CVE-2024-3721
TBK DVR-4104/DVR-4216 os command injection
Description
A vulnerability was found in TBK DVR-4104 and DVR-4216 up to 20240412 and classified as critical. This issue affects some unknown processing of the file /device.rsp?opt=sys&cmd=___S_O_S_T_R_E_A_MAX___. The manipulation of the argument mdb/mdc leads to os command injection. The attack may be initiated remotely. The exploit has been disclosed to the public and may be used. The identifier VDB-260573 was assigned to this vulnerability.
INFO
Published Date :
April 13, 2024, 12:15 p.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-3721
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
No affected product recoded yet
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 2.0 | MEDIUM | [email protected] | ||||
| CVSS 3.1 | MEDIUM | [email protected] |
Public PoC/Exploit Available at Github
CVE-2024-3721 has a 16 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-3721.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-3721 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-3721
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
HTML CSS JavaScript Shell
From the headlines to the SIEM: daily detection content built from public threat intel — Sigma, KQL, SPL, YARA — with attribution, ATT&CK mapping, and false-positive notes.
YARA Python Shell
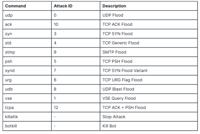
I will teach you how to "buy" a home IP for free,analyze CVE-2024-3721,launch a udp flood attack. please refer to the html file, not the README.md file.
HTML
None
None
C
POC on how mirai can target " CVE-2024-3721 " { TBK DVR-4104 and DVR-4216 }
Go
备份的漏洞库,3月开始我们来维护
None
CVE POC repo 자동 수집기
Python
None
None
HTML
wy876
Python
wy876 POC | wy876的poc仓库已删库,该项目为其仓库镜像
备份的漏洞库,3月开始我们来维护
漏洞文库 wiki.wy876.cn
HTML
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-3721 vulnerability anywhere in the article.
-
Daily CyberSecurity
Nexcorium Botnet Turns Unpatched DVRs into DDoS Foot Soldiers
Security researchers at FortiGuard Labs have uncovered a sophisticated campaign deploying Nexcorium, a multi-architecture Mirai variant that turns unpatched digital video recorders (DVRs) into foot so ... Read more

-
CybersecurityNews
Hackers Use CVE-2024-3721 to Infect TBK DVRs With Nexcorium DDoS Malware
A newly identified botnet campaign is actively exploiting a critical flaw in TBK digital video recorders to deploy a dangerous piece of malware known as Nexcorium, a Mirai-based threat built to launch ... Read more

-
CybersecurityNews
Nexcorium-Associated Mirai Variant Uses TBK DVR Exploit to Scale Botnet Operations
A new iteration of the notorious Mirai botnet, dubbed Nexcorium, has emerged in the wild, aggressively targeting internet-connected video recording devices. According to recent threat research publish ... Read more

-
The Hacker News
Mirai Variant Nexcorium Exploits CVE-2024-3721 to Hijack TBK DVRs for DDoS Botnet
Threat actors are exploiting security flaws in TBK DVR and end‑of‑life (EoL) TP-Link Wi-Fi routers to deploy Mirai-botnet variants on compromised devices, according to findings from Fortinet FortiGuar ... Read more

-
The Hacker News
ThreatsDay Bulletin: Spyware Alerts, Mirai Strikes, Docker Leaks, ValleyRAT Rootkit — and 20 More Stories
This week's cyber stories show how fast the online world can turn risky. Hackers are sneaking malware into movie downloads, browser add-ons, and even software updates people trust. Tech giants and gov ... Read more

-
CybersecurityNews
New Mirai Botnet Variant ‘Broadside’ Actively Attacking Users in the Wild
A sophisticated new variant of the Mirai botnet, named “Broadside,” has emerged as an active threat targeting maritime shipping companies and vessel operators. The malware exploits a critical vulnerab ... Read more

-
CybersecurityNews
Hackers Actively Exploiting IoT Vulnerabilities to Deploy New ShadowV2 Malware
During late October 2025, a new malware campaign dubbed ShadowV2 emerged, coinciding with a global AWS disruption. This sophisticated threat actively exploits vulnerabilities in IoT devices to assembl ... Read more

-
The Hacker News
ThreatsDay Bulletin: AI Malware, Voice Bot Flaws, Crypto Laundering, IoT Attacks — and 20 More Stories
Hackers have been busy again this week. From fake voice calls and AI-powered malware to huge money-laundering busts and new scams, there's a lot happening in the cyber world.Criminals are getting crea ... Read more

-
BleepingComputer
New ShadowV2 botnet malware used AWS outage as a test opportunity
A new Mirai-based botnet malware named ‘ShadowV2’ has been observed targeting IoT devices from D-Link, TP-Link, and other vendors with exploits for known vulnerabilities. Fortinet’s FortiGuard Labs re ... Read more

-
The Register
Botnet takes advantage of AWS outage to smack 28 countries
A Mirai-based botnet named ShadowV2 emerged during last October's widespread AWS outage, infecting IoT devices across industries and continents, likely serving as a "test run" for future attacks, acco ... Read more

-
CybersecurityNews
RondoDox Botnet Updated Their Arsenal with 650% More Exploits Targeting Enterprises
A sophisticated evolution of the RondoDox botnet has emerged with a staggering 650% increase in exploitation capabilities, marking a significant escalation in the threat landscape for both enterprise ... Read more

-
The Hacker News
Experts Reports Sharp Increase in Automated Botnet Attacks Targeting PHP Servers and IoT Devices
Oct 29, 2025Ravie LakshmananVulnerability / Internet of Things Cybersecurity researchers are calling attention to a spike in automated attacks targeting PHP servers, IoT devices, and cloud gateways ... Read more

-
CybersecurityNews
RondoDox Botnet Exploits 50+ Vulnerabilities to Attack Routers, CCTV Systems and Web Servers
Since its emergence in early 2025, RondoDox has rapidly become one of the most pervasive IoT-focused botnets in operation, targeting a wide range of network-connected devices—from consumer routers to ... Read more

-
Daily CyberSecurity
RondoDox Botnet Unleashed: New Malware Uses ‘Exploit Shotgun’ to Target 50+ Router and IoT Flaws
Trend Micro has uncovered a rapidly expanding botnet campaign dubbed RondoDox, which is targeting a wide spectrum of internet-exposed devices — from routers and DVRs to CCTV systems and industrial net ... Read more

-
The Register
RondoDox botnet fires 'exploit shotgun' at nearly every router and internet-connected home device
A new RondoDox botnet campaign uses an "exploit shotgun" - fire at everything, see what hits - to target 56 vulnerabilities across at least 30 different vendors' routers, DVRs, CCTV systems, web serve ... Read more

-
BleepingComputer
RondoDox botnet targets 56 n-day flaws in worldwide attacks
A new large-scale botnet called RondoDox is targeting 56 vulnerabilities in more than 30 distinct devices, including flaws first disclosed during Pwn2Own hacking competitions. The attacker focuses on ... Read more

-
Trend Micro
RondoDox: From Targeting Pwn2Own Vulnerabilities to Shotgunning Exploits
Cyber Threats Trend™ Research and ZDI Threat Hunters have identified a large-scale RondoDox botnet campaign exploiting over 50 vulnerabilities across more than 30 vendors, including flaws first seen i ... Read more

-
Kaspersky
Evolution of the PipeMagic backdoor: from the RansomExx incident to CVE-2025-29824
In April 2025, Microsoft patched 121 vulnerabilities in its products. According to the company, only one of them was being used in real-world attacks at the time the patch was released: CVE-2025-29824 ... Read more

-
Kaspersky
Driver of destruction: How a legitimate driver is being used to take down AV processes
Introduction In a recent incident response case in Brazil, we spotted intriguing new antivirus (AV) killer software that has been circulating in the wild since at least October 2024. This malicious ar ... Read more

-
Kaspersky
ToolShell: a story of five vulnerabilities in Microsoft SharePoint
On July 19–20, 2025, various security companies and national CERTs published alerts about active exploitation of on-premise SharePoint servers. According to the reports, observed attacks did not requi ... Read more
The following table lists the changes that have been made to the
CVE-2024-3721 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://github.com/netsecfish/tbk_dvr_command_injection Added Reference https://vuldb.com/?ctiid.260573 Added Reference https://vuldb.com/?id.260573 Added Reference https://vuldb.com/?submit.314969 -
CVE Modified by [email protected]
May. 17, 2024
Action Type Old Value New Value -
CVE Modified by [email protected]
May. 14, 2024
Action Type Old Value New Value -
CVE Received by [email protected]
Apr. 13, 2024
Action Type Old Value New Value Added Description A vulnerability was found in TBK DVR-4104 and DVR-4216 up to 20240412 and classified as critical. This issue affects some unknown processing of the file /device.rsp?opt=sys&cmd=___S_O_S_T_R_E_A_MAX___. The manipulation of the argument mdb/mdc leads to os command injection. The attack may be initiated remotely. The exploit has been disclosed to the public and may be used. The identifier VDB-260573 was assigned to this vulnerability. Added Reference VulDB https://vuldb.com/?id.260573 [No types assigned] Added Reference VulDB https://vuldb.com/?ctiid.260573 [No types assigned] Added Reference VulDB https://vuldb.com/?submit.314969 [No types assigned] Added Reference VulDB https://github.com/netsecfish/tbk_dvr_command_injection [No types assigned] Added CWE VulDB CWE-78 Added CVSS V2 VulDB (AV:N/AC:L/Au:S/C:P/I:P/A:P) Added CVSS V3.1 VulDB AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:L