CVE-2024-45823
FactoryTalk® Batch View™ Authentication Bypass Vulnerability via shared secrets
Description
CVE-2024-45823 IMPACT An authentication bypass vulnerability exists in the affected product. The vulnerability exists due to shared secrets across accounts and could allow a threat actor to impersonate a user if the threat actor is able to enumerate additional information required during authentication.
INFO
Published Date :
Sept. 12, 2024, 3:18 p.m.
Last Modified :
Oct. 2, 2024, 2:49 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-45823
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 4.0 | CRITICAL | [email protected] |
Solution
- Upgrade to Rockwell FactoryTalk Batch View version 3.00 or later.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-45823.
| URL | Resource |
|---|---|
| https://www.rockwellautomation.com/en-us/trust-center/security-advisories/advisory.SD%201698.html | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-45823 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-45823
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-45823 vulnerability anywhere in the article.

-
Cybersecurity News
Privilege Escalation and Remote Code Execution Threaten Cisco Routers: No Updates Available
In a recent security advisory, Cisco revealed multiple vulnerabilities impacting its Small Business RV340, RV340W, RV345, and RV345P Dual WAN Gigabit VPN Routers, which could potentially expose busine ... Read more

-
Cybersecurity News
CVE-2024-43917 (CVSS 9.3): Unpatched SQLi Flaw in TI WooCommerce Wishlist Threatens 100,000+ Sites
A critical security vulnerability has been discovered in the widely-used WordPress plugin, TI WooCommerce Wishlist, potentially exposing over 100,000 websites to malicious attacks. The flaw, tracked a ... Read more

-
Cybersecurity News
Proxmox Virtual Environment and Mail Gateway Exposed to Critical API Vulnerability
A critical vulnerability has been identified in Proxmox Virtual Environment (VE) and Proxmox Mail Gateway (PMG) that could allow unauthorized access to sensitive files and potentially lead to a full s ... Read more

-
Cybersecurity News
Passive Backdoors, Active Threat: UNC1860’s Espionage Tools Exposed
Mandiant has uncovered alarming evidence of a sophisticated Iranian state-sponsored cyber campaign orchestrated by UNC1860, a threat actor likely affiliated with Iran’s Ministry of Intelligence and Se ... Read more
-
Cybersecurity News
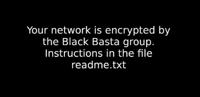
ZeroLogon to NoPac Vulnerability: Black Basta Group’s Exploit Arsenal Revealed
Desktop background on victim’s system after encryption | Image: QualysQualys has released a comprehensive report shedding light on the Black Basta ransomware, a highly disruptive threat that has wreak ... Read more

-
Cybersecurity News
Rockwell Automation Products Face Critical Security Risks, Urgent Patching Required
Two recently discovered vulnerabilities in Rockwell Automation’s FactoryTalk software products pose a serious threat to industrial control systems (ICS). The vulnerabilities, tracked as CVE-2024-45823 ... Read more
The following table lists the changes that have been made to the
CVE-2024-45823 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Oct. 02, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://www.rockwellautomation.com/en-us/trust-center/security-advisories/advisory.SD%201698.html No Types Assigned https://www.rockwellautomation.com/en-us/trust-center/security-advisories/advisory.SD%201698.html Vendor Advisory Added CWE NIST NVD-CWE-noinfo Added CPE Configuration OR *cpe:2.3:a:rockwellautomation:factorytalk_batch_view:2.01.00:*:*:*:*:*:*:* -
CVE Received by [email protected]
Sep. 12, 2024
Action Type Old Value New Value Added Description CVE-2024-45823 IMPACT An authentication bypass vulnerability exists in the affected product. The vulnerability exists due to shared secrets across accounts and could allow a threat actor to impersonate a user if the threat actor is able to enumerate additional information required during authentication. Added Reference Rockwell Automation https://www.rockwellautomation.com/en-us/trust-center/security-advisories/advisory.SD%201698.html [No types assigned] Added CWE Rockwell Automation CWE-287 Added CVSS V3.1 Rockwell Automation AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H Added CVSS V4.0 Rockwell Automation CVSS:4.0/AV:N/AC:H/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:X/R:X/V:X/RE:X/U:X