CVE-2024-6670
Progress WhatsUp Gold SQL Injection Vulnerability - [Actively Exploited]
Description
In WhatsUp Gold versions released before 2024.0.0, a SQL Injection vulnerability allows an unauthenticated attacker to retrieve the users encrypted password.
INFO
Published Date :
Aug. 29, 2024, 10:15 p.m.
Last Modified :
Oct. 31, 2025, 9:54 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Progress WhatsUp Gold contains a SQL injection vulnerability that allows an unauthenticated attacker to retrieve the user's encrypted password if the application is configured with only a single user.
Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable.
Known Detected Sep 16, 2024
https://community.progress.com/s/article/WhatsUp-Gold-Security-Bulletin-August-2024 ; https://nvd.nist.gov/vuln/detail/CVE-2024-6670
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Update to Progress WhatsUp Gold version 24.0.0 or later.
Public PoC/Exploit Available at Github
CVE-2024-6670 has a 4 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-6670.
| URL | Resource |
|---|---|
| https://community.progress.com/s/article/WhatsUp-Gold-Security-Bulletin-August-2024 | Vendor Advisory |
| https://www.progress.com/network-monitoring | Product |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-6670 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-6670 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-6670
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
a Python tool for visualizing and exploring CVEs (Common Vulnerabilities and Exposures) and information about them
Python
None
Python
Ostorlab KEV: One-command to detect most remotely known exploitable vulnerabilities. Sourced from CISA KEV, Google's Tsunami, Ostorlab's Asteroid and Bug Bounty programs.
cisa-kev vulnerability 0day cisa exploits
EPSS & VEDAS Score Aggregator for CVEs
cve vulnerability exploit epss vedas exploit-maturity
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-6670 vulnerability anywhere in the article.

-
Cybersecurity News
CVE-2024-12108 (CVSS 9.6) and Beyond: Progress Issues Critical Patch for WhatsUp Gold Network Monitoring Software
Progress Software Corporation, a global provider of products to develop, deploy, and manage high-impact business applications, has issued a critical security bulletin for its WhatsUp Gold network moni ... Read more

-
Cybersecurity News
Exploit Code Available: Critical Flaw Found in WhatsUp Gold- CVE-2024-8785 (CVSS 9.8)
Tenable’s latest vulnerability analysis has exposed a critical flaw, CVE-2024-8785, in WhatsUp Gold versions prior to 24.0.1. Rated with a CVSS score of 9.8, this vulnerability allows unauthenticated ... Read more

-
TheCyberThrone
Progress fixes Critical vulnerability in Whatsup Gold
Progress Software has disclosed a critical vulnerability in its popular network monitoring solution, WhatsUp Gold, that exposes organizations to potential cyberattacks by allowing unauthorized access ... Read more

-
Cybersecurity News
WhatsUp Gold Users Beware: Critical Authentication Bypass Flaw Exposed – CVE-2024-7763 (CVSS 9.8)
Progress Software has disclosed a severe new vulnerability in its popular network monitoring solution, WhatsUp Gold, that exposes organizations to potential cyberattacks by allowing unauthorized acces ... Read more

-
Cybersecurity News
CVE-2024-7490: Urgent Warning for IoT Devices Using Microchip ASF, No Patch Available
The latest vulnerability disclosure identifies a significant security flaw in the Microchip Advanced Software Framework (ASF), specifically within its tinydhcp server implementation. This vulnerabilit ... Read more

-
Cybersecurity News
Critical Dragonfly2 Flaw CVE-2023-27584: Hardcoded Key Threatens Admin Access
A serious security flaw has been uncovered in Dragonfly2, an open-source, peer-to-peer-based file distribution and image acceleration system. The vulnerability, CVE-2023-27584, carries a CVSS score of ... Read more

-
The Register
Apple's latest macOS release is breaking security software, network connections
Infosec In Brief Something's wrong with macOS Sequoia, and it's breaking security software installed on some updated Apple systems. Sequoia, aka macOS 15, was released on Monday of last week. By Thurs ... Read more

-
TheCyberThrone
CISA KEV Update September 2024 -Part V
The US CISA adds two vulnerabilities to its Known Exploited Vulnerabilities Catalog based on the evidence of active exploitationThe first vulnerability tracked as CVE-2024-43461, Microsoft Windows MSH ... Read more

-
Cybersecurity News
Faraday: Open Source Vulnerability Management Platform
In today’s complex cybersecurity landscape, security teams face the dual challenge of uncovering new vulnerabilities and efficiently managing remediation efforts. Faraday emerges as a powerful solutio ... Read more

-
Cybersecurity News
CISA Flags Two Actively Exploited Vulnerabilities: Critical Threats to Windows and WhatsUp Gold
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued a warning, adding two actively exploited security flaws to its Known Exploited Vulnerabilities (KEV) catalog, urging immedia ... Read more

-
The Hacker News
Progress WhatsUp Gold Exploited Just Hours After PoC Release for Critical Flaw
Software Security / Threat Intelligence Malicious actors are likely leveraging publicly available proof-of-concept (PoC) exploits for recently disclosed security flaws in Progress Software WhatsUp Gol ... Read more

-
BleepingComputer
Hackers targeting WhatsUp Gold with public exploit since August
Hackers have been leveraging publicly available exploit code for two critical vulnerabilities in the WhatsUp Gold network availability and performance monitoring solution from Progress Software. The t ... Read more

-
Cybersecurity News
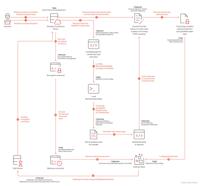
WhatsUp Gold Under Attack: New RCE Vulnerabilities Exploited
Timeline how the WhatsUp Gold Active Monitor PowerShell Script was abused | Image: Trend MicroTrend Micro researchers have uncovered a series of remote code execution (RCE) attacks targeting WhatsUp G ... Read more

-
Trend Micro
Protecting Against RCE Attacks Abusing WhatsUp Gold Vulnerabilities
Summary Trend Micro researchers identified remote code execution attacks on WhatsUp Gold exploiting the Active Monitor PowerShell Script since August 30. These attacks possibly leveraged vulnerabiliti ... Read more

-
Cybersecurity News
From Charging to Hijacking: The Autel MaxiCharger Vulnerability
Image: Sector 7The transition to electric vehicles (EVs) is rapidly gaining momentum, but the recent Pwn2Own Automotive 2024 competition in Tokyo has revealed a concerning vulnerability: EV chargers t ... Read more

-
Cybersecurity News
SonicWall Confirms Critical CVE-2024-40766 Vulnerability Actively Exploited in the Wild
On September 5, 2024, SonicWall updated its security advisory with an urgent warning: CVE-2024-40766, a critical access control vulnerability within SonicOS, is being actively exploited by cybercrimin ... Read more

-
security.nl
WhatsUp Gold-servers actief aangevallen via kritiek SQL Injection-lek
Opnieuw zijn WhatsUp Gold-servers het doelwit van aanvallen, waarbij aanvallers nu een kritieke SQL Injection-kwetsbaarheid gebruiken. Onlangs werden dergelijke systemen aangevallen via een kritiek pa ... Read more

-
Cybersecurity News
Proof-of-Concept Exploit Released for WhatsUp Gold Authentication Bypass (CVE-2024-6670)
Researcher Sina Kheirkhah of the Summoning Team has published the technical details and a proof-of-concept (PoC) exploit for a critical vulnerability, identified as CVE-2024-6670, affecting Progress S ... Read more
-
Cybersecurity News
Godzilla Backdoor: A Stealthy Threat Targeting Atlassian Confluence Flaw (CVE-2023-22527)
Attack chain | Image: TrendMicroA recent discovery by cybersecurity researchers at Trend Micro has unveiled a sophisticated new attack vector targeting Atlassian Confluence servers, leveraging the cri ... Read more

-
Cybersecurity News
Critical CVE-2024-45321 Flaw in Popular Perl Module Installer cpanminus, No Patch Available
In a significant security advisory, the Perl community has been alerted to a critical vulnerability, CVE-2024-45321, affecting the widely-used App::cpanminus (cpanm) tool. Rated with a CVSS score of 9 ... Read more
The following table lists the changes that have been made to the
CVE-2024-6670 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 31, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-6670 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-6670 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-6670 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2024-6670 -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Sep. 17, 2024
Action Type Old Value New Value Added Date Added 2024-09-16 Added Vulnerability Name Progress WhatsUp Gold SQL Injection Vulnerability Added Due Date 2024-10-07 Added Required Action Apply mitigations per vendor instructions or discontinue use of the product if mitigations are unavailable. -
Initial Analysis by [email protected]
Sep. 04, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://community.progress.com/s/article/WhatsUp-Gold-Security-Bulletin-August-2024 No Types Assigned https://community.progress.com/s/article/WhatsUp-Gold-Security-Bulletin-August-2024 Vendor Advisory Changed Reference Type https://www.progress.com/network-monitoring No Types Assigned https://www.progress.com/network-monitoring Product Added CWE NIST CWE-89 Added CPE Configuration OR *cpe:2.3:a:progress:whatsup_gold:*:*:*:*:*:*:*:* versions up to (excluding) 24.0 -
CVE Received by [email protected]
Aug. 29, 2024
Action Type Old Value New Value Added Description In WhatsUp Gold versions released before 2024.0.0, a SQL Injection vulnerability allows an unauthenticated attacker to retrieve the users encrypted password. Added Reference Progress Software Corporation https://www.progress.com/network-monitoring [No types assigned] Added Reference Progress Software Corporation https://community.progress.com/s/article/WhatsUp-Gold-Security-Bulletin-August-2024 [No types assigned] Added CWE Progress Software Corporation CWE-89 Added CVSS V3.1 Progress Software Corporation AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H