CVE-2024-31449
Lua library commands may lead to stack overflow and RCE in Redis
Description
Redis is an open source, in-memory database that persists on disk. An authenticated user may use a specially crafted Lua script to trigger a stack buffer overflow in the bit library, which may potentially lead to remote code execution. The problem exists in all versions of Redis with Lua scripting. This problem has been fixed in Redis versions 6.2.16, 7.2.6, and 7.4.1. Users are advised to upgrade. There are no known workarounds for this vulnerability.
INFO
Published Date :
Oct. 7, 2024, 8:15 p.m.
Last Modified :
Sept. 4, 2025, 7:03 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Update the Redis package to a patched version.
- Update any related development or documentation packages.
Public PoC/Exploit Available at Github
CVE-2024-31449 has a 6 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-31449.
| URL | Resource |
|---|---|
| https://github.com/redis/redis/commit/1f7c148be2cbacf7d50aa461c58b871e87cc5ed9 | Patch |
| https://github.com/redis/redis/security/advisories/GHSA-whxg-wx83-85p5 | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-31449 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-31449
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
A Comprehensive Pentest Suite for Redis.
automation cli-tool exploits golang golang-cli golang-package goreleaser pentest-tool pentesting-tools redis scanner security-tools vulnerability-scanner scan-tool bugbounty cicd
Makefile Go
None
Dockerfile Python
None
Dockerfile JavaScript Shell
None
HTML Python Shell
一个 CVE 漏洞预警知识库,无 exp/poc,部分包含修复方案。A knowledge base of CVE security vulnerability, no PoCs/exploits.
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-31449 vulnerability anywhere in the article.

-
Daily CyberSecurity
Redis Reintroduces Open-Source AGPL Alongside SSPL Licensing
In March 2024, the widely adopted database caching solution Redis announced its transition to the Server Side Public License (SSPL)—a license that, while offering source code access, is not recognized ... Read more

-
Daily CyberSecurity
Redis Vulnerability Exposes Servers to Denial-of-Service Attacks
A high-severity vulnerability has been discovered in Redis, the popular open-source in-memory data structure store, which could allow unauthenticated users to exhaust server memory and cause a Denial- ... Read more

-
Cybersecurity News
0patch Uncovers and Patches New Windows Zero-Day Vulnerability, Microsoft Scrambles to Re-Fix Flaw
Security researchers at 0patch have discovered a new zero-day vulnerability in Microsoft Windows, exposing users to potential credential theft. This revelation comes on the heels of Microsoft’s attemp ... Read more

-
Cybersecurity News
Critical Vulnerabilities in Bitdefender Total Security Expose Users to Man-in-the-Middle Attacks
Bitdefender, a leading global cybersecurity technology company, has issued an urgent advisory regarding three critical vulnerabilities discovered in the HTTPS scanning feature of its Total Security pr ... Read more

-
Cybersecurity News
SideWinder APT: A Decade of Evolution and Global Expansion
The SideWinder Advanced Persistent Threat (APT) group, also known as T-APT-04 or RattleSnake, has been a relentless actor in the global cyber espionage landscape since its emergence in 2012. Though in ... Read more

-
Cybersecurity News
Critical Vulnerabilities Found in mbNET.mini Industrial Routers Could Allow for Full System Takeover
A security advisory issued by CERT@VDE has revealed multiple critical vulnerabilities in the mbNET.mini industrial router, a widely used device designed for secure remote access to industrial machines ... Read more

-
Cybersecurity News
Don’t Get Tricked: RTF Files Are the Latest Weapon in Phishing Attacks
Image: IronscalesIn 2024, phishing attacks have taken on a new and dangerous form, utilizing Rich Text Format (RTF) files in creative and highly deceptive ways. According to a recent report by Audian ... Read more

-
Cybersecurity News
Ivanti Patches CSA Appliance Against Vulnerabilities, Including Actively Exploited Flaws
Ivanti has recently released urgent security updates for its Cloud Services Appliance (CSA) to address multiple vulnerabilities, including one that is actively being exploited in the wild. The company ... Read more
-
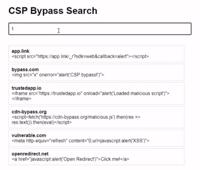
Cybersecurity News
CSP Bypass: A New Open-Source Tool for Ethical Hackers to Overcome Content Security Policies
Renowned security researcher Renniepak, the founder of Hacker Hideout, has launched an open-source tool called CSP Bypass. This tool is designed to assist ethical hackers and security researchers in i ... Read more
The following table lists the changes that have been made to the
CVE-2024-31449 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Reanalysis by [email protected]
Sep. 04, 2025
Action Type Old Value New Value Changed CPE Configuration OR *cpe:2.3:a:redis:redis:*:*:*:*:*:*:*:* versions from (including) 2.8.18 up to (excluding) 6.2.16 *cpe:2.3:a:redis:redis:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (excluding) 7.2.6 *cpe:2.3:a:redis:redis:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.1 OR *cpe:2.3:a:redis:redis:*:*:*:*:*:*:*:* versions from (including) 2.8.18 up to (excluding) 6.2.16 *cpe:2.3:a:redis:redis:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (excluding) 7.2.6 *cpe:2.3:a:redis:redis:7.4.0:-:*:*:*:*:*:* *cpe:2.3:a:redis:redis:7.4.0:rc1:*:*:*:*:*:* *cpe:2.3:a:redis:redis:7.4.0:rc2:*:*:*:*:*:* Changed Reference Type GitHub, Inc.: https://github.com/redis/redis/security/advisories/GHSA-whxg-wx83-85p5 Types: Third Party Advisory GitHub, Inc.: https://github.com/redis/redis/security/advisories/GHSA-whxg-wx83-85p5 Types: Vendor Advisory -
Initial Analysis by [email protected]
Sep. 04, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Added CPE Configuration OR *cpe:2.3:a:redis:redis:*:*:*:*:*:*:*:* versions from (including) 2.8.18 up to (excluding) 6.2.16 *cpe:2.3:a:redis:redis:*:*:*:*:*:*:*:* versions from (including) 7.2.0 up to (excluding) 7.2.6 *cpe:2.3:a:redis:redis:*:*:*:*:*:*:*:* versions from (including) 7.4.0 up to (excluding) 7.4.1 Added Reference Type GitHub, Inc.: https://github.com/redis/redis/commit/1f7c148be2cbacf7d50aa461c58b871e87cc5ed9 Types: Patch Added Reference Type GitHub, Inc.: https://github.com/redis/redis/security/advisories/GHSA-whxg-wx83-85p5 Types: Third Party Advisory -
CVE Received by [email protected]
Oct. 07, 2024
Action Type Old Value New Value Added Description Redis is an open source, in-memory database that persists on disk. An authenticated user may use a specially crafted Lua script to trigger a stack buffer overflow in the bit library, which may potentially lead to remote code execution. The problem exists in all versions of Redis with Lua scripting. This problem has been fixed in Redis versions 6.2.16, 7.2.6, and 7.4.1. Users are advised to upgrade. There are no known workarounds for this vulnerability. Added Reference GitHub, Inc. https://github.com/redis/redis/security/advisories/GHSA-whxg-wx83-85p5 [No types assigned] Added Reference GitHub, Inc. https://github.com/redis/redis/commit/1f7c148be2cbacf7d50aa461c58b871e87cc5ed9 [No types assigned] Added CWE GitHub, Inc. CWE-20 Added CWE GitHub, Inc. CWE-121 Added CVSS V3.1 GitHub, Inc. AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H