CVE-2024-50550
WordPress LiteSpeed Cache plugin <= 6.5.1 - Privilege Escalation vulnerability
Description
Incorrect Privilege Assignment vulnerability in LiteSpeed Technologies LiteSpeed Cache litespeed-cache allows Privilege Escalation.This issue affects LiteSpeed Cache: from n/a through <= 6.5.1.
INFO
Published Date :
Oct. 29, 2024, 10:15 a.m.
Last Modified :
April 23, 2026, 3:20 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Public PoC/Exploit Available at Github
CVE-2024-50550 has a 3 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-50550.
| URL | Resource |
|---|---|
| https://patchstack.com/database/Wordpress/Plugin/litespeed-cache/vulnerability/wordpress-litespeed-cache-plugin-6-5-1-privilege-escalation-vulnerability?_s_id=cve |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-50550 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-50550
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
Python
None
Ostorlab KEV: One-command to detect most remotely known exploitable vulnerabilities. Sourced from CISA KEV, Google's Tsunami, Ostorlab's Asteroid and Bug Bounty programs.
cisa-kev vulnerability 0day cisa exploits
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-50550 vulnerability anywhere in the article.

-
Cybersecurity News
Elpaco Ransomware: A New Threat Actor Leverages CVE-2020-1472 for Global Attacks
Kaspersky Labs has unveiled a sophisticated new ransomware variant named Elpaco, which has emerged as an evolution of the Mimic ransomware family. This advanced malware exhibits a plethora of customiz ... Read more

-
Cybersecurity News
WolfsBane: Gelsemium APT Group’s Linux Backdoor Debut
WolfsBane execution chain | Image: ESETESET researchers have unveiled WolfsBane, the Linux counterpart to the Windows-based Gelsevirine backdoor, marking a significant milestone in the evolution of th ... Read more

-
The Hacker News
THN Recap: Top Cybersecurity Threats, Tools, and Practices (Oct 28 - Nov 03)
Weekly Recap / Cybersecurity This week was a total digital dumpster fire! Hackers were like, "Let's cause some chaos!" and went after everything from our browsers to those fancy cameras that zoom and ... Read more
-
TheCyberThrone
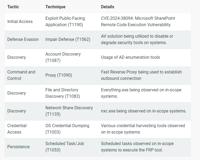
Microsoft Sharepoint Server CVE-2024-38094 Exploited
Threat actors have exploited a vulnerability in Microsoft SharePoint Server, identified as CVE-2024-38094, allowing them to gain complete domain access and compromise critical systems. The Rapid7 inci ... Read more

-
TheCyberThrone
WordPress Plugin LiteSpeed Cache Flaw CVE-2024-50550
Security researcher has identified a vulnerability in the LiteSpeed Cache plugin that could compromise WordPress sites with its unauthenticated privilege escalation capabilities.The vulnerability trac ... Read more

-
BleepingComputer
LiteSpeed Cache WordPress plugin bug lets hackers get admin access
The free version of the popular WordPress plugin LiteSpeed Cache has fixed a dangerous privilege elevation flaw on its latest release that could allow unauthenticated site visitors to gain admin right ... Read more

-
The Hacker News
LiteSpeed Cache Plugin Vulnerability Poses Significant Risk to WordPress Websites
Vulnerability / Website Security A high-severity security flaw has been disclosed in the LiteSpeed Cache plugin for WordPress that could allow an unauthenticated threat actor to elevate their privileg ... Read more

-
Cybersecurity News
Over 6 Million Sites at Risk: Severe Privilege Escalation Flaw CVE-2024-50550 in LiteSpeed Cache Plugin
Rafie Muhammad, a Security Researcher at Patchstack, reveals a severe security vulnerability in the LiteSpeed Cache plugin—a popular WordPress caching plugin with over six million active installations ... Read more
The following table lists the changes that have been made to the
CVE-2024-50550 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by [email protected]
Apr. 23, 2026
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H -
CVE Modified by [email protected]
Apr. 01, 2026
Action Type Old Value New Value Changed Description Incorrect Privilege Assignment vulnerability in LiteSpeed Technologies LiteSpeed Cache allows Privilege Escalation.This issue affects LiteSpeed Cache: from n/a through 6.5.1. Incorrect Privilege Assignment vulnerability in LiteSpeed Technologies LiteSpeed Cache litespeed-cache allows Privilege Escalation.This issue affects LiteSpeed Cache: from n/a through <= 6.5.1. Removed CVSS V3.1 AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H Added Reference https://patchstack.com/database/Wordpress/Plugin/litespeed-cache/vulnerability/wordpress-litespeed-cache-plugin-6-5-1-privilege-escalation-vulnerability?_s_id=cve Removed Reference https://patchstack.com/database/vulnerability/litespeed-cache/wordpress-litespeed-cache-plugin-6-5-1-privilege-escalation-vulnerability?_s_id=cve Removed Reference Type https://patchstack.com/database/vulnerability/litespeed-cache/wordpress-litespeed-cache-plugin-6-5-1-privilege-escalation-vulnerability?_s_id=cve Types: Third Party Advisory -
Initial Analysis by [email protected]
Mar. 07, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Added CWE CWE-326 Added CPE Configuration OR *cpe:2.3:a:litespeedtech:litespeed_cache:*:*:*:*:*:wordpress:*:* versions from (excluding) 6.5.2 Added Reference Type Patchstack: https://patchstack.com/database/vulnerability/litespeed-cache/wordpress-litespeed-cache-plugin-6-5-1-privilege-escalation-vulnerability?_s_id=cve Types: Third Party Advisory -
CVE Received by [email protected]
Oct. 29, 2024
Action Type Old Value New Value Added Description Incorrect Privilege Assignment vulnerability in LiteSpeed Technologies LiteSpeed Cache allows Privilege Escalation.This issue affects LiteSpeed Cache: from n/a through 6.5.1. Added Reference Patchstack https://patchstack.com/database/vulnerability/litespeed-cache/wordpress-litespeed-cache-plugin-6-5-1-privilege-escalation-vulnerability?_s_id=cve [No types assigned] Added CWE Patchstack CWE-266 Added CVSS V3.1 Patchstack AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H