CVE-2024-21545
Proxmox Virtual Environment API Arbitary File Read Vulnerability
Description
Proxmox Virtual Environment is an open-source server management platform for enterprise virtualization. Insufficient safeguards against malicious API response values allow authenticated attackers with 'Sys.Audit' or 'VM.Monitor' privileges to download arbitrary host files via the API. When handling the result from a request handler before returning it to the user, the handle_api2_request function will check for the ‘download’ or ‘data’->’download’ objects inside the request handler call response object. If present, handle_api2_request will read a local file defined by this object and return it to the user. Two endpoints were identified which can control the object returned by a request handler sufficiently that the ’download’ object is defined and user controlled. This results in arbitrary file read. The privileges of this file read can result in full compromise of the system by various impacts such as disclosing sensitive files allowing for privileged session forgery.
INFO
Published Date :
Sept. 25, 2024, 1:15 a.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Public PoC/Exploit Available at Github
CVE-2024-21545 has a 2 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-21545.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-21545 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-21545
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Proxmox VE Arbitrary File Read -> Full System Compromise . Not Testeted yet... will test them this week
Python
CVE POC repo 자동 수집기
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-21545 vulnerability anywhere in the article.

-
Cybersecurity News
Critical EoP Flaw in Microsoft’s Remote Registry: Researcher Publishes PoC for CVE-2024-43532
Akamai researcher Stiv Kupchik published the technical details and a proof-of-concept (PoC) exploit code for a critical Elevation of Privilege (EoP) vulnerability, CVE-2024-43532, in Microsoft’s Remot ... Read more
-
Cybersecurity News
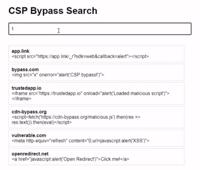
CSP Bypass: A New Open-Source Tool for Ethical Hackers to Overcome Content Security Policies
Renowned security researcher Renniepak, the founder of Hacker Hideout, has launched an open-source tool called CSP Bypass. This tool is designed to assist ethical hackers and security researchers in i ... Read more

-
Cybersecurity News
Proxmox Virtual Environment and Mail Gateway Exposed to Critical API Vulnerability
A critical vulnerability has been identified in Proxmox Virtual Environment (VE) and Proxmox Mail Gateway (PMG) that could allow unauthorized access to sensitive files and potentially lead to a full s ... Read more
The following table lists the changes that have been made to the
CVE-2024-21545 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Sep. 25, 2024
Action Type Old Value New Value Added CWE CISA-ADP CWE-73 -
CVE Received by [email protected]
Sep. 25, 2024
Action Type Old Value New Value Added Description Proxmox Virtual Environment is an open-source server management platform for enterprise virtualization. Insufficient safeguards against malicious API response values allow authenticated attackers with 'Sys.Audit' or 'VM.Monitor' privileges to download arbitrary host files via the API. When handling the result from a request handler before returning it to the user, the handle_api2_request function will check for the ‘download’ or ‘data’->’download’ objects inside the request handler call response object. If present, handle_api2_request will read a local file defined by this object and return it to the user. Two endpoints were identified which can control the object returned by a request handler sufficiently that the ’download’ object is defined and user controlled. This results in arbitrary file read. The privileges of this file read can result in full compromise of the system by various impacts such as disclosing sensitive files allowing for privileged session forgery. Added Reference Snyk https://git.proxmox.com/?p=pve-http-server.git;a=blob;f=src/PVE/APIServer/AnyEvent.pm;h=a8d60c18102d2eea9235720852fb60d90f405d0a;hb=HEAD#l988 [No types assigned] Added Reference Snyk https://forum.proxmox.com/threads/proxmox-virtual-environment-security-advisories.149331/post-705345 [No types assigned] Added CWE Snyk CWE-73 Added CVSS V3.1 Snyk AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:N