CVE-2024-45519
Synacor Zimbra Collaboration Suite (ZCS) Command Execution Vulnerability - [Actively Exploited]
Description
The postjournal service in Zimbra Collaboration (ZCS) before 8.8.15 Patch 46, 9 before 9.0.0 Patch 41, 10 before 10.0.9, and 10.1 before 10.1.1 sometimes allows unauthenticated users to execute commands.
INFO
Published Date :
Oct. 2, 2024, 10:15 p.m.
Last Modified :
Nov. 4, 2025, 4:45 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Synacor Zimbra Collaboration Suite (ZCS) contains an unspecified vulnerability in the postjournal service that may allow an unauthenticated user to execute commands.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Unknown
https://wiki.zimbra.com/wiki/Zimbra_Security_Advisories ; https://nvd.nist.gov/vuln/detail/CVE-2024-45519
Affected Products
The following products are affected by CVE-2024-45519
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Upgrade to version 8.8.15 Patch 46, 9.0.0 Patch 41, 10.0.9, 10.1.1 or later.
Public PoC/Exploit Available at Github
CVE-2024-45519 has a 34 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-45519.
| URL | Resource |
|---|---|
| https://wiki.zimbra.com/wiki/Security_Center | Release Notes |
| https://wiki.zimbra.com/wiki/Zimbra_Releases/10.0.9#Security_Fixes | Release Notes |
| https://wiki.zimbra.com/wiki/Zimbra_Releases/10.1.1#Security_Fixes | Release Notes |
| https://wiki.zimbra.com/wiki/Zimbra_Releases/8.8.15/P46#Security_Fixes | Release Notes |
| https://wiki.zimbra.com/wiki/Zimbra_Releases/9.0.0/P41#Security_Fixes | Release Notes |
| https://wiki.zimbra.com/wiki/Zimbra_Responsible_Disclosure_Policy | Not Applicable |
| https://blog.projectdiscovery.io/zimbra-remote-code-execution/ | Exploit |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-45519 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-45519 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-45519
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Exploit Intelligence Platform MCP Server
cve database exploit mcp-server vulnerability
Makefile Python Dockerfile Shell
Exploit Intelligence Platform MCP Server
Shell Python Makefile Dockerfile
Automated GitHub traffic stats archival (views, clones, referrers, paths)
Python
Exploit Intelligence Platform MCP Server
cve database exploit vulnerability mcp-server
Makefile Python Dockerfile Shell
CVE detection-to-remediation fabric app. Scan, enrich, triage, and fix vulnerabilities across managed repos.
cve fabric github-actions mcp security vulnerability-management
JavaScript TypeScript
Exploit Intel MCP Server
Python Makefile
None
All PoC
PowerShell Python Java Shell C Makefile PHP Lua Roff Ruby
Laboratory of vulnerable machines and systems
Dockerfile Shell PHP CSS JavaScript HTML SCSS Handlebars Blade Python
备份的漏洞库,3月开始我们来维护
None
None
None
HTML
wy876
Python
Zimbra CVE-2024-45519
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-45519 vulnerability anywhere in the article.

-
Daily CyberSecurity
Triple Threat Patched: Zimbra 10.1.16 Fixes XSS, XXE & LDAP Injection
Zimbra has rolled out a significant security update for its collaboration suite, releasing Zimbra 10.1.16 to address a spectrum of vulnerabilities ranging from front-end script injection to back-end d ... Read more

-
Daily CyberSecurity
Zimbra Under Siege: High-Severity LFI Vulnerability Exposes Internal Files to Unauthenticated Attackers
Administrators of the popular Zimbra Collaboration Suite (ZCS) are being urged to patch immediately after the discovery of two distinct security vulnerabilities. The most severe of the pair allows una ... Read more

-
Daily CyberSecurity
CVE-2025-11833 (CVSS 9.8): Critical Flaw Exposes 400,000 WordPress Sites to Unauthenticated Account Takeover
The Post SMTP plugin, used by over 400,000 WordPress sites to ensure reliable email delivery, has been found to contain a critical Missing Authorization vulnerability that can lead to complete Account ... Read more

-
Daily CyberSecurity
Zimbra Issues Emergency Patch for Critical SSRF Vulnerability in Chat Proxy Configuration
Zimbra has released an emergency security patch (version 10.1.12) to address a critical Server-Side Request Forgery (SSRF) vulnerability in its chat proxy configuration, urging all administrators to u ... Read more

-
Daily CyberSecurity
Zimbra XSS Zero-Day (CVE-2025-27915) Actively Exploited; CISA Adds to KEV Catalog
A cross-site scripting (XSS) vulnerability in Synacor Zimbra Collaboration Suite (ZCS) — tracked as CVE-2025-27915 — has been confirmed to be actively exploited in the wild, prompting CISA to add the ... Read more

-
Daily CyberSecurity
400,000 WordPress Sites at Risk: CVE-2025-24000 in Post SMTP Plugin Allows Full Site Takeover
A vulnerability in the popular Post SMTP WordPress plugin—installed on over 400,000 websites—has been disclosed by Patchstack, exposing sites to full account takeover attacks via broken access control ... Read more

-
Cybersecurity News
CISA Flags Actively Exploited Zimbra (CVE-2023-34192) and Microsoft (CVE-2024-49035) Vulnerabilities
The Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning, adding two critical vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog. This move underscores the ur ... Read more

-
Kaspersky
Exploits and vulnerabilities in Q3 2024
Q3 2024 saw multiple vulnerabilities discovered in Windows and Linux subsystems that are not standard for cyberattacks. This is because operating system developers have been releasing new security mit ... Read more

-
Cybersecurity News
Century Systems Routers Vulnerable to Remote Exploitation – CVE-2024-50357 (CVSS 9.8)
Century Systems Co., Ltd. has issued a critical security advisory regarding its FutureNet NXR series routers. A vulnerability, tracked as CVE-2024-50357 and assigned a CVSS score of 9.8 (indicating a ... Read more

-
TheCyberThrone
The CyberThrone Most Exploited Vulnerabilities Top 10 – October 2024
Welcome to TheCyberThrone most exploited vulnerabilities review. This review is for the month of October 2024CVE-2024-21762: Fortinet FortiOS: Out-of-bounds WriteCVSS 3.1 score : 9.8 CISA KEV : Y ... Read more

-
Cybersecurity News
PSAUX Ransomware is Exploiting Two Max Severity Flaws (CVE-2024-51567, CVE-2024-51568) in CyberPanel
Image: DreyAndThree critical remote code execution (RCE) vulnerabilities impacting CyberPanel, a widely used web hosting control panel, are under active exploitation. Threat actors are leveraging thes ... Read more

-
Cybersecurity News
ThreatFabric Reveals Dangerous Upgrades in LightSpy Spyware – 28 Plugins Targeting iOS Devices
Image: ThreatFabricThreatFabric released a report detailing advancements in the LightSpy implant, an iOS spyware first identified in 2020, which has evolved into a more complex and damaging tool. The ... Read more

-
Cybersecurity News
AWS CDK Vulnerability: Missing S3 Bucket Could Lead to Account Takeover
Security researchers Ofek Itach and Yakir Kadkoda from Aqua Security’s Team Nautilus uncovered a critical vulnerability in the AWS Cloud Development Kit (CDK) that could lead to a full account takeove ... Read more

-
Cybersecurity News
Critical EoP Flaw in Microsoft’s Remote Registry: Researcher Publishes PoC for CVE-2024-43532
Akamai researcher Stiv Kupchik published the technical details and a proof-of-concept (PoC) exploit code for a critical Elevation of Privilege (EoP) vulnerability, CVE-2024-43532, in Microsoft’s Remot ... Read more

-
Cybersecurity News
Patch Now! Grafana Hit by 9.9 Severity RCE Vulnerability (CVE-2024-9264)
A critical security vulnerability (CVE-2024-9264) has been discovered in Grafana, the popular open-source platform for monitoring and observability. This vulnerability, with a CVSS v3.1 score of 9.9, ... Read more

-
Cybersecurity News
Broadcom Warns of High-Risk VMware HCX Vulnerability (CVE-2024-38814)
In a recent security advisory, Broadcom disclosed a significant SQL injection vulnerability (CVE-2024-38814) affecting VMware HCX, a key component used in multi-cloud infrastructures to enable applica ... Read more

-
Cybersecurity News
Rittal IoT Interface and CMC III Processing Unit Plagued by Critical Security Flaws
Rittal, a leading provider of industrial automation solutions, has addressed multiple vulnerabilities in their IoT Interface and CMC III Processing Unit. Discovered by Johannes Kruchem of SEC Consult ... Read more

-
security.nl
'Nederland telt ruim tweehonderd Zimbra-mailservers met kritiek beveiligingslek'
Ruim tweehonderd Zimbra-mailservers in Nederland missen een beveiligingsupdate voor een op grote schaal aangevallen kritieke kwetsbaarheid, zo meldt The Shadowserver Foundation op basis van eigen onde ... Read more
-
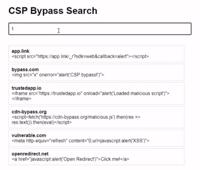
Cybersecurity News
CSP Bypass: A New Open-Source Tool for Ethical Hackers to Overcome Content Security Policies
Renowned security researcher Renniepak, the founder of Hacker Hideout, has launched an open-source tool called CSP Bypass. This tool is designed to assist ethical hackers and security researchers in i ... Read more

-
Cybersecurity News
Active Exploits Target Zimbra Collaboration: Over 19K Systems Vulnerable to CVE-2024-45519
Image: The Shadowserver FoundationEnterprise security firm Proofpoint has issued a critical warning regarding active exploitation attempts against Synacor’s Zimbra Collaboration platform. A recently d ... Read more
The following table lists the changes that have been made to the
CVE-2024-45519 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Nov. 04, 2025
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p1:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:-:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:*:*:*:*:*:*:*:* versions up to (excluding) 8.8.15 *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p6:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p5:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p3:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p10:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p2:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p4:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p7:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p8:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p9:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:-:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p1:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p10:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p11:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p12:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p2:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p13:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p14:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p15:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p16:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p17:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p18:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p19:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p20:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p21:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p22:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p23:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p24:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p24.1:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p25:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p26:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p3:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p4:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p5:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p6:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p7:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p8:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p9:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:*:*:*:*:*:*:*:* versions from (including) 10.0.0 up to (excluding) 10.0.9 *cpe:2.3:a:synacor:zimbra_collaboration_suite:10.1.0:*:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p11:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p12:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p13:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p14:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p15:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p16:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p17:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p18:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p19:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p20:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p21:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p22:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p23:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p24:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p25:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p26:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p27:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p28:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p29:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p30:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p31:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p31.1:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p32:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p33:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p34:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p35:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p36:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p37:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p38:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p39:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p40:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p41:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p42:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p43:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p27:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p28:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p29:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p30:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p31:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p32:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p33:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p34:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p35:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p36:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p37:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p38:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p39:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:9.0.0:p40:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p44:*:*:*:*:*:* *cpe:2.3:a:synacor:zimbra_collaboration_suite:8.8.15:p45:*:*:*:*:*:* Removed CPE Configuration OR *cpe:2.3:a:zimbra:collaboration:9.0.0:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions up to (excluding) 8.8.15 *cpe:2.3:a:zimbra:collaboration:8.8.15:p17:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p18:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p22:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p28:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p29:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p30:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p31:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p32:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p0:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p41:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p42:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p36:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p38:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p39:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:10.1.0:*:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions from (including) 10.0.0 up to (excluding) 10.0.9 *cpe:2.3:a:zimbra:collaboration:9.0.0:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p45:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p44:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p43:*:*:*:*:*:* Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-45519 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-45519 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-45519 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-45519 -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Feb. 25, 2025
Action Type Old Value New Value Changed Vulnerability Name Synacor Zimbra Collaboration Command Execution Vulnerability Synacor Zimbra Collaboration Suite (ZCS) Command Execution Vulnerability -
Modified Analysis by [email protected]
Dec. 20, 2024
Action Type Old Value New Value Added CWE NIST NVD-CWE-noinfo Removed CWE NIST NVD-CWE-Other Changed Reference Type https://blog.projectdiscovery.io/zimbra-remote-code-execution/ No Types Assigned https://blog.projectdiscovery.io/zimbra-remote-code-execution/ Exploit Changed Reference Type https://wiki.zimbra.com/wiki/Zimbra_Responsible_Disclosure_Policy Product https://wiki.zimbra.com/wiki/Zimbra_Responsible_Disclosure_Policy Not Applicable -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Nov. 21, 2024
Action Type Old Value New Value Added CWE CWE-78 Removed CWE CWE-284 Added Reference https://blog.projectdiscovery.io/zimbra-remote-code-execution/ -
Modified Analysis by [email protected]
Oct. 23, 2024
Action Type Old Value New Value Changed Reference Type https://wiki.zimbra.com/wiki/Zimbra_Releases/10.0.9#Security_Fixes No Types Assigned https://wiki.zimbra.com/wiki/Zimbra_Releases/10.0.9#Security_Fixes Release Notes Changed Reference Type https://wiki.zimbra.com/wiki/Zimbra_Releases/10.1.1#Security_Fixes No Types Assigned https://wiki.zimbra.com/wiki/Zimbra_Releases/10.1.1#Security_Fixes Release Notes Changed Reference Type https://wiki.zimbra.com/wiki/Zimbra_Releases/8.8.15/P46#Security_Fixes No Types Assigned https://wiki.zimbra.com/wiki/Zimbra_Releases/8.8.15/P46#Security_Fixes Release Notes Changed Reference Type https://wiki.zimbra.com/wiki/Zimbra_Releases/9.0.0/P41#Security_Fixes No Types Assigned https://wiki.zimbra.com/wiki/Zimbra_Releases/9.0.0/P41#Security_Fixes Release Notes Removed CWE NIST CWE-863 Added CWE NIST NVD-CWE-Other -
CVE Modified by [email protected]
Oct. 22, 2024
Action Type Old Value New Value Added Reference MITRE https://wiki.zimbra.com/wiki/Zimbra_Releases/10.1.1#Security_Fixes [No types assigned] Added Reference MITRE https://wiki.zimbra.com/wiki/Zimbra_Releases/10.0.9#Security_Fixes [No types assigned] Added Reference MITRE https://wiki.zimbra.com/wiki/Zimbra_Releases/9.0.0/P41#Security_Fixes [No types assigned] Added Reference MITRE https://wiki.zimbra.com/wiki/Zimbra_Releases/8.8.15/P46#Security_Fixes [No types assigned] -
Modified Analysis by [email protected]
Oct. 15, 2024
Action Type Old Value New Value Changed Reference Type https://wiki.zimbra.com/wiki/Security_Center Release Notes, Vendor Advisory https://wiki.zimbra.com/wiki/Security_Center Release Notes Changed CPE Configuration OR *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions up to (excluding) 8.8.15 *cpe:2.3:a:zimbra:collaboration:8.8.15:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p17:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p18:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p22:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p28:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p29:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p30:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p31:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p32:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p41:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p42:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p43:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p44:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p45:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p0:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p36:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p38:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p39:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions from (including) 10.0.0 up to (excluding) 10.0.9 OR *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions up to (excluding) 8.8.15 *cpe:2.3:a:zimbra:collaboration:8.8.15:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p17:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p18:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p22:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p28:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p29:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p30:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p31:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p32:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p41:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p42:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p43:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p44:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p45:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p0:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p36:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p38:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p39:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions from (including) 10.0.0 up to (excluding) 10.0.9 *cpe:2.3:a:zimbra:collaboration:10.1.0:*:*:*:*:*:*:* -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 11, 2024
Action Type Old Value New Value Added CWE CISA-ADP CWE-284 Removed CWE CISA-ADP CWE-78 -
Modified Analysis by [email protected]
Oct. 10, 2024
Action Type Old Value New Value Changed CPE Configuration OR *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions up to (excluding) 8.8.15 *cpe:2.3:a:zimbra:collaboration:8.8.15:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p17:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p18:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p22:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p28:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p29:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p30:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p31:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p32:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p41:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p42:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p43:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p44:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p45:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p0:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p36:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p38:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p39:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions from (including) 10.0.0 up to (excluding) 10.0.9 *cpe:2.3:a:zimbra:collaboration:10.1.0:*:*:*:*:*:*:* OR *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions up to (excluding) 8.8.15 *cpe:2.3:a:zimbra:collaboration:8.8.15:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p17:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p18:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p22:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p28:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p29:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p30:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p31:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p32:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p41:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p42:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p43:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p44:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p45:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p0:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p36:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p38:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p39:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions from (including) 10.0.0 up to (excluding) 10.0.9 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 09, 2024
Action Type Old Value New Value Added CWE CISA-ADP CWE-78 Removed CWE CISA-ADP CWE-284 -
Modified Analysis by [email protected]
Oct. 04, 2024
Action Type Old Value New Value -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Oct. 04, 2024
Action Type Old Value New Value Added Due Date 2024-10-24 Added Vulnerability Name Synacor Zimbra Collaboration Command Execution Vulnerability Added Required Action Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. Added Date Added 2024-10-03 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 03, 2024
Action Type Old Value New Value Added CWE CISA-ADP CWE-284 -
Initial Analysis by [email protected]
Oct. 03, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://wiki.zimbra.com/wiki/Security_Center No Types Assigned https://wiki.zimbra.com/wiki/Security_Center Release Notes, Vendor Advisory Changed Reference Type https://wiki.zimbra.com/wiki/Zimbra_Responsible_Disclosure_Policy No Types Assigned https://wiki.zimbra.com/wiki/Zimbra_Responsible_Disclosure_Policy Product Added CWE NIST CWE-863 Added CPE Configuration OR *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions up to (excluding) 8.8.15 *cpe:2.3:a:zimbra:collaboration:8.8.15:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p17:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p18:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p22:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p28:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p29:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p30:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p31:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p32:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p41:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p42:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p43:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p44:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p45:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:8.8.15:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:-:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p0:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p10:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p11:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p12:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p13:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p14:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p15:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p16:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p19:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p2:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p20:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p21:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p23:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p24.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p25:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p26:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p27:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p3:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p33:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p34:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p35:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p36:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p37:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p38:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p39:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p4:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p40:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p5:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p6:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p7.1:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p8:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:9.0.0:p9:*:*:*:*:*:* *cpe:2.3:a:zimbra:collaboration:*:*:*:*:*:*:*:* versions from (including) 10.0.0 up to (excluding) 10.0.9 *cpe:2.3:a:zimbra:collaboration:10.1.0:*:*:*:*:*:*:* -
CVE Received by [email protected]
Oct. 02, 2024
Action Type Old Value New Value Added Description The postjournal service in Zimbra Collaboration (ZCS) before 8.8.15 Patch 46, 9 before 9.0.0 Patch 41, 10 before 10.0.9, and 10.1 before 10.1.1 sometimes allows unauthenticated users to execute commands. Added Reference MITRE https://wiki.zimbra.com/wiki/Security_Center [No types assigned] Added Reference MITRE https://wiki.zimbra.com/wiki/Zimbra_Responsible_Disclosure_Policy [No types assigned] Added CVSS V3.1 MITRE AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H