CVE-2024-6915
JFrog Artifactory Cache Poisoning
Description
JFrog Artifactory versions below 7.90.6, 7.84.20, 7.77.14, 7.71.23, 7.68.22, 7.63.22, 7.59.23, 7.55.18 are vulnerable to Improper Input Validation that could potentially lead to cache poisoning.
INFO
Published Date :
Aug. 5, 2024, 8:15 p.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] |
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-6915.
| URL | Resource |
|---|---|
| https://jfrog.com/help/r/jfrog-release-information/jfrog-security-advisories |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-6915 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-6915
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-6915 vulnerability anywhere in the article.

-
Daily CyberSecurity
Backdoor Disguised as SOCKS5 Proxy: Malicious PyPI Package SoopSocks Grants Root Access
The security of the open-source software supply chain was once again tested when JFrog’s security research team uncovered a malicious package on PyPI. The package, named SoopSocks (XRAY-725599), masqu ... Read more
-
Cybersecurity News
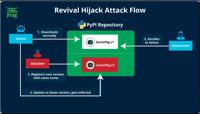
Revival Hijack: A New PyPI Hijacking Technique Threatens Thousands of Packages
The JFrog security research team has uncovered a novel PyPI package hijacking method known as “Revival Hijack,” which has put over 22,000 packages at risk of exploitation. Unlike traditional typosquat ... Read more

-
Cybersecurity News
CVE-2024-7971: North Korean APT Citrine Sleet Exploits Chromium Zero-Day
In a recent cybersecurity report, Microsoft Threat Intelligence has revealed that a North Korean threat actor, believed to be Citrine Sleet, has been actively exploiting a zero-day vulnerability (CVE- ... Read more

-
Cybersecurity News
CVE-2024-6386 (CVSS 9.9) in WPML Plugin Exposes Millions of WordPress Sites to RCE Attacks
A severe security flaw (CVE-2024-6386, CVSS 9.9) has been discovered in the widely-used WPML plugin for WordPress, potentially exposing over one million websites to the risk of complete takeover. The ... Read more

-
Cybersecurity News
Researcher Details Microsoft Outlook Zero-Click Vulnerability (CVE-2024-38021)
Morphisec researchers have detailed a critical vulnerability in Microsoft Outlook, identified as CVE-2024-38021, which has the potential to allow remote attackers to execute arbitrary code on vulnerab ... Read more

-
Cybersecurity News
CVE-2024-33533 to 33536: Zimbra Users at Risk of XSS and LFI Attacks
Zimbra Collaboration, a widely adopted email and collaboration platform disclosed three new security vulnerabilities. These flaws, identified as CVE-2024-33533, CVE-2024-33535, and CVE-2024-33536, imp ... Read more

-
Cybersecurity News
CISA & Microsoft Warn of 6 Actively Exploited Zero-Day Vulnerabilities
Microsoft’s August 2024 Patch Tuesday release addresses 88 vulnerabilities, including seven critical flaws and 10 zero-day vulnerabilities. Among these, six are currently being actively exploited in t ... Read more

-
Cyber Security News
Jfrog Artifactory Flaw Let Attackers Poison Artifact Caches
A critical vulnerability identified as CVE-2024-6915 has been discovered in JFrog Artifactory, a widely used repository manager. This flaw, categorized under CWE-20 (Improper Input Validation), allows ... Read more
The following table lists the changes that have been made to the
CVE-2024-6915 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Received by [email protected]
Aug. 05, 2024
Action Type Old Value New Value Added Description JFrog Artifactory versions below 7.90.6, 7.84.20, 7.77.14, 7.71.23, 7.68.22, 7.63.22, 7.59.23, 7.55.18 are vulnerable to Improper Input Validation that could potentially lead to cache poisoning. Added Reference JFrog https://jfrog.com/help/r/jfrog-release-information/jfrog-security-advisories [No types assigned] Added CWE JFrog CWE-20 Added CVSS V3.1 JFrog AV:N/AC:L/PR:N/UI:N/S:C/C:N/I:H/A:L