CVE-2024-46982
Cache Poisoning in next.js
Description
Next.js is a React framework for building full-stack web applications. By sending a crafted HTTP request, it is possible to poison the cache of a non-dynamic server-side rendered route in the pages router (this does not affect the app router). When this crafted request is sent it could coerce Next.js to cache a route that is meant to not be cached and send a `Cache-Control: s-maxage=1, stale-while-revalidate` header which some upstream CDNs may cache as well. To be potentially affected all of the following must apply: 1. Next.js between 13.5.1 and 14.2.9, 2. Using pages router, & 3. Using non-dynamic server-side rendered routes e.g. `pages/dashboard.tsx` not `pages/blog/[slug].tsx`. This vulnerability was resolved in Next.js v13.5.7, v14.2.10, and later. We recommend upgrading regardless of whether you can reproduce the issue or not. There are no official or recommended workarounds for this issue, we recommend that users patch to a safe version.
INFO
Published Date :
Sept. 17, 2024, 10:15 p.m.
Last Modified :
Sept. 10, 2025, 3:46 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Public PoC/Exploit Available at Github
CVE-2024-46982 has a 22 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-46982.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-46982 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-46982
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
how to check/ fix your nextjs version across multiple projects
Python
Dummy Next.js app pinned to vulnerable [email protected] (for testing only)
JavaScript
Security infrastructure your AI can't be — deterministic, daily CVE intel past your model's training cutoff, whole-repo-aware, author-independent. The security MCP for vibe coding: 438 rules, 37 tools, CLI + doctor for Next.js, Supabase, Clerk, Stripe, Prisma, Drizzle, Hono, AI SDK & MCP.
ai-security claude clerk cursor mcp nextjs owasp prisma sast security stripe supabase typescript vercel vibe-coding cve drizzle hono mcp-server prompt-injection
TypeScript JavaScript
Security auditor skill for Claude Code — React + TypeScript + Supabase + Vercel
None
JavaScript TypeScript CSS PLpgSQL Python HTML PowerShell Shell
None
Python TypeScript
None
Burp Suite extension for detecting PortSwigger Top 10 Web Hacking Techniques (2025) — 8 modules, 250+ CVE-backed payloads
Java
Modern JS process orchestration and deployment for your own infrastructure.
deployment error-monitoring monitoring node nodejs npm-package orchestration process-manager
JavaScript TypeScript Shell Dockerfile
None
TypeScript CSS JavaScript Python
None
Go
Cloudflare ACME Challenge WAF Bypass Scanner
Python
Reproduction of CVE-2024-46982
JavaScript TypeScript
High-performance security scanner for finding exposed credentials, secrets, and vulnerabilities in web applications
Makefile Rust
Comprehensive demonstration of CVE-2025-32421 Eclipse technique - a sophisticated race condition attack against Next.js 15.0.4 that bypasses the original CVE-2024-46982 patch.
JavaScript TypeScript
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-46982 vulnerability anywhere in the article.

-
Daily CyberSecurity
Operation PCPcat: 60,000 Next.js Servers Hijacked in Just 48 Hours
A highly automated and ruthlessly efficient cyber-espionage campaign is tearing through the cloud infrastructure of modern web applications, leaving tens of thousands of compromised servers in its wak ... Read more

-
Daily CyberSecurity
Maximum Severity Alert: Critical RCE Flaw Hits Next.js (CVE-2025-66478, CVSS 10.0)
Developers using the modern stack of Next.js and React are facing a “red alert” situation today. A maximum-severity security flaw has been uncovered in the React Server Components (RSC) protocol, putt ... Read more

-
Daily CyberSecurity
Next.js Flaw (CVE-2025-49826, CVSS 7.5): Cache Poisoning Leads to Denial-of-Service
A cache poisoning vulnerability (CVE-2025-49826) with a CVSS score of 7.5 has been disclosed in Next.js, the popular React-based web development framework. The flaw, found in versions >=15.1.0 <15.1.8 ... Read more

-
Daily CyberSecurity
CVE-2025-48947: Session Cookies at Risk in Auth0 Next.js SDK
A serious vulnerability has been uncovered in the widely-used Auth0 Next.js SDK—a library that helps developers implement authentication in their Next.js apps. Tracked as CVE-2025-48947 and rated CVSS ... Read more
-
Cybersecurity News
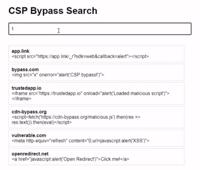
CSP Bypass: A New Open-Source Tool for Ethical Hackers to Overcome Content Security Policies
Renowned security researcher Renniepak, the founder of Hacker Hideout, has launched an open-source tool called CSP Bypass. This tool is designed to assist ethical hackers and security researchers in i ... Read more
-
Cybersecurity News
CVE-2024-8698: Keycloak Vulnerability Puts SAML Authentication at Risk
Image: KeycloakIn a concerning development for organizations relying on Keycloak for secure identity and access management, a high-severity vulnerability has been discovered in its SAML signature vali ... Read more
-
Cybersecurity News
Critical Security Flaws in Camaleon CMS Put Web Servers at Risk – Users Urged to Upgrade Immediately
In a significant development for website owners and administrators using Camaleon CMS, a critical security update has been released to address several vulnerabilities, some of which are already being ... Read more

-
Cybersecurity News
Next.js Vulnerability CVE-2024-46982: Cache Poisoning Exploit Threatens Deployments
In the fast-paced world of web development, security is a constant concern, especially for platforms that power high-traffic applications like Next.js. Recently, the Next.js team has disclosed a new v ... Read more
The following table lists the changes that have been made to the
CVE-2024-46982 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Sep. 10, 2025
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:a:vercel:next.js:*:*:*:*:*:node.js:*:* versions from (including) 13.5.1 up to (excluding) 13.5.7 *cpe:2.3:a:vercel:next.js:*:*:*:*:*:node.js:*:* versions from (including) 14.0.0 up to (excluding) 14.2.10 Added Reference Type GitHub, Inc.: https://github.com/vercel/next.js/commit/7ed7f125e07ef0517a331009ed7e32691ba403d3 Types: Patch Added Reference Type GitHub, Inc.: https://github.com/vercel/next.js/commit/bd164d53af259c05f1ab434004bcfdd3837d7cda Types: Patch Added Reference Type GitHub, Inc.: https://github.com/vercel/next.js/security/advisories/GHSA-gp8f-8m3g-qvj9 Types: Vendor Advisory -
CVE Received by [email protected]
Sep. 17, 2024
Action Type Old Value New Value Added Description Next.js is a React framework for building full-stack web applications. By sending a crafted HTTP request, it is possible to poison the cache of a non-dynamic server-side rendered route in the pages router (this does not affect the app router). When this crafted request is sent it could coerce Next.js to cache a route that is meant to not be cached and send a `Cache-Control: s-maxage=1, stale-while-revalidate` header which some upstream CDNs may cache as well. To be potentially affected all of the following must apply: 1. Next.js between 13.5.1 and 14.2.9, 2. Using pages router, & 3. Using non-dynamic server-side rendered routes e.g. `pages/dashboard.tsx` not `pages/blog/[slug].tsx`. This vulnerability was resolved in Next.js v13.5.7, v14.2.10, and later. We recommend upgrading regardless of whether you can reproduce the issue or not. There are no official or recommended workarounds for this issue, we recommend that users patch to a safe version. Added Reference GitHub, Inc. https://github.com/vercel/next.js/security/advisories/GHSA-gp8f-8m3g-qvj9 [No types assigned] Added Reference GitHub, Inc. https://github.com/vercel/next.js/commit/7ed7f125e07ef0517a331009ed7e32691ba403d3 [No types assigned] Added Reference GitHub, Inc. https://github.com/vercel/next.js/commit/bd164d53af259c05f1ab434004bcfdd3837d7cda [No types assigned] Added CWE GitHub, Inc. CWE-639 Added CVSS V3.1 GitHub, Inc. AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H