CVE-2024-46986
Arbitrary file write leading to RCE in Camaleon CMS
Description
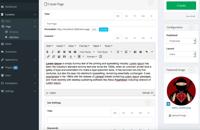
Camaleon CMS is a dynamic and advanced content management system based on Ruby on Rails. An arbitrary file write vulnerability accessible via the upload method of the MediaController allows authenticated users to write arbitrary files to any location on the web server Camaleon CMS is running on (depending on the permissions of the underlying filesystem). E.g. This can lead to a delayed remote code execution in case an attacker is able to write a Ruby file into the config/initializers/ subfolder of the Ruby on Rails application. This issue has been addressed in release version 2.8.2. Users are advised to upgrade. There are no known workarounds for this vulnerability.
INFO
Published Date :
Sept. 18, 2024, 6:15 p.m.
Last Modified :
April 17, 2025, 6:15 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Public PoC/Exploit Available at Github
CVE-2024-46986 has a 1 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-46986.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-46986 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-46986
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-46986 vulnerability anywhere in the article.
-
Cybersecurity News
Critical Security Flaws in Camaleon CMS Put Web Servers at Risk – Users Urged to Upgrade Immediately
In a significant development for website owners and administrators using Camaleon CMS, a critical security update has been released to address several vulnerabilities, some of which are already being ... Read more
The following table lists the changes that have been made to the
CVE-2024-46986 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by [email protected]
Apr. 17, 2025
Action Type Old Value New Value Added Reference https://securitylab.github.com/advisories/GHSL-2024-182_GHSL-2024-186_Camaleon_CMS -
Initial Analysis by [email protected]
Sep. 24, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H Changed Reference Type https://codeql.github.com/codeql-query-help/ruby/rb-path-injection No Types Assigned https://codeql.github.com/codeql-query-help/ruby/rb-path-injection Third Party Advisory Changed Reference Type https://github.com/owen2345/camaleon-cms/security/advisories/GHSA-wmjg-vqhv-q5p5 No Types Assigned https://github.com/owen2345/camaleon-cms/security/advisories/GHSA-wmjg-vqhv-q5p5 Exploit, Third Party Advisory Changed Reference Type https://owasp.org/www-community/attacks/Path_Traversal No Types Assigned https://owasp.org/www-community/attacks/Path_Traversal Issue Tracking Changed Reference Type https://www.reddit.com/r/rails/comments/1exwtdm/camaleon_cms_281_has_been_released No Types Assigned https://www.reddit.com/r/rails/comments/1exwtdm/camaleon_cms_281_has_been_released Patch Added CWE NIST CWE-22 Added CPE Configuration OR *cpe:2.3:a:tuzitio:camaleon_cms:*:*:*:*:*:*:*:* versions up to (excluding) 2.8.2 -
CVE Received by [email protected]
Sep. 18, 2024
Action Type Old Value New Value Added Description Camaleon CMS is a dynamic and advanced content management system based on Ruby on Rails. An arbitrary file write vulnerability accessible via the upload method of the MediaController allows authenticated users to write arbitrary files to any location on the web server Camaleon CMS is running on (depending on the permissions of the underlying filesystem). E.g. This can lead to a delayed remote code execution in case an attacker is able to write a Ruby file into the config/initializers/ subfolder of the Ruby on Rails application. This issue has been addressed in release version 2.8.2. Users are advised to upgrade. There are no known workarounds for this vulnerability. Added Reference GitHub, Inc. https://github.com/owen2345/camaleon-cms/security/advisories/GHSA-wmjg-vqhv-q5p5 [No types assigned] Added Reference GitHub, Inc. https://codeql.github.com/codeql-query-help/ruby/rb-path-injection [No types assigned] Added Reference GitHub, Inc. https://owasp.org/www-community/attacks/Path_Traversal [No types assigned] Added Reference GitHub, Inc. https://www.reddit.com/r/rails/comments/1exwtdm/camaleon_cms_281_has_been_released [No types assigned] Added CWE GitHub, Inc. CWE-74 Added CVSS V3.1 GitHub, Inc. AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H