CVE-2024-3094
Xz: malicious code in distributed source
Description
Malicious code was discovered in the upstream tarballs of xz, starting with version 5.6.0. Through a series of complex obfuscations, the liblzma build process extracts a prebuilt object file from a disguised test file existing in the source code, which is then used to modify specific functions in the liblzma code. This results in a modified liblzma library that can be used by any software linked against this library, intercepting and modifying the data interaction with this library.
INFO
Published Date :
March 29, 2024, 5:15 p.m.
Last Modified :
Aug. 19, 2025, 1:15 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Consult the vendor advisory for specific guidance.
- Upgrade to the latest patched version, or downgrade to a version prior to 5.6.0.
Public PoC/Exploit Available at Github
CVE-2024-3094 has a 396 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-3094.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-3094 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-3094
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
An autonomous SecOps analyst skill for TRAE, triages alerts, enriches IOCs with live threat intel, looks up CVEs, generates Sigma rules, and makes bounded escalation decisions. One paste → one verdict → one shareable report.
Python
None
Python
None
C# HTML CSS JavaScript
Agentic cybersecurity investigation platform using LangGraph, structured AI reasoning, threat intelligence retrieval, validation-aware workflows, and persistent memory orchestration.
Dockerfile Python Mako
None
A security monitoring using Wazuh to collect and analyze endpoint telemetry from Linux and Windows servers, integrating Falco, auditd, and Sysmon for detection testing.
Mermaid
Curated red team toolkit catalog — 251 tools, 22 categories, 64-step engagement workflow, weekly PoC tracker. Excel + GitHub-rendered.
Python
Transparent, reproducible pipeline that turns the daily CVE firehose into actionable Markdown cards. Ingests NVD + EPSS + CISA KEV, triages with deterministic rules or opt-in AI (Anthropic/Ollama), emits cards with primary-source links.
Python Dockerfile Shell YARA
CLI-first, skill-driven web research for AI agents and terminal users.
JavaScript Python
None
Shell Nix Just TypeScript CSS Kotlin
MCP server for Claude — audit open-source dependencies for known vulnerabilities
anthropic claude mcp mcp-server osv python security vulnerability-scanner
Python
None
HTML JavaScript TypeScript CSS
Free CVE prioritization CLI by AIS Labs
Python
None
Autonomous cybersecurity threat intelligence agent — port scan, WHOIS, DNS, VirusTotal & AI-powered analysis with IOC extraction and cross-investigation memory.
agentic ai cybersecurity flask ioc llm portscan python threat-intelligence
Procfile Python CSS JavaScript HTML
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-3094 vulnerability anywhere in the article.

-
Krypt3ia
Cyber Supply-Chain Attacks: Early Internet to Today
Executive assessment Cyber supply-chain attacks did not originate with computers. They are part of a much older strategic logic rooted in warfare, trade, logistics, and trust manipulation. Across hist ... Read more

-
Kaspersky
The dangers of telehealth: data breaches, phishing, and spam | Kaspersky official blog
privacy Telehealth services and apps are blowing up in popularity right now, making the availability of medical services better than ever. But just how safe is telemedicine, and what kind of risks doe ... Read more

-
CybersecurityNews
Red Hat Warns of Malware Code Embedded in Popular Linux Tool Allow Unauthorized Access to Systems
Red Hat has issued a critical security warning regarding malicious code discovered in recent versions of the “xz” compression tools and libraries. Tracked as CVE-2024-3094, this highly sophisticated s ... Read more

-
Kaspersky
Mental health apps are leaking your private thoughts. How do you protect yourself? | Kaspersky official blog
In February 2026, the cybersecurity firm Oversecured published a report that makes you want to factory reset your phone and move into a remote cabin in the woods. Researchers audited 10 popular Androi ... Read more
-
The Cyber Express
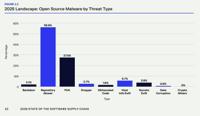
Malicious Open Source Software Packages Neared 500,000 in 2025
Malicious open source software packages have become a critical problem threatening the software supply chain. That’s one of the major takeaways of a new report titled “State of the Software Supply Cha ... Read more

-
Daily CyberSecurity
Critical XZ Backdoor Still Lurks in Docker Images, Posing Supply Chain Risk
The backdoor vulnerability in XZ-Utils first came to light in March 2024, and had it not been discovered in time, it could have posed a grave security threat to the entire technology sector. Yet, even ... Read more

-
BleepingComputer
Docker Hub still hosts dozens of Linux images with the XZ backdoor
The XZ-Utils backdoor, first discovered in March 2024, is still present in at least 35 Linux images on Docker Hub, potentially putting users, organizations, and their data at risk. Docker Hub is the o ... Read more

-
The Hacker News
Researchers Spot XZ Utils Backdoor in Dozens of Docker Hub Images, Fueling Supply Chain Risks
Aug 12, 2025Ravie LakshmananMalware / Container Security New research has uncovered Docker images on Docker Hub that contain the infamous XZ Utils backdoor, more than a year after the discovery of t ... Read more

-
Help Net Security
PRevent: Open-source tool to detect malicious code in pull requests
Apiiro security researchers have released open source tools that can help organizations detect malicious code as part of their software development lifecycle: PRevent (a scanner for pull requests), an ... Read more

-
Kaspersky
The biggest supply chain attacks in 2024 | Kaspersky official blog
A supply-chain attack can totally thwart all a targeted company’s efforts to protect its infrastructure. Preventing such attacks is extremely difficult because a significant portion of an attack occur ... Read more

-
The Cyber Express
Cybersecurity in 2025: Shadow AI, Deepfakes, and the Next Wave of Threats
As we step into 2025, the cybersecurity landscape is evolving at an unprecedented pace. The frequency of cyberattacks continues to rise, with organizations facing an average of 1,308 attacks per week ... Read more

-
Kaspersky
Trusted-relationship cyberattacks and their prevention
supply chain Attacks on companies via their suppliers and contractors are becoming increasingly widespread. How can you manage this risk? January 13, 2025 The old saying, “A chain is only as strong as ... Read more

-
The Cyber Express
Critical Veeam Vulnerabilities Expose Service Provider Console to Cyber Risks
Veeam has published a critical advisory regarding severe vulnerabilities affecting its Veeam Service Provider Console (VSPC), particularly impacting version 8.1.0.21377 and earlier builds from version ... Read more

-
Dark Reading
Lessons From OSC&R on Protecting the Software Supply Chain
Neatsun Ziv, CEO & Co-Founder, Ox SecurityNovember 15, 20245 Min ReadSource: Andrey Kryuchkov via Alamy Stock PhotoCOMMENTARYThe complexity of today's software development — a mix of open source and t ... Read more

-
The Hacker News
Leveraging Wazuh for Zero Trust security
Zero Trust security changes how organizations handle security by doing away with implicit trust while continuously analyzing and validating access requests. Contrary to perimeter-based security, users ... Read more

-
BleepingComputer
How open source SIEM and XDR tackle evolving threats
In today's cybersecurity landscape, evolving threats require security solutions that match the sophistication of modern threats. As businesses rapidly adopt emerging technologies, their exposure to cy ... Read more

-
Kaspersky
IT threat evolution Q2 2024
Targeted attacks XZ backdoor: a supply chain attack in the making On March 29, a message on the Openwall oss-security mailing list announced the discovery of a backdoor in XZ, a compression utility in ... Read more

-
Kaspersky
APT trends report Q2 2024
For over six years now, Kaspersky’s Global Research and Analysis Team (GReAT) has been sharing quarterly updates on advanced persistent threats (APTs). These summaries draw on our threat intelligence ... Read more
The following table lists the changes that have been made to the
CVE-2024-3094 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Aug. 19, 2025
Action Type Old Value New Value Added Reference https://www.binarly.io/blog/persistent-risk-xz-utils-backdoor-still-lurking-in-docker-images -
CVE Modified by [email protected]
Feb. 06, 2025
Action Type Old Value New Value Removed Reference http://www.openwall.com/lists/oss-security/2024/03/29/10 Removed Reference http://www.openwall.com/lists/oss-security/2024/03/29/12 Removed Reference http://www.openwall.com/lists/oss-security/2024/03/29/4 Removed Reference http://www.openwall.com/lists/oss-security/2024/03/29/5 Removed Reference http://www.openwall.com/lists/oss-security/2024/03/29/8 Removed Reference http://www.openwall.com/lists/oss-security/2024/03/30/12 Removed Reference http://www.openwall.com/lists/oss-security/2024/03/30/27 Removed Reference http://www.openwall.com/lists/oss-security/2024/03/30/36 Removed Reference http://www.openwall.com/lists/oss-security/2024/03/30/5 Removed Reference http://www.openwall.com/lists/oss-security/2024/04/16/5 Removed Reference https://ariadne.space/2024/04/02/the-xz-utils-backdoor-is-a-symptom-of-a-larger-problem/ Removed Reference https://arstechnica.com/security/2024/03/backdoor-found-in-widely-used-linux-utility-breaks-encrypted-ssh-connections/ Removed Reference https://aws.amazon.com/security/security-bulletins/AWS-2024-002/ Removed Reference https://blog.netbsd.org/tnf/entry/statement_on_backdoor_in_xz Removed Reference https://boehs.org/node/everything-i-know-about-the-xz-backdoor Removed Reference https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1068024 Removed Reference https://bugs.gentoo.org/928134 Removed Reference https://bugzilla.suse.com/show_bug.cgi?id=1222124 Removed Reference https://discourse.nixos.org/t/cve-2024-3094-malicious-code-in-xz-5-6-0-and-5-6-1-tarballs/42405 Removed Reference https://gist.github.com/thesamesam/223949d5a074ebc3dce9ee78baad9e27 Removed Reference https://github.com/advisories/GHSA-rxwq-x6h5-x525 Removed Reference https://github.com/amlweems/xzbot Removed Reference https://github.com/karcherm/xz-malware Removed Reference https://gynvael.coldwind.pl/?lang=en&id=782 Removed Reference https://lists.debian.org/debian-security-announce/2024/msg00057.html Removed Reference https://lists.freebsd.org/archives/freebsd-security/2024-March/000248.html Removed Reference https://lwn.net/Articles/967180/ Removed Reference https://news.ycombinator.com/item?id=39865810 Removed Reference https://news.ycombinator.com/item?id=39877267 Removed Reference https://news.ycombinator.com/item?id=39895344 Removed Reference https://openssf.org/blog/2024/03/30/xz-backdoor-cve-2024-3094/ Removed Reference https://research.swtch.com/xz-script Removed Reference https://research.swtch.com/xz-timeline Removed Reference https://security.alpinelinux.org/vuln/CVE-2024-3094 Removed Reference https://security.archlinux.org/CVE-2024-3094 Removed Reference https://security.netapp.com/advisory/ntap-20240402-0001/ Removed Reference https://security-tracker.debian.org/tracker/CVE-2024-3094 Removed Reference https://tukaani.org/xz-backdoor/ Removed Reference https://twitter.com/debian/status/1774219194638409898 Removed Reference https://twitter.com/infosecb/status/1774595540233167206 Removed Reference https://twitter.com/infosecb/status/1774597228864139400 Removed Reference https://twitter.com/LetsDefendIO/status/1774804387417751958 Removed Reference https://ubuntu.com/security/CVE-2024-3094 Removed Reference https://www.cisa.gov/news-events/alerts/2024/03/29/reported-supply-chain-compromise-affecting-xz-utils-data-compression-library-cve-2024-3094 Removed Reference https://www.darkreading.com/vulnerabilities-threats/are-you-affected-by-the-backdoor-in-xz-utils Removed Reference https://www.kali.org/blog/about-the-xz-backdoor/ Removed Reference https://www.tenable.com/blog/frequently-asked-questions-cve-2024-3094-supply-chain-backdoor-in-xz-utils Removed Reference https://www.theregister.com/2024/03/29/malicious_backdoor_xz/ Removed Reference https://www.vicarius.io/vsociety/vulnerabilities/cve-2024-3094 Removed Reference https://xeiaso.net/notes/2024/xz-vuln/ Removed Reference Type https://arstechnica.com/security/2024/03/backdoor-found-in-widely-used-linux-utility-breaks-encrypted-ssh-connections/ Types: Third Party Advisory Removed Reference Type https://aws.amazon.com/security/security-bulletins/AWS-2024-002/ Types: Third Party Advisory Removed Reference Type https://boehs.org/node/everything-i-know-about-the-xz-backdoor Types: Third Party Advisory Removed Reference Type https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1068024 Types: Mailing List, Vendor Advisory Removed Reference Type https://bugs.gentoo.org/928134 Types: Issue Tracking, Third Party Advisory Removed Reference Type https://bugzilla.suse.com/show_bug.cgi?id=1222124 Types: Issue Tracking, Third Party Advisory Removed Reference Type https://discourse.nixos.org/t/cve-2024-3094-malicious-code-in-xz-5-6-0-and-5-6-1-tarballs/42405 Types: Third Party Advisory Removed Reference Type https://gist.github.com/thesamesam/223949d5a074ebc3dce9ee78baad9e27 Types: Third Party Advisory Removed Reference Type https://github.com/advisories/GHSA-rxwq-x6h5-x525 Types: Third Party Advisory Removed Reference Type https://github.com/karcherm/xz-malware Types: Third Party Advisory Removed Reference Type https://gynvael.coldwind.pl/?lang=en&id=782 Types: Technical Description, Third Party Advisory Removed Reference Type https://lists.debian.org/debian-security-announce/2024/msg00057.html Types: Mailing List, Third Party Advisory Removed Reference Type https://lists.freebsd.org/archives/freebsd-security/2024-March/000248.html Types: Third Party Advisory Removed Reference Type https://lwn.net/Articles/967180/ Types: Issue Tracking, Third Party Advisory Removed Reference Type https://news.ycombinator.com/item?id=39865810 Types: Issue Tracking, Third Party Advisory Removed Reference Type https://news.ycombinator.com/item?id=39877267 Types: Issue Tracking Removed Reference Type https://openssf.org/blog/2024/03/30/xz-backdoor-cve-2024-3094/ Types: Third Party Advisory Removed Reference Type https://security.alpinelinux.org/vuln/CVE-2024-3094 Types: Third Party Advisory Removed Reference Type https://security.archlinux.org/CVE-2024-3094 Types: Third Party Advisory Removed Reference Type https://security-tracker.debian.org/tracker/CVE-2024-3094 Types: Third Party Advisory Removed Reference Type https://tukaani.org/xz-backdoor/ Types: Issue Tracking, Vendor Advisory Removed Reference Type https://twitter.com/debian/status/1774219194638409898 Types: Press/Media Coverage Removed Reference Type https://twitter.com/infosecb/status/1774595540233167206 Types: Press/Media Coverage Removed Reference Type https://twitter.com/infosecb/status/1774597228864139400 Types: Press/Media Coverage Removed Reference Type https://twitter.com/LetsDefendIO/status/1774804387417751958 Types: Third Party Advisory Removed Reference Type https://ubuntu.com/security/CVE-2024-3094 Types: Third Party Advisory Removed Reference Type https://www.cisa.gov/news-events/alerts/2024/03/29/reported-supply-chain-compromise-affecting-xz-utils-data-compression-library-cve-2024-3094 Types: Third Party Advisory, US Government Resource Removed Reference Type https://www.darkreading.com/vulnerabilities-threats/are-you-affected-by-the-backdoor-in-xz-utils Types: Third Party Advisory Removed Reference Type https://www.tenable.com/blog/frequently-asked-questions-cve-2024-3094-supply-chain-backdoor-in-xz-utils Types: Third Party Advisory Removed Reference Type https://www.theregister.com/2024/03/29/malicious_backdoor_xz/ Types: Press/Media Coverage Removed Reference Type https://xeiaso.net/notes/2024/xz-vuln/ Types: Third Party Advisory -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://www.openwall.com/lists/oss-security/2024/03/29/10 Added Reference http://www.openwall.com/lists/oss-security/2024/03/29/12 Added Reference http://www.openwall.com/lists/oss-security/2024/03/29/4 Added Reference http://www.openwall.com/lists/oss-security/2024/03/29/5 Added Reference http://www.openwall.com/lists/oss-security/2024/03/29/8 Added Reference http://www.openwall.com/lists/oss-security/2024/03/30/12 Added Reference http://www.openwall.com/lists/oss-security/2024/03/30/27 Added Reference http://www.openwall.com/lists/oss-security/2024/03/30/36 Added Reference http://www.openwall.com/lists/oss-security/2024/03/30/5 Added Reference http://www.openwall.com/lists/oss-security/2024/04/16/5 Added Reference https://access.redhat.com/security/cve/CVE-2024-3094 Added Reference https://ariadne.space/2024/04/02/the-xz-utils-backdoor-is-a-symptom-of-a-larger-problem/ Added Reference https://arstechnica.com/security/2024/03/backdoor-found-in-widely-used-linux-utility-breaks-encrypted-ssh-connections/ Added Reference https://aws.amazon.com/security/security-bulletins/AWS-2024-002/ Added Reference https://blog.netbsd.org/tnf/entry/statement_on_backdoor_in_xz Added Reference https://boehs.org/node/everything-i-know-about-the-xz-backdoor Added Reference https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1068024 Added Reference https://bugs.gentoo.org/928134 Added Reference https://bugzilla.redhat.com/show_bug.cgi?id=2272210 Added Reference https://bugzilla.suse.com/show_bug.cgi?id=1222124 Added Reference https://discourse.nixos.org/t/cve-2024-3094-malicious-code-in-xz-5-6-0-and-5-6-1-tarballs/42405 Added Reference https://gist.github.com/thesamesam/223949d5a074ebc3dce9ee78baad9e27 Added Reference https://github.com/advisories/GHSA-rxwq-x6h5-x525 Added Reference https://github.com/amlweems/xzbot Added Reference https://github.com/karcherm/xz-malware Added Reference https://gynvael.coldwind.pl/?lang=en&id=782 Added Reference https://lists.debian.org/debian-security-announce/2024/msg00057.html Added Reference https://lists.freebsd.org/archives/freebsd-security/2024-March/000248.html Added Reference https://lwn.net/Articles/967180/ Added Reference https://news.ycombinator.com/item?id=39865810 Added Reference https://news.ycombinator.com/item?id=39877267 Added Reference https://news.ycombinator.com/item?id=39895344 Added Reference https://openssf.org/blog/2024/03/30/xz-backdoor-cve-2024-3094/ Added Reference https://research.swtch.com/xz-script Added Reference https://research.swtch.com/xz-timeline Added Reference https://security.alpinelinux.org/vuln/CVE-2024-3094 Added Reference https://security.archlinux.org/CVE-2024-3094 Added Reference https://security.netapp.com/advisory/ntap-20240402-0001/ Added Reference https://security-tracker.debian.org/tracker/CVE-2024-3094 Added Reference https://tukaani.org/xz-backdoor/ Added Reference https://twitter.com/debian/status/1774219194638409898 Added Reference https://twitter.com/infosecb/status/1774595540233167206 Added Reference https://twitter.com/infosecb/status/1774597228864139400 Added Reference https://twitter.com/LetsDefendIO/status/1774804387417751958 Added Reference https://ubuntu.com/security/CVE-2024-3094 Added Reference https://www.cisa.gov/news-events/alerts/2024/03/29/reported-supply-chain-compromise-affecting-xz-utils-data-compression-library-cve-2024-3094 Added Reference https://www.darkreading.com/vulnerabilities-threats/are-you-affected-by-the-backdoor-in-xz-utils Added Reference https://www.kali.org/blog/about-the-xz-backdoor/ Added Reference https://www.openwall.com/lists/oss-security/2024/03/29/4 Added Reference https://www.redhat.com/en/blog/urgent-security-alert-fedora-41-and-rawhide-users Added Reference https://www.tenable.com/blog/frequently-asked-questions-cve-2024-3094-supply-chain-backdoor-in-xz-utils Added Reference https://www.theregister.com/2024/03/29/malicious_backdoor_xz/ Added Reference https://www.vicarius.io/vsociety/vulnerabilities/cve-2024-3094 Added Reference https://xeiaso.net/notes/2024/xz-vuln/ -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CVE Modified by [email protected]
May. 01, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. http://www.openwall.com/lists/oss-security/2024/03/29/12 [No types assigned] Added Reference Red Hat, Inc. http://www.openwall.com/lists/oss-security/2024/04/16/5 [No types assigned] -
CVE Modified by [email protected]
May. 01, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. http://www.openwall.com/lists/oss-security/2024/03/30/27 [No types assigned] Added Reference Red Hat, Inc. http://www.openwall.com/lists/oss-security/2024/03/29/10 [No types assigned] Added Reference Red Hat, Inc. http://www.openwall.com/lists/oss-security/2024/03/30/36 [No types assigned] Added Reference Red Hat, Inc. http://www.openwall.com/lists/oss-security/2024/03/29/8 [No types assigned] Added Reference Red Hat, Inc. http://www.openwall.com/lists/oss-security/2024/03/30/5 [No types assigned] Added Reference Red Hat, Inc. http://www.openwall.com/lists/oss-security/2024/03/29/5 [No types assigned] Added Reference Red Hat, Inc. http://www.openwall.com/lists/oss-security/2024/03/29/4 [No types assigned] -
CVE Modified by [email protected]
May. 01, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. http://www.openwall.com/lists/oss-security/2024/03/30/12 [No types assigned] -
CVE Modified by [email protected]
Apr. 12, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://blog.netbsd.org/tnf/entry/statement_on_backdoor_in_xz [No types assigned] -
CVE Modified by [email protected]
Apr. 03, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://ariadne.space/2024/04/02/the-xz-utils-backdoor-is-a-symptom-of-a-larger-problem/ [No types assigned] Added Reference Red Hat, Inc. https://research.swtch.com/xz-timeline [No types assigned] Added Reference Red Hat, Inc. https://research.swtch.com/xz-script [No types assigned] -
CVE Modified by [email protected]
Apr. 03, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://www.kali.org/blog/about-the-xz-backdoor/ [No types assigned] -
CVE Modified by [email protected]
Apr. 02, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://security.netapp.com/advisory/ntap-20240402-0001/ [No types assigned] -
CVE Modified by [email protected]
Apr. 01, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://github.com/amlweems/xzbot [No types assigned] Added Reference Red Hat, Inc. https://news.ycombinator.com/item?id=39895344 [No types assigned] Added Reference Red Hat, Inc. https://www.vicarius.io/vsociety/vulnerabilities/cve-2024-3094 [No types assigned] -
Initial Analysis by [email protected]
Apr. 01, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H Changed Reference Type https://access.redhat.com/security/cve/CVE-2024-3094 No Types Assigned https://access.redhat.com/security/cve/CVE-2024-3094 Vendor Advisory Changed Reference Type https://arstechnica.com/security/2024/03/backdoor-found-in-widely-used-linux-utility-breaks-encrypted-ssh-connections/ No Types Assigned https://arstechnica.com/security/2024/03/backdoor-found-in-widely-used-linux-utility-breaks-encrypted-ssh-connections/ Third Party Advisory Changed Reference Type https://aws.amazon.com/security/security-bulletins/AWS-2024-002/ No Types Assigned https://aws.amazon.com/security/security-bulletins/AWS-2024-002/ Third Party Advisory Changed Reference Type https://boehs.org/node/everything-i-know-about-the-xz-backdoor No Types Assigned https://boehs.org/node/everything-i-know-about-the-xz-backdoor Third Party Advisory Changed Reference Type https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1068024 No Types Assigned https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1068024 Mailing List, Vendor Advisory Changed Reference Type https://bugs.gentoo.org/928134 No Types Assigned https://bugs.gentoo.org/928134 Issue Tracking, Third Party Advisory Changed Reference Type https://bugzilla.redhat.com/show_bug.cgi?id=2272210 No Types Assigned https://bugzilla.redhat.com/show_bug.cgi?id=2272210 Issue Tracking, Vendor Advisory Changed Reference Type https://bugzilla.suse.com/show_bug.cgi?id=1222124 No Types Assigned https://bugzilla.suse.com/show_bug.cgi?id=1222124 Issue Tracking, Third Party Advisory Changed Reference Type https://discourse.nixos.org/t/cve-2024-3094-malicious-code-in-xz-5-6-0-and-5-6-1-tarballs/42405 No Types Assigned https://discourse.nixos.org/t/cve-2024-3094-malicious-code-in-xz-5-6-0-and-5-6-1-tarballs/42405 Third Party Advisory Changed Reference Type https://gist.github.com/thesamesam/223949d5a074ebc3dce9ee78baad9e27 No Types Assigned https://gist.github.com/thesamesam/223949d5a074ebc3dce9ee78baad9e27 Third Party Advisory Changed Reference Type https://github.com/advisories/GHSA-rxwq-x6h5-x525 No Types Assigned https://github.com/advisories/GHSA-rxwq-x6h5-x525 Third Party Advisory Changed Reference Type https://github.com/karcherm/xz-malware No Types Assigned https://github.com/karcherm/xz-malware Third Party Advisory Changed Reference Type https://gynvael.coldwind.pl/?lang=en&id=782 No Types Assigned https://gynvael.coldwind.pl/?lang=en&id=782 Technical Description, Third Party Advisory Changed Reference Type https://lists.debian.org/debian-security-announce/2024/msg00057.html No Types Assigned https://lists.debian.org/debian-security-announce/2024/msg00057.html Mailing List, Third Party Advisory Changed Reference Type https://lists.freebsd.org/archives/freebsd-security/2024-March/000248.html No Types Assigned https://lists.freebsd.org/archives/freebsd-security/2024-March/000248.html Third Party Advisory Changed Reference Type https://lwn.net/Articles/967180/ No Types Assigned https://lwn.net/Articles/967180/ Issue Tracking, Third Party Advisory Changed Reference Type https://news.ycombinator.com/item?id=39865810 No Types Assigned https://news.ycombinator.com/item?id=39865810 Issue Tracking, Third Party Advisory Changed Reference Type https://news.ycombinator.com/item?id=39877267 No Types Assigned https://news.ycombinator.com/item?id=39877267 Issue Tracking Changed Reference Type https://openssf.org/blog/2024/03/30/xz-backdoor-cve-2024-3094/ No Types Assigned https://openssf.org/blog/2024/03/30/xz-backdoor-cve-2024-3094/ Third Party Advisory Changed Reference Type https://security.alpinelinux.org/vuln/CVE-2024-3094 No Types Assigned https://security.alpinelinux.org/vuln/CVE-2024-3094 Third Party Advisory Changed Reference Type https://security.archlinux.org/CVE-2024-3094 No Types Assigned https://security.archlinux.org/CVE-2024-3094 Third Party Advisory Changed Reference Type https://security-tracker.debian.org/tracker/CVE-2024-3094 No Types Assigned https://security-tracker.debian.org/tracker/CVE-2024-3094 Third Party Advisory Changed Reference Type https://tukaani.org/xz-backdoor/ No Types Assigned https://tukaani.org/xz-backdoor/ Issue Tracking, Vendor Advisory Changed Reference Type https://twitter.com/debian/status/1774219194638409898 No Types Assigned https://twitter.com/debian/status/1774219194638409898 Press/Media Coverage Changed Reference Type https://twitter.com/infosecb/status/1774595540233167206 No Types Assigned https://twitter.com/infosecb/status/1774595540233167206 Press/Media Coverage Changed Reference Type https://twitter.com/infosecb/status/1774597228864139400 No Types Assigned https://twitter.com/infosecb/status/1774597228864139400 Press/Media Coverage Changed Reference Type https://twitter.com/LetsDefendIO/status/1774804387417751958 No Types Assigned https://twitter.com/LetsDefendIO/status/1774804387417751958 Third Party Advisory Changed Reference Type https://ubuntu.com/security/CVE-2024-3094 No Types Assigned https://ubuntu.com/security/CVE-2024-3094 Third Party Advisory Changed Reference Type https://www.cisa.gov/news-events/alerts/2024/03/29/reported-supply-chain-compromise-affecting-xz-utils-data-compression-library-cve-2024-3094 No Types Assigned https://www.cisa.gov/news-events/alerts/2024/03/29/reported-supply-chain-compromise-affecting-xz-utils-data-compression-library-cve-2024-3094 Third Party Advisory, US Government Resource Changed Reference Type https://www.darkreading.com/vulnerabilities-threats/are-you-affected-by-the-backdoor-in-xz-utils No Types Assigned https://www.darkreading.com/vulnerabilities-threats/are-you-affected-by-the-backdoor-in-xz-utils Third Party Advisory Changed Reference Type https://www.openwall.com/lists/oss-security/2024/03/29/4 No Types Assigned https://www.openwall.com/lists/oss-security/2024/03/29/4 Mailing List Changed Reference Type https://www.redhat.com/en/blog/urgent-security-alert-fedora-41-and-rawhide-users No Types Assigned https://www.redhat.com/en/blog/urgent-security-alert-fedora-41-and-rawhide-users Vendor Advisory Changed Reference Type https://www.tenable.com/blog/frequently-asked-questions-cve-2024-3094-supply-chain-backdoor-in-xz-utils No Types Assigned https://www.tenable.com/blog/frequently-asked-questions-cve-2024-3094-supply-chain-backdoor-in-xz-utils Third Party Advisory Changed Reference Type https://www.theregister.com/2024/03/29/malicious_backdoor_xz/ No Types Assigned https://www.theregister.com/2024/03/29/malicious_backdoor_xz/ Press/Media Coverage Changed Reference Type https://xeiaso.net/notes/2024/xz-vuln/ No Types Assigned https://xeiaso.net/notes/2024/xz-vuln/ Third Party Advisory Added CPE Configuration OR *cpe:2.3:a:tukaani:xz:5.6.0:*:*:*:*:*:*:* *cpe:2.3:a:tukaani:xz:5.6.1:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Apr. 01, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://twitter.com/LetsDefendIO/status/1774804387417751958 [No types assigned] -
CVE Modified by [email protected]
Apr. 01, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://ubuntu.com/security/CVE-2024-3094 [No types assigned] Added Reference Red Hat, Inc. https://github.com/advisories/GHSA-rxwq-x6h5-x525 [No types assigned] Added Reference Red Hat, Inc. https://bugs.gentoo.org/928134 [No types assigned] Added Reference Red Hat, Inc. https://lists.debian.org/debian-security-announce/2024/msg00057.html [No types assigned] Added Reference Red Hat, Inc. https://twitter.com/debian/status/1774219194638409898 [No types assigned] Added Reference Red Hat, Inc. https://twitter.com/infosecb/status/1774597228864139400 [No types assigned] Added Reference Red Hat, Inc. https://twitter.com/infosecb/status/1774595540233167206 [No types assigned] Added Reference Red Hat, Inc. https://gist.github.com/thesamesam/223949d5a074ebc3dce9ee78baad9e27 [No types assigned] Added Reference Red Hat, Inc. https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=1068024 [No types assigned] Added Reference Red Hat, Inc. https://github.com/karcherm/xz-malware [No types assigned] Added Reference Red Hat, Inc. https://discourse.nixos.org/t/cve-2024-3094-malicious-code-in-xz-5-6-0-and-5-6-1-tarballs/42405 [No types assigned] Added Reference Red Hat, Inc. https://xeiaso.net/notes/2024/xz-vuln/ [No types assigned] Added Reference Red Hat, Inc. https://lwn.net/Articles/967180/ [No types assigned] Added Reference Red Hat, Inc. https://boehs.org/node/everything-i-know-about-the-xz-backdoor [No types assigned] Added Reference Red Hat, Inc. https://tukaani.org/xz-backdoor/ [No types assigned] -
CVE Modified by [email protected]
Mar. 31, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://news.ycombinator.com/item?id=39877267 [No types assigned] Added Reference Red Hat, Inc. https://gynvael.coldwind.pl/?lang=en&id=782 [No types assigned] -
CVE Modified by [email protected]
Mar. 30, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://lists.freebsd.org/archives/freebsd-security/2024-March/000248.html [No types assigned] -
CVE Modified by [email protected]
Mar. 30, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://news.ycombinator.com/item?id=39865810 [No types assigned] Added Reference Red Hat, Inc. https://arstechnica.com/security/2024/03/backdoor-found-in-widely-used-linux-utility-breaks-encrypted-ssh-connections/ [No types assigned] Added Reference Red Hat, Inc. https://www.theregister.com/2024/03/29/malicious_backdoor_xz/ [No types assigned] Added Reference Red Hat, Inc. https://www.cisa.gov/news-events/alerts/2024/03/29/reported-supply-chain-compromise-affecting-xz-utils-data-compression-library-cve-2024-3094 [No types assigned] Added Reference Red Hat, Inc. https://www.darkreading.com/vulnerabilities-threats/are-you-affected-by-the-backdoor-in-xz-utils [No types assigned] Added Reference Red Hat, Inc. https://aws.amazon.com/security/security-bulletins/AWS-2024-002/ [No types assigned] Added Reference Red Hat, Inc. https://www.tenable.com/blog/frequently-asked-questions-cve-2024-3094-supply-chain-backdoor-in-xz-utils [No types assigned] Added Reference Red Hat, Inc. https://openssf.org/blog/2024/03/30/xz-backdoor-cve-2024-3094/ [No types assigned] Added Reference Red Hat, Inc. https://bugzilla.suse.com/show_bug.cgi?id=1222124 [No types assigned] Added Reference Red Hat, Inc. https://security.archlinux.org/CVE-2024-3094 [No types assigned] Added Reference Red Hat, Inc. https://security.alpinelinux.org/vuln/CVE-2024-3094 [No types assigned] Added Reference Red Hat, Inc. https://security-tracker.debian.org/tracker/CVE-2024-3094 [No types assigned] -
CVE Modified by [email protected]
Mar. 29, 2024
Action Type Old Value New Value Changed Description Malicious code was discovered in the upstream tarballs of xz, starting with version 5.6.0. The tarballs included extra .m4 files, which contained instructions for building with automake that did not exist in the repository. These instructions, through a series of complex obfuscations, extract a prebuilt object file from one of the test archives, which is then used to modify specific functions in the code while building the liblzma package. This issue results in liblzma being used by additional software, like sshd, to provide functionality that will be interpreted by the modified functions. Malicious code was discovered in the upstream tarballs of xz, starting with version 5.6.0. Through a series of complex obfuscations, the liblzma build process extracts a prebuilt object file from a disguised test file existing in the source code, which is then used to modify specific functions in the liblzma code. This results in a modified liblzma library that can be used by any software linked against this library, intercepting and modifying the data interaction with this library. -
CVE Received by [email protected]
Mar. 29, 2024
Action Type Old Value New Value Added Description Malicious code was discovered in the upstream tarballs of xz, starting with version 5.6.0. The tarballs included extra .m4 files, which contained instructions for building with automake that did not exist in the repository. These instructions, through a series of complex obfuscations, extract a prebuilt object file from one of the test archives, which is then used to modify specific functions in the code while building the liblzma package. This issue results in liblzma being used by additional software, like sshd, to provide functionality that will be interpreted by the modified functions. Added Reference Red Hat, Inc. https://access.redhat.com/security/cve/CVE-2024-3094 [No types assigned] Added Reference Red Hat, Inc. https://bugzilla.redhat.com/show_bug.cgi?id=2272210 [No types assigned] Added Reference Red Hat, Inc. https://www.openwall.com/lists/oss-security/2024/03/29/4 [No types assigned] Added Reference Red Hat, Inc. https://www.redhat.com/en/blog/urgent-security-alert-fedora-41-and-rawhide-users [No types assigned] Added CWE Red Hat, Inc. CWE-506 Added CVSS V3.1 Red Hat, Inc. AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H