CVE-2024-22116
Remote code execution within ping script
Description
An administrator with restricted permissions can exploit the script execution functionality within the Monitoring Hosts section. The lack of default escaping for script parameters enabled this user ability to execute arbitrary code via the Ping script, thereby compromising infrastructure.
INFO
Published Date :
Aug. 12, 2024, 1:38 p.m.
Last Modified :
Nov. 3, 2025, 10:16 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
Solution
- There is no known solution at this time.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-22116.
| URL | Resource |
|---|---|
| https://support.zabbix.com/browse/ZBX-25016 | Vendor Advisory |
| https://lists.debian.org/debian-lts-announce/2024/10/msg00000.html |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-22116 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-22116
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-22116 vulnerability anywhere in the article.

-
Daily CyberSecurity
Zabbix API Vulnerability: High-Severity SQL Injection Threatens Network Monitoring Security
A high-severity security vulnerability has been identified in the Zabbix API, a popular open-source monitoring solution used by enterprises worldwide to track the status of network services, servers, ... Read more

-
Daily CyberSecurity
Multiple Vulnerabilities in Zabbix Open the Door to XSS, DoS, and SQL Injection
Zabbix, a cornerstone in IT infrastructure monitoring fixed five newly disclosed security vulnerabilities ranging from low-severity information leaks to high-impact SQL injection and denial-of-service ... Read more

-
Cybersecurity News
CVE-2024-42327 (CVSS 9.9): Critical SQL Injection Vulnerability Found in Zabbix
Zabbix, a popular open-source IT infrastructure monitoring tool used by organizations worldwide, has been found to contain a critical SQL injection vulnerability (CVE-2024-42327) with a CVSS score of ... Read more

-
Cybersecurity News
Akira Ransomware Exploits SonicWall SSLVPN Flaw (CVE-2024-40766)
SonicWall has issued a warning: the recently patched critical access control vulnerability, tracked as CVE-2024-40766, is now actively exploited in the wild. The flaw, originally thought to impact onl ... Read more

-
europa.eu
Cyber Brief 24-09 - August 2024
Cyber Brief (August 2024)September 4, 2024 - Version: 1.0TLP:CLEARExecutive summaryWe analysed 249 open source reports for this Cyber Brief1.Relating to cyber policy and law enforcement, in Europe, th ... Read more

-
Cybersecurity News
RomCom Group’s Underground Ransomware Exploits Microsoft Zero-Day Flaw
The data leak site for Underground ransomwareFortiGuard Labs found a new ransomware variant, Underground, that has been linked to the Russia-based RomCom group (also known as Storm-0978). This insidio ... Read more

-
Cybersecurity News
Google Patches Actively Exploited Zero-Day in September Android Update
Google’s September 2024 Android security patch addresses 36 vulnerabilities, one of which has already been exploited in active targeted attacks. The zero-day flaw, tracked as CVE-2024-32896 (CVSS scor ... Read more

-
Cyber Security News
Cyber Security News Letter – Data Breaches, Vulnerability, Cyber Attack & Other Stories
The “Weekly Cyber Security News Letter – Data Breaches, Vulnerability, Cyber Attack & More” provides a comprehensive overview of the latest developments in the cybersecurity landscape. Each edition hi ... Read more

-
Cybersecurity News
Unpatched Kubernetes Flaw Leaves Clusters Open to Exploitation: Researcher Unveils Command Injection Vulnerability
Akamai researcher Tomer Peled has uncovered a concerning design flaw within Kubernetes’ git-sync project. This flaw could potentially enable attackers to execute commands or exfiltrate sensitive data, ... Read more

-
Cybersecurity News
Ivanti Issues Critical Fixes for ITSM Vulnerabilities (CVE-2024-7569 and CVE-2024-7570)
Please enable JavaScriptIvanti has released a security advisory addressing two significant vulnerabilities in its Neurons for IT Service Management (ITSM) platform, urging on-premise customers to take ... Read more

-
Cyber Security News
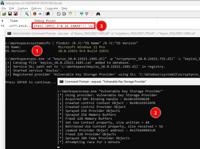
Zabbix Server Vulnerability Lets Attacker Execute Arbitrary Code Via Ping Script
A critical security vulnerability, identified as CVE-2024-22116, has been patched in Zabbix, a popular monitoring solution. The vulnerability allowed an administrator with restricted permissions to ex ... Read more
-
Cybersecurity News
BYOVDLL: New Exploit Bypasses Microsoft’s LSASS Defenses
In July 2022, Microsoft made modifications to its Protected Process Light (PPL) system aimed at mitigating a vulnerability that allowed bypassing the protection of LSASS, a critical process responsibl ... Read more

-
Cybersecurity News
CVE-2024-22116 (CVSS 9.9): Critical RCE Vulnerability Found in Zabbix Monitoring Solution
Zabbix, a widely-adopted open-source solution for enterprise-level IT infrastructure monitoring, has disclosed a critical security vulnerability that could lead to full system compromise. The vulnerab ... Read more
The following table lists the changes that have been made to the
CVE-2024-22116 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 03, 2025
Action Type Old Value New Value Added Reference https://lists.debian.org/debian-lts-announce/2024/10/msg00000.html -
Initial Analysis by [email protected]
Dec. 04, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H Added CWE NIST CWE-94 Added CPE Configuration OR *cpe:2.3:a:zabbix:zabbix:*:*:*:*:*:*:*:* versions from (including) 6.4.9 up to (including) 6.4.15 *cpe:2.3:a:zabbix:zabbix:7.0.0:alpha1:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:alpha2:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:alpha3:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:alpha4:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:alpha5:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:alpha6:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:alpha7:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:alpha8:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:alpha9:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:beta1:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:beta2:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:beta3:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:rc1:*:*:*:*:*:* *cpe:2.3:a:zabbix:zabbix:7.0.0:rc2:*:*:*:*:*:* Changed Reference Type https://support.zabbix.com/browse/ZBX-25016 No Types Assigned https://support.zabbix.com/browse/ZBX-25016 Vendor Advisory -
CVE Received by [email protected]
Aug. 12, 2024
Action Type Old Value New Value Added Description An administrator with restricted permissions can exploit the script execution functionality within the Monitoring Hosts section. The lack of default escaping for script parameters enabled this user ability to execute arbitrary code via the Ping script, thereby compromising infrastructure. Added Reference Zabbix https://support.zabbix.com/browse/ZBX-25016 [No types assigned] Added CWE Zabbix CWE-94 Added CVSS V3.1 Zabbix AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H