CVE-2024-20381
Cisco Network Services Orchestrator Configuration Update Authorization Bypass Vulnerability
Description
A vulnerability in the JSON-RPC API feature in Cisco Crosswork Network Services Orchestrator (NSO) and ConfD that is used by the web-based management interfaces of Cisco Optical Site Manager and Cisco RV340 Dual WAN Gigabit VPN Routers could allow an authenticated, remote attacker to modify the configuration of an affected application or device. This vulnerability is due to improper authorization checks on the API. An attacker with privileges sufficient to access the affected application or device could exploit this vulnerability by sending malicious requests to the JSON-RPC API. A successful exploit could allow the attacker to make unauthorized modifications to the configuration of the affected application or device, including creating new user accounts or elevating their own privileges on an affected system.
INFO
Published Date :
Sept. 11, 2024, 5:15 p.m.
Last Modified :
Oct. 8, 2024, 9:43 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-20381
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-20381.
| URL | Resource |
|---|---|
| https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-nso-auth-bypass-QnTEesp | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-20381 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-20381
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-20381 vulnerability anywhere in the article.

-
Daily CyberSecurity
Cisco Patches High-Severity CVE-2025-20350 DoS Flaw in Desk and IP Phones
Cisco has released security updates to patch two vulnerabilities (CVE-2025-20350 and CVE-2025-20351) affecting multiple Cisco Desk Phone and IP Phone models, including the 9800, 7800, 8800, and 8875 s ... Read more

-
Daily CyberSecurity
Cisco SNMP Flaw (CVE-2025-20352) Actively Exploited: Patch Now to Stop Root Access!
Cisco has issued a security advisory warning of a critical flaw in its IOS and IOS XE Software, tracked as CVE-2025-20352 with a CVSS score of 7.7, which affects the SNMP subsystem and has already bee ... Read more

-
Cybersecurity News
SAP Patches Critical BusinessObjects Vulnerability with October Security Updates
SAP has released its monthly security patch updates, addressing several vulnerabilities across its product portfolio. The October Security Patch Day includes six new security notes and six updates to ... Read more

-
Cybersecurity News
Authd Vulnerability (CVE-2024-9313) Allows User Impersonation on Ubuntu Systems
A high-severity vulnerability, CVE-2024-9313 ((CVSS 8.8)), has been discovered in Authd, an authentication daemon used for secure identity and access management in Ubuntu machines. This flaw could all ... Read more

-
Cybersecurity News
Cybercriminals Exploit CosmicSting Vulnerability, Hacking Thousands of Adobe Commerce and Magento Stores
Malware in the National Geographic store | Image: SansecIn a significant cybersecurity breach this summer, cybercriminals compromised approximately 5% of all Adobe Commerce and Magento stores, affecti ... Read more
-
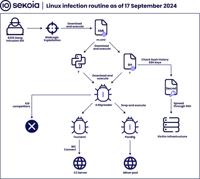
Cybersecurity News
Hadooken & K4Spreader Malware: 8220 Gang’s Latest Cloud Hijacking Tools
Linux infection routine | Image: Sekoia’s Threat Detection & Research (TDR) teamThe notorious 8220 Gang, a China-based intrusion set first identified in 2018, continues to expand its arsenal with two ... Read more

-
Cybersecurity News
Sophisticated Cyber Espionage: Earth Baxia Uses CVE-2024-36401 and Cobalt Strike to Infiltrate APAC
Overview of the attack chain | Image: Trend MicroIn a recent report from Trend Micro, the cyber espionage group Earth Baxia has been identified targeting government organizations in Taiwan and potenti ... Read more

-
Cybersecurity News
Cisco Issues Security Advisories: Critical Vulnerabilities Impact Multiple Products
Cisco Systems has released a series of urgent security advisories, revealing a total of nine vulnerabilities affecting various products, including Cisco IOS XR Software, Crosswork Network Services Orc ... Read more
The following table lists the changes that have been made to the
CVE-2024-20381 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Oct. 08, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-nso-auth-bypass-QnTEesp No Types Assigned https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-nso-auth-bypass-QnTEesp Vendor Advisory Added CWE NIST NVD-CWE-noinfo Added CPE Configuration OR *cpe:2.3:o:cisco:ios_xr:6.5.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.3:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.15:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.25:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.26:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.28:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.29:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.31:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.32:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.33:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.90:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.92:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.5.93:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.6.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.6.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.6.3:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.6.4:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.6.11:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.6.12:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.6.25:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.7.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.7.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.7.3:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.7.4:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.7.35:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.8.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.8.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.9.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:6.9.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.0.0:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.0.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.0.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.0.11:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.0.12:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.0.14:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.0.90:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.1.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.1.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.1.3:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.1.15:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.1.25:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.2.0:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.2.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.2.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.2.12:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.3.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.3.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.3.3:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.3.4:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.3.5:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.3.6:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.3.15:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.3.16:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.3.27:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.4.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.4.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.4.15:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.4.16:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.5.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.5.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.5.3:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.5.4:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.5.5:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.5.12:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.5.52:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.6.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.6.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.6.3:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.6.15:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.7.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.7.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.7.21:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.8.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.8.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.8.12:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.8.22:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.9.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.9.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.9.21:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.10.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.10.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.11.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:7.11.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:24.1.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:24.1.2:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:24.2.1:*:*:*:*:*:*:* *cpe:2.3:o:cisco:ios_xr:24.2.11:*:*:*:*:*:*:* Added CPE Configuration OR *cpe:2.3:a:cisco:network_services_orchestrator:4.4.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:4.5.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:4.7.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:4.7.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.1.1.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.1.1.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.1.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.1.4.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.2.0.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.2.0.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.2.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.2.1.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.2.3.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.3.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.3.4.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.0.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.0.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.1.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.2.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.2.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.3.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.3.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.3.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.3.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.4.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.4.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.4.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.5:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.5.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.5.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.6:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.7:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.4.7.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.5:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.6:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.7:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.8:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.9:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.10:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.11:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.2.12:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.3.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.4.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.5:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.6:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.6.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.7:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.8:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.9:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.5.10:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.3.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.5:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.6:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.6.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.7:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.7.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.7.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.8:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.8.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.9:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.10:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.11:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.12:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.13:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.14:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.6.14.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.1.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.2.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.5:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.5.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.6:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.6.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.6.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.6.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.7:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.8:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.8.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.9:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.9.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.10:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.10.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.10.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.11:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.12:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.13:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.14:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.15:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.15.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.7.17:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.2.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.5:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.6:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.7:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.8:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.9:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.10:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.11:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.12:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:5.8.13:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.1.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.5:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.6:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.7:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.8:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.9:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.10:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.11:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.0.12:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.2.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.3:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.3.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.3.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.4:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.5:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.6:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.6.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.7:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.7.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.8:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.10:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.11:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.11.1:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.11.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.1.12:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.2:*:*:*:*:*:*:* *cpe:2.3:a:cisco:network_services_orchestrator:6.2.2:*:*:*:*:*:*:* Added CPE Configuration OR *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.00.29:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.00.33:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.01.16:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.01.17:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.01.18:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.01.20:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.02.16:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.15:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.16:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.17:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.18:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.19:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.20:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.21:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.22:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.24:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.26:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.27:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.28:*:*:*:*:*:*:* *cpe:2.3:o:cisco:small_business_rv_series_router_firmware:1.0.03.29:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Sep. 25, 2024
Action Type Old Value New Value Changed Description A vulnerability in the JSON-RPC API feature in ConfD that is used by the web-based management interfaces of Cisco Crosswork Network Services Orchestrator (NSO), Cisco Optical Site Manager, and Cisco RV340 Dual WAN Gigabit VPN Routers could allow an authenticated, remote attacker to modify the configuration of an affected application or device. This vulnerability is due to improper authorization checks on the API. An attacker with privileges sufficient to access the affected application or device could exploit this vulnerability by sending malicious requests to the JSON-RPC API. A successful exploit could allow the attacker to make unauthorized modifications to the configuration of the affected application or device, including creating new user accounts or elevating their own privileges on an affected system. A vulnerability in the JSON-RPC API feature in Cisco Crosswork Network Services Orchestrator (NSO) and ConfD that is used by the web-based management interfaces of Cisco Optical Site Manager and Cisco RV340 Dual WAN Gigabit VPN Routers could allow an authenticated, remote attacker to modify the configuration of an affected application or device. This vulnerability is due to improper authorization checks on the API. An attacker with privileges sufficient to access the affected application or device could exploit this vulnerability by sending malicious requests to the JSON-RPC API. A successful exploit could allow the attacker to make unauthorized modifications to the configuration of the affected application or device, including creating new user accounts or elevating their own privileges on an affected system. -
CVE Received by [email protected]
Sep. 11, 2024
Action Type Old Value New Value Added Description A vulnerability in the JSON-RPC API feature in ConfD that is used by the web-based management interfaces of Cisco Crosswork Network Services Orchestrator (NSO), Cisco Optical Site Manager, and Cisco RV340 Dual WAN Gigabit VPN Routers could allow an authenticated, remote attacker to modify the configuration of an affected application or device. This vulnerability is due to improper authorization checks on the API. An attacker with privileges sufficient to access the affected application or device could exploit this vulnerability by sending malicious requests to the JSON-RPC API. A successful exploit could allow the attacker to make unauthorized modifications to the configuration of the affected application or device, including creating new user accounts or elevating their own privileges on an affected system. Added Reference Cisco Systems, Inc. https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-nso-auth-bypass-QnTEesp [No types assigned] Added CWE Cisco Systems, Inc. CWE-285 Added CVSS V3.1 Cisco Systems, Inc. AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H