CVE-2024-43399
Mobile Security Framework (MobSF) has a Zip Slip Vulnerability in .a Static Library Files
Description
Mobile Security Framework (MobSF) is a pen-testing, malware analysis and security assessment framework capable of performing static and dynamic analysis. Before 4.0.7, there is a flaw in the Static Libraries analysis section. Specifically, during the extraction of .a extension files, the measure intended to prevent Zip Slip attacks is improperly implemented. Since the implemented measure can be bypassed, the vulnerability allows an attacker to extract files to any desired location within the server running MobSF. This vulnerability is fixed in 4.0.7.
INFO
Published Date :
Aug. 19, 2024, 3:15 p.m.
Last Modified :
Aug. 20, 2024, 4:21 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Public PoC/Exploit Available at Github
CVE-2024-43399 has a 1 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-43399.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-43399 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-43399
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Ostorlab KEV: One-command to detect most remotely known exploitable vulnerabilities. Sourced from CISA KEV, Google's Tsunami, Ostorlab's Asteroid and Bug Bounty programs.
cisa-kev vulnerability 0day cisa exploits
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-43399 vulnerability anywhere in the article.

-
Cybersecurity News
Passive Backdoors, Active Threat: UNC1860’s Espionage Tools Exposed
Mandiant has uncovered alarming evidence of a sophisticated Iranian state-sponsored cyber campaign orchestrated by UNC1860, a threat actor likely affiliated with Iran’s Ministry of Intelligence and Se ... Read more
-
Cybersecurity News
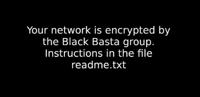
ZeroLogon to NoPac Vulnerability: Black Basta Group’s Exploit Arsenal Revealed
Desktop background on victim’s system after encryption | Image: QualysQualys has released a comprehensive report shedding light on the Black Basta ransomware, a highly disruptive threat that has wreak ... Read more

-
Cybersecurity News
Cisco Issues Security Advisories: Critical Vulnerabilities Impact Multiple Products
Cisco Systems has released a series of urgent security advisories, revealing a total of nine vulnerabilities affecting various products, including Cisco IOS XR Software, Crosswork Network Services Orc ... Read more

-
Cybersecurity News
CVE-2024-7988 (CVSS 9.8): Rockwell Automation’s ThinManager Flaw Allows RCE
Rockwell Automation has issued a critical security advisory concerning multiple vulnerabilities discovered in its ThinManager ThinServer software. These vulnerabilities, reported by Nicholas Zubrisky ... Read more

-
Cybersecurity News
CVE-2024-43399: Critical Zip Slip Vulnerability Discovered in Mobile Security Framework (MobSF)
A serious security flaw has been uncovered in Mobile Security Framework (MobSF), a widely-used open-source tool for mobile app security analysis. The vulnerability, identified as CVE-2024-43399 (CVSS ... Read more

-
Cybersecurity News
Styx Stealer: The Evolved Threat to Your Crypto and Data
Recently, Check Point Research (CPR) discovered a new malware variant, Styx Stealer. Derived from the notorious Phemedrone Stealer, Styx was being sold via subscription with advanced capabilities such ... Read more
The following table lists the changes that have been made to the
CVE-2024-43399 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Aug. 20, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://github.com/MobSF/Mobile-Security-Framework-MobSF/commit/cc625fe8430f3437a473e82aa2966d100a4dc883 No Types Assigned https://github.com/MobSF/Mobile-Security-Framework-MobSF/commit/cc625fe8430f3437a473e82aa2966d100a4dc883 Patch Changed Reference Type https://github.com/MobSF/Mobile-Security-Framework-MobSF/security/advisories/GHSA-4hh3-vj32-gr6j No Types Assigned https://github.com/MobSF/Mobile-Security-Framework-MobSF/security/advisories/GHSA-4hh3-vj32-gr6j Exploit, Vendor Advisory Added CWE NIST CWE-22 Added CPE Configuration OR *cpe:2.3:a:opensecurity:mobile_security_framework:*:*:*:*:*:*:*:* versions up to (excluding) 4.0.7 -
CVE Received by [email protected]
Aug. 19, 2024
Action Type Old Value New Value Added Description Mobile Security Framework (MobSF) is a pen-testing, malware analysis and security assessment framework capable of performing static and dynamic analysis. Before 4.0.7, there is a flaw in the Static Libraries analysis section. Specifically, during the extraction of .a extension files, the measure intended to prevent Zip Slip attacks is improperly implemented. Since the implemented measure can be bypassed, the vulnerability allows an attacker to extract files to any desired location within the server running MobSF. This vulnerability is fixed in 4.0.7. Added Reference GitHub, Inc. https://github.com/MobSF/Mobile-Security-Framework-MobSF/security/advisories/GHSA-4hh3-vj32-gr6j [No types assigned] Added Reference GitHub, Inc. https://github.com/MobSF/Mobile-Security-Framework-MobSF/commit/cc625fe8430f3437a473e82aa2966d100a4dc883 [No types assigned] Added CWE GitHub, Inc. CWE-23 Added CVSS V3.1 GitHub, Inc. AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H