CVE-2024-38100
Windows File Explorer Elevation of Privilege Vulnerability
Description
Windows File Explorer Elevation of Privilege Vulnerability
INFO
Published Date :
July 9, 2024, 5:15 p.m.
Last Modified :
Nov. 21, 2024, 9:24 a.m.
Remotely Exploit :
No
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-38100
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Apply the latest security updates.
- Reboot the system if prompted.
Public PoC/Exploit Available at Github
CVE-2024-38100 has a 4 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-38100.
| URL | Resource |
|---|---|
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38100 | Patch Vendor Advisory |
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38100 | Patch Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-38100 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-38100
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
A set of programs for analyzing common vulnerabilities in COM
C# C++
CVE-2024-38100 Windows Leaked Wallpaper Escelation to RCE vulnerability
Python
Leak of any user's NetNTLM hash. Fixed in KB5040434
C++
Collection of Windows Privilege Escalation (Analyse/PoC/Exploit)
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-38100 vulnerability anywhere in the article.

-
Kaspersky
Exploits and vulnerabilities in Q4 2024
Q4 2024 saw fewer published exploits for Windows and Linux compared to the first three quarters. Although the number of registered vulnerabilities continued to rise, the total number of Proof of Conce ... Read more

-
Cybersecurity News
CVE-2024-7261 (CVSS 9.8): Zyxel Patches Critical Vulnerability in Wi-Fi Devices
Zyxel, a prominent networking equipment manufacturer, has issued a security advisory urging users to promptly update their firmware to address a critical vulnerability affecting a range of their acces ... Read more

-
Cybersecurity News
PoC Exploit Released for Arbitrary File Write Flaw (CVE-2024-22263) in Spring Cloud Data Flow
Security researcher Zeyad Azima from SecureLayer7 published the proof-of-concept exploit for arbitrary file write vulnerability (CVE-2024-22263) in Spring Cloud Data Flow, a widely-used tool for cloud ... Read more

-
Cybersecurity News
CVE-2024-31214 & CVE-2024-24809: Traccar Users Urged to Update Immediately
Image: Horizon3Please enable JavaScriptTwo critical vulnerabilities have been discovered in the popular GPS tracking system Traccar, which is used for both personal and corporate applications. The vul ... Read more

-
Cybersecurity News
PoC Exploit Released for RCE 0-day CVE-2024-41992 in Arcadyan FMIMG51AX000J Model
A critical vulnerability, identified as CVE-2024-41992, has been discovered in the Arcadyan FMIMG51AX000J model, and potentially other WiFi Alliance-affiliated devices using the same firmware version ... Read more
-
Cybersecurity News
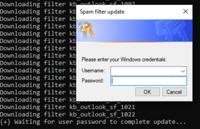
Cybercriminals Evolve Social Engineering Tactics, Exploit CVE-2022-26923 in Sophisticated Campaign
Credential harvester prompt spawned by `AntiSpam.exe | Image: Rapid7 Recently, cybersecurity firm Rapid7 identified a series of sophisticated intrusion attempts linked to an ongoing social engineering ... Read more

-
Cybersecurity News
CVE-2024-5290: Wi-Fi Flaw Leaves Millions Vulnerable to Root Takeover
Security researchers have uncovered a critical vulnerability in wpa_supplicant, a ubiquitous software component responsible for managing Wi-Fi connections on countless devices. The flaw, dubbed CVE-20 ... Read more

-
Cybersecurity News
Cisco Warns of Public PoC Exploit Code of Critical CVE-2024-20419 (CVSS 10) Flaw
Cisco has recently updated its security advisory, alerting users to a critical vulnerability identified as CVE-2024-20419. This flaw affects the Cisco Smart Software Manager On-Prem (Cisco SSM On-Prem ... Read more

-
Cybersecurity News
Apache CloudStack Releases Critical Patches (CVE-2024-42062 and CVE-2024-42222)
The Apache CloudStack project has issued an urgent security advisory, urging users to update their software immediately to address two critical vulnerabilities, CVE-2024-42062 and CVE-2024-42222. Thes ... Read more

-
tripwire.com
Tripwire Patch Priority Index for July 2024
Tripwire's July 2024 Patch Priority Index (PPI) brings together important vulnerabilities for Microsoft.First on the list are patches for Microsoft Office and Outlook that resolve remote code executio ... Read more

-
Cyber Security News
Leaked Wallpaper Exploit Let Attackers Escalate Privilege on Windows Systems
A critical security flaw in Windows’ wallpaper handling mechanism has been uncovered. It allows attackers to gain system-level privileges on affected machines. Security researcher Andrea Pierini discl ... Read more
The following table lists the changes that have been made to the
CVE-2024-38100 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38100 -
Initial Analysis by [email protected]
Jul. 11, 2024
Action Type Old Value New Value Changed Reference Type https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38100 No Types Assigned https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38100 Patch, Vendor Advisory Added CWE NIST NVD-CWE-Other Added CPE Configuration OR *cpe:2.3:o:microsoft:windows_server_2016:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.14393.7159 *cpe:2.3:o:microsoft:windows_server_2019:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.6054 *cpe:2.3:o:microsoft:windows_server_2022:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.20348.2582 *cpe:2.3:o:microsoft:windows_server_2022_23h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.25398.1009 -
CVE Received by [email protected]
Jul. 09, 2024
Action Type Old Value New Value Added Description Windows File Explorer Elevation of Privilege Vulnerability Added Reference Microsoft Corporation https://msrc.microsoft.com/update-guide/vulnerability/CVE-2024-38100 [No types assigned] Added CWE Microsoft Corporation CWE-284 Added CVSS V3.1 Microsoft Corporation AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H