.9): Critical SQL Injection Vulnerability Found in Apache Traffic Control
A critical-severity security flaw has been uncovered in Apache Traffic Control, a popular open-source platform used to build large-scale content delivery networks (CDNs). This vulnerability, identifie ... Read more
The following table lists the changes that have been made to the
CVE-2024-10205 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
New CVE Received by [email protected]
Dec. 17, 2024
Action Type Old Value New Value Added Description Authentication Bypass vulnerability in Hitachi Ops Center Analyzer on Linux, 64 bit (Hitachi Ops Center Analyzer detail view component), Hitachi Infrastructure Analytics Advisor on Linux, 64 bit (Hitachi Data Center Analytics component ).This issue affects Hitachi Ops Center Analyzer: from 10.0.0-00 before 11.0.3-00; Hitachi Infrastructure Analytics Advisor: from 2.1.0-00 through 4.4.0-00. Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:H/A:H Added CWE CWE-306 Added Reference https://www.hitachi.com/products/it/software/security/info/vuls/hitachi-sec-2024-151/index.html