CVE-2024-51567
CyberPanel Incorrect Default Permissions Vulnerability - [Actively Exploited]
Description
upgrademysqlstatus in databases/views.py in CyberPanel (aka Cyber Panel) before 5b08cd6 allows remote attackers to bypass authentication and execute arbitrary commands via /dataBases/upgrademysqlstatus by bypassing secMiddleware (which is only for a POST request) and using shell metacharacters in the statusfile property, as exploited in the wild in October 2024 by PSAUX. Versions through 2.3.6 and (unpatched) 2.3.7 are affected.
INFO
Published Date :
Oct. 29, 2024, 11:15 p.m.
Last Modified :
Nov. 7, 2025, 7:02 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
CyberPanel contains an incorrect default permissions vulnerability that allows a remote, unauthenticated attacker to execute commands as root.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Known Detected Feb 26, 2026
https://cyberpanel.net/blog/detials-and-fix-of-recent-security-issue-and-patch-of-cyberpanel ; https://nvd.nist.gov/vuln/detail/CVE-2024-51567
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Update CyberPanel to version 2.3.8.
- Alternatively, apply the provided patch.
Public PoC/Exploit Available at Github
CVE-2024-51567 has a 7 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-51567.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-51567 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-51567
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
Python HTML Dockerfile
CVE-2024-51567 is a Python PoC exploit targeting an RCE vulnerability in CyberPanel v2.3.6’s upgrademysqlstatus endpoint, bypassing CSRF protections.
Python
cbyerpanel rce exploit
Python
None
Python
CVE-2024-51567 is a Python PoC exploit targeting an RCE vulnerability in CyberPanel v2.3.6’s upgrademysqlstatus endpoint, bypassing CSRF protections.
cyberpanel cve-2024-51567
Python
CISA Bot is a GitHub bot that automatically monitors the Cybersecurity and Infrastructure Security Agency (CISA) Known Exploited Vulnerabilities (KEV) Catalog. When new vulnerabilities are published in the KEV, the bot creates GitHub issues in this repository with detailed information about each vulnerability.
Python
一个 CVE 漏洞预警知识库,无 exp/poc,部分包含修复方案。A knowledge base of CVE security vulnerability, no PoCs/exploits.
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-51567 vulnerability anywhere in the article.

-
The Hacker News
China-Linked Hackers Exploit SAP and SQL Server Flaws in Attacks Across Asia and Brazil
Vulnerability / Threat Intelligence The China-linked threat actor behind the recent in-the-wild exploitation of a critical security flaw in SAP NetWeaver has been attributed to a broader set of attack ... Read more

-
TheCyberThrone
Zeroday Vulnerabilities Prevailed in 2024 Analysis-Part II
This is the continuation of Zeroday vulnerabilities in 2024. Let’s delve deeply into the continuation of zero-day vulnerabilities of 2024, providing a comprehensive analysis.1. CVE-2023-46805: Authen ... Read more

-
Cybersecurity News
CVE-2024-51378 (CVSS 10): Critical CyberPanel Flaw Under Active Attack, CISA Warns
The Cybersecurity and Infrastructure Security Agency (CISA) has warned about a critical vulnerability in CyberPanel, an open-source web hosting control panel. This flaw, tracked as CVE-2024-51378, is ... Read more

-
TheCyberThrone
TheCyberThrone CyberSecurity Newsletter Top 5 Articles – November, 2024
Welcome to TheCyberThrone cybersecurity month in review will be posted covering the important security happenings . This review is for the month ending November, 2024Subscribers favorite #1Apache Airf ... Read more

-
Cybersecurity News
Critical Laravel Flaw (CVE-2024-52301) Exposes Millions of Web Applications to Attack
A critical security vulnerability, CVE-2024-52301, has been identified in the Laravel framework, a popular web application framework known for its elegant syntax and comprehensive toolset for building ... Read more

-
Cybersecurity News
CISA Flags Critical Exploits in Palo Alto Networks’ Expedition with Public PoC Code
The Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent warning about two critical vulnerabilities in Palo Alto Networks Expedition that malicious actors are actively exploiti ... Read more

-
The Register
Alleged Snowflake attacker gets busted by Canadians – politely, we assume
in brief One of the suspected masterminds behind the widespread Snowflake breach has been arrested in Canada – but the saga isn't over, eh. Alexander "Connor" Moucka was apprehended last week at the r ... Read more

-
TheCyberThrone
The CyberThrone most exploited vulnerabilities review – November 9, 2024
Welcome to TheCyberThrone most exploited vulnerabilities review. This review is for the weeks ending Saturday, November 9, 2024.Grafana LabsThe vulnerability tracked as CVE-2024-9264 with a 9.4-severi ... Read more

-
The Hacker News
CISA Alerts to Active Exploitation of Critical Palo Alto Networks Vulnerability
Vulnerability / Network Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a now-patched critical security flaw impacting Palo Alto Networks Expedition to its ... Read more

-
Cybersecurity News
CISA Expands KEV Catalog with Four Actively Exploited Vulnerabilities
The Cybersecurity and Infrastructure Security Agency (CISA) has issued an updated advisory regarding four security vulnerabilities actively exploited in the wild. These vulnerabilities, now included i ... Read more

-
Cybersecurity News
CVE-2024-43047 & CVE-2024-43093: Android Zero-Days Demand Immediate Patching
In its November 2024 security update, Google has addressed 40 security vulnerabilities in the Android operating system, two of which are flagged as actively exploited: CVE-2024-43047 and CVE-2024-4309 ... Read more

-
The Cyber Express
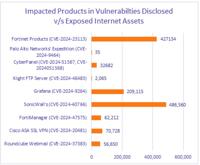
New Vulnerabilities in Fortinet, SonicWall, and Grafana Pose Significant Risks
Cyble Research and Intelligence Labs (CRIL) has identified new IT vulnerabilities affecting Fortinet, SonicWall, Grafana Labs, and CyberPanel, among others. The report for the week of October 23-29 hi ... Read more
-
The Cyber Express
Nearly 1 Million Vulnerable Fortinet, SonicWall Devices Exposed to the Web
Nearly 1 million Fortinet and SonicWall devices with actively exploited vulnerabilities are exposed on the internet, according to Cyble’s weekly vulnerability report published today. The report also l ... Read more

-
Cybersecurity News
Researcher Exposes Critical Vulnerabilities in Google Cloud
In a recent in-depth analysis, Christophe Tafani-Dereeper, a prominent Cloud Security Researcher at DATADOG, highlights critical vulnerabilities within Google Cloud’s default service accounts that put ... Read more

-
Help Net Security
Ransomware hits web hosting servers via vulnerable CyberPanel instances
A threat actor – or possibly several – has hit approximately 22,000 vulnerable instances of CyberPanel and encrypted files on the servers running it with the PSAUX and other ransomware. The PSAUX rans ... Read more

-
security.nl
'22.000 CyberPanel-servers via kritiek lek besmet met ransomware en offline'
Aanvallers hebben via kritieke kwetsbaarheden in CyberPanel 22.000 servers met ransomware geïnfecteerd, die daardoor offline gingen, zo stellen onderzoekers en securitybedrijf LeakIX. Voor getroffen g ... Read more

-
Cybersecurity News
PSAUX Ransomware is Exploiting Two Max Severity Flaws (CVE-2024-51567, CVE-2024-51568) in CyberPanel
Image: DreyAndThree critical remote code execution (RCE) vulnerabilities impacting CyberPanel, a widely used web hosting control panel, are under active exploitation. Threat actors are leveraging thes ... Read more
The following table lists the changes that have been made to the
CVE-2024-51567 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Nov. 07, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-51567 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-51567 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-51567 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-51567 -
Modified Analysis by [email protected]
Apr. 03, 2025
Action Type Old Value New Value -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Feb. 05, 2025
Action Type Old Value New Value Added CWE CWE-306 Removed CWE CWE-276 -
Initial Analysis by [email protected]
Nov. 08, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://cwe.mitre.org/data/definitions/420.html No Types Assigned https://cwe.mitre.org/data/definitions/420.html Technical Description Changed Reference Type https://cwe.mitre.org/data/definitions/78.html No Types Assigned https://cwe.mitre.org/data/definitions/78.html Technical Description Changed Reference Type https://cyberpanel.net/blog/detials-and-fix-of-recent-security-issue-and-patch-of-cyberpanel No Types Assigned https://cyberpanel.net/blog/detials-and-fix-of-recent-security-issue-and-patch-of-cyberpanel Product Changed Reference Type https://cyberpanel.net/KnowledgeBase/home/change-logs/ No Types Assigned https://cyberpanel.net/KnowledgeBase/home/change-logs/ Release Notes Changed Reference Type https://dreyand.rs/code/review/2024/10/27/what-are-my-options-cyberpanel-v236-pre-auth-rce No Types Assigned https://dreyand.rs/code/review/2024/10/27/what-are-my-options-cyberpanel-v236-pre-auth-rce Exploit, Patch Changed Reference Type https://github.com/usmannasir/cyberpanel/commit/5b08cd6d53f4dbc2107ad9f555122ce8b0996515 No Types Assigned https://github.com/usmannasir/cyberpanel/commit/5b08cd6d53f4dbc2107ad9f555122ce8b0996515 Patch Changed Reference Type https://www.bleepingcomputer.com/news/security/massive-psaux-ransomware-attack-targets-22-000-cyberpanel-instances/ No Types Assigned https://www.bleepingcomputer.com/news/security/massive-psaux-ransomware-attack-targets-22-000-cyberpanel-instances/ Press/Media Coverage Added CWE NIST CWE-306 Added CPE Configuration OR *cpe:2.3:a:cyberpanel:cyberpanel:*:*:*:*:*:*:*:* versions up to (excluding) 2.3.8 -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Nov. 08, 2024
Action Type Old Value New Value Added Due Date 2024-11-28 Added Vulnerability Name CyberPanel Incorrect Default Permissions Vulnerability Added Required Action Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. Added Date Added 2024-11-07 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 30, 2024
Action Type Old Value New Value Added CWE CISA-ADP CWE-276 -
CVE Received by [email protected]
Oct. 29, 2024
Action Type Old Value New Value Added Description upgrademysqlstatus in databases/views.py in CyberPanel (aka Cyber Panel) before 5b08cd6 allows remote attackers to bypass authentication and execute arbitrary commands via /dataBases/upgrademysqlstatus by bypassing secMiddleware (which is only for a POST request) and using shell metacharacters in the statusfile property, as exploited in the wild in October 2024 by PSAUX. Versions through 2.3.6 and (unpatched) 2.3.7 are affected. Added Reference MITRE https://cwe.mitre.org/data/definitions/78.html [No types assigned] Added Reference MITRE https://dreyand.rs/code/review/2024/10/27/what-are-my-options-cyberpanel-v236-pre-auth-rce [No types assigned] Added Reference MITRE https://github.com/usmannasir/cyberpanel/commit/5b08cd6d53f4dbc2107ad9f555122ce8b0996515 [No types assigned] Added Reference MITRE https://cyberpanel.net/KnowledgeBase/home/change-logs/ [No types assigned] Added Reference MITRE https://cwe.mitre.org/data/definitions/420.html [No types assigned] Added Reference MITRE https://cyberpanel.net/blog/detials-and-fix-of-recent-security-issue-and-patch-of-cyberpanel [No types assigned] Added Reference MITRE https://www.bleepingcomputer.com/news/security/massive-psaux-ransomware-attack-targets-22-000-cyberpanel-instances/ [No types assigned] Added CVSS V3.1 MITRE AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H