CVE-2024-37285
Kibana arbitrary code execution via YAML deserialization
Description
A deserialization issue in Kibana can lead to arbitrary code execution when Kibana attempts to parse a YAML document containing a crafted payload. A successful attack requires a malicious user to have a combination of both specific Elasticsearch indices privileges https://www.elastic.co/guide/en/elasticsearch/reference/current/defining-roles.html#roles-indices-priv and Kibana privileges https://www.elastic.co/guide/en/fleet/current/fleet-roles-and-privileges.html assigned to them. The following Elasticsearch indices permissions are required * write privilege on the system indices .kibana_ingest* * The allow_restricted_indices flag is set to true Any of the following Kibana privileges are additionally required * Under Fleet the All privilege is granted * Under Integration the Read or All privilege is granted * Access to the fleet-setup privilege is gained through the Fleet Server’s service account token
INFO
Published Date :
Nov. 14, 2024, 5:15 p.m.
Last Modified :
Oct. 1, 2025, 6:36 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Upgrade to Kibana version 8.15.1 or later.
Public PoC/Exploit Available at Github
CVE-2024-37285 has a 1 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-37285.
| URL | Resource |
|---|---|
| https://discuss.elastic.co/t/kibana-8-15-1-security-update-esa-2024-27-esa-2024-28/366119 | Patch Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-37285 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-37285
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
一个 CVE 漏洞预警知识库,无 exp/poc,部分包含修复方案。A knowledge base of CVE security vulnerability, no PoCs/exploits.
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-37285 vulnerability anywhere in the article.

-
Daily CyberSecurity
CVE-2025-25014 (CVSS 9.1): Prototype Pollution in Kibana Opens Door to Code Execution
Elastic has issued a critical security advisory for Kibana, warning users of a vulnerability tracked as CVE-2025-25014. Scoring a CVSS of 9.1, this flaw stems from a prototype pollution vulnerability ... Read more

-
Daily CyberSecurity
Kibana Code Injection Vulnerability: Prototype Pollution Threat (CVE-2024-12556)
A newly disclosed vulnerability in Kibana, the popular open-source data visualization front-end for Elasticsearch, has been rated CVSS 8.7 due to its potential to allow remote code injection under spe ... Read more
-
Cybersecurity News
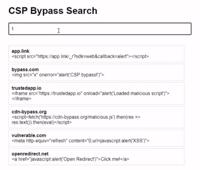
CSP Bypass: A New Open-Source Tool for Ethical Hackers to Overcome Content Security Policies
Renowned security researcher Renniepak, the founder of Hacker Hideout, has launched an open-source tool called CSP Bypass. This tool is designed to assist ethical hackers and security researchers in i ... Read more

-
Cybersecurity News
Rockwell Automation Products Face Critical Security Risks, Urgent Patching Required
Two recently discovered vulnerabilities in Rockwell Automation’s FactoryTalk software products pose a serious threat to industrial control systems (ICS). The vulnerabilities, tracked as CVE-2024-45823 ... Read more

-
Cybersecurity News
CVE-2024-28991 (CVSS 9.0): SolarWinds Access Rights Manager RCE Flaw
In a recent security advisory, SolarWinds has disclosed two vulnerabilities affecting their Access Rights Manager (ARM) software. ARM is widely used by IT and security administrators to manage and aud ... Read more

-
Cybersecurity News
Critical Kibana Flaws (CVE-2024-37288, CVE-2024-37285) Expose Systems to Arbitrary Code Execution
Elastic, the company behind the popular open-source data visualization and analytics platform Kibana, has issued a critical security advisory urging users to update immediately to version 8.15.1. Two ... Read more
The following table lists the changes that have been made to the
CVE-2024-37285 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Oct. 01, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H Added CPE Configuration OR *cpe:2.3:a:elastic:kibana:*:*:*:*:*:*:*:* versions from (including) 8.10.0 up to (including) 8.15.0 Added Reference Type Elastic: https://discuss.elastic.co/t/kibana-8-15-1-security-update-esa-2024-27-esa-2024-28/366119 Types: Patch, Vendor Advisory -
CVE Received by [email protected]
Nov. 14, 2024
Action Type Old Value New Value Added Description A deserialization issue in Kibana can lead to arbitrary code execution when Kibana attempts to parse a YAML document containing a crafted payload. A successful attack requires a malicious user to have a combination of both specific Elasticsearch indices privileges https://www.elastic.co/guide/en/elasticsearch/reference/current/defining-roles.html#roles-indices-priv and Kibana privileges https://www.elastic.co/guide/en/fleet/current/fleet-roles-and-privileges.html assigned to them. The following Elasticsearch indices permissions are required * write privilege on the system indices .kibana_ingest* * The allow_restricted_indices flag is set to true Any of the following Kibana privileges are additionally required * Under Fleet the All privilege is granted * Under Integration the Read or All privilege is granted * Access to the fleet-setup privilege is gained through the Fleet Server’s service account token Added Reference Elastic https://discuss.elastic.co/t/kibana-8-15-1-security-update-esa-2024-27-esa-2024-28/366119 [No types assigned] Added CWE Elastic CWE-502 Added CVSS V3.1 Elastic AV:N/AC:L/PR:H/UI:N/S:C/C:H/I:H/A:H