CVE-2024-7261
Zyxel NWA1123AC/v WagonWeb Command Injection
Description
The improper neutralization of special elements in the parameter "host" in the CGI program of Zyxel NWA1123ACv3 firmware version 6.70(ABVT.4) and earlier, WAC500 firmware version 6.70(ABVS.4) and earlier, WAX655E firmware version 7.00(ACDO.1) and earlier, WBE530 firmware version 7.00(ACLE.1) and earlier, and USG LITE 60AX firmware version V2.00(ACIP.2) could allow an unauthenticated attacker to execute OS commands by sending a crafted cookie to a vulnerable device.
INFO
Published Date :
Sept. 3, 2024, 3:15 a.m.
Last Modified :
Sept. 13, 2024, 7:39 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2024-7261
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] |
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-7261.
| URL | Resource |
|---|---|
| https://www.zyxel.com/global/en/support/security-advisories/zyxel-security-advisory-for-os-command-injection-vulnerability-in-aps-and-security-router-devices-09-03-2024 | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-7261 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-7261
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-7261 vulnerability anywhere in the article.

-
Cybersecurity News
Protect Your Network: Zyxel Issues Firmware Updates
Zyxel Networks has released firmware updates to address multiple vulnerabilities affecting a range of its networking products, including 4G LTE/5G NR CPEs, DSL/Ethernet CPEs, fiber ONTs, and WiFi exte ... Read more

-
Cybersecurity News
Critical WatchGuard Vulnerabilities Discovered: CVE-2024-6592 and CVE-2024-6593
Cybersecurity firm RedTeam Pentesting GmbH has disclosed two critical vulnerabilities, CVE-2024-6592 and CVE-2024-6593, in WatchGuard’s Authentication Gateway (also known as Single Sign-On Agent) and ... Read more

-
Cybersecurity News
Critical SQL Injection Vulnerability Discovered in ‘The Events Calendar’ WordPress Plugin (CVE-2024-8275)
A severe security flaw has been identified in the popular WordPress plugin The Events Calendar, affecting all versions up to and including 6.6.4. Designated as CVE-2024-8275, the vulnerability has bee ... Read more

-
Cybersecurity News
TeamViewer Urges Users to Patch Privilege Escalation Flaws (CVE-2024-7479 and CVE-2024-7481)
In a recently disclosed security bulletin, TeamViewer has highlighted two critical vulnerabilities impacting its Remote Client and Remote Host products for Windows. CVE-2024-7479 and CVE-2024-7481—bot ... Read more

-
Cybersecurity News
Citrix Workspace App Users Urged to Update Following Two Privilege Escalation Flaws
In a security advisory released recently, Cloud Software Group has disclosed two vulnerabilities affecting the widely used Citrix Workspace app for Windows. These vulnerabilities, identified as CVE-20 ... Read more
-
Cybersecurity News
CosmicBeetle’s ScRansom Ransomware: A Growing Threat to European and Asian Businesses
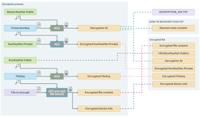
Encryption scheme utilized by the latest ScRansom samples | Image: ESETIn a significant development tracked by ESET researchers, the threat actor known as CosmicBeetle has intensified its ransomware o ... Read more

-
Cybersecurity News
LNK Stomping (CVE-2024-38217): Microsoft Patches Years-Old Zero-Day Flaw
Image: Elastic SecurityMicrosoft’s September 2024 security update addresses a zero-day vulnerability affecting Smart App Control and SmartScreen. This vulnerability, dubbed “LNK stomping” (CVE-2024-38 ... Read more

-
TheCyberThrone
CISA KEV Update Part II – September 2024.
The US CISA added below vulnerabilities to the Known Exploited Vulnerability Catalog based on the evidence of active exploitationCVE-2024-40766 SonicWall SonicOS contains an improper access control vu ... Read more

-
Help Net Security
Week in review: Vulnerability allows Yubico security keys cloning, Patch Tuesday forecast
Here’s an overview of some of last week’s most interesting news, articles, interviews and videos: Vulnerability allows Yubico security keys to be cloned Researchers have unearthed a cryptographic vuln ... Read more

-
TheCyberThrone
Veeam fixes several vulnerabilities in its products
Several critical vulnerabilities have been discovered in Veeam Service Provider Console and Veeam Backup & Replication could allow attackers to gain unauthorized access, execute malicious code, and po ... Read more

-
TheCyberThrone
Zyxel fixes Critical Vulnerability CVE-2024-7261
Zyxel released updates to fix a critical vulnerability that impacts 28 access points (AP) and security router version.The Zyxel vulnerability is tracked as CVE-2024-7261 CVSS score of 9.8, which is co ... Read more

-
Ars Technica
Zyxel warns of vulnerabilities in a wide range of its products
GET YER PATCHING ON — Most serious vulnerabilities carry severity ratings of 9.8 and 8.1 out of a possible 10. Getty Images Networking hardware-maker Zyxel is warning of nearly a dozen vulnerabilit ... Read more

-
The Hacker News
Zyxel Patches Critical OS Command Injection Flaw in Access Points and Routers
Vulnerability / Network Security Zyxel has released software updates to address a critical security flaw impacting certain access point (AP) and security router versions that could result in the execu ... Read more

-
security.nl
Zyxel-accesspoints via kritieke kwetsbaarheid op afstand over te nemen
Zyxel waarschuwt eigenaren van verschillende accesspoints en een 'security router' voor een kritieke kwetsbaarheid waardoor de apparaten op afstand door een ongeauthenticeerde aanvaller zijn over te n ... Read more

-
BleepingComputer
Zyxel warns of critical OS command injection flaw in routers
Zyxel has released security updates to address a critical vulnerability impacting multiple models of its business routers, potentially allowing unauthenticated attackers to perform OS command injectio ... Read more

-
Help Net Security
Critical flaw in Zyxel’s secure routers allows OS command execution via cookie (CVE-2024-7261)
Zyxel has patched a myriad of vulnerabilities in its various networking devices, including a critical one (CVE-2024-7261) that may allow unauthenticated attackers to execute OS commands on many Zyxel ... Read more

-
Cybersecurity News
CVE-2024-7261 (CVSS 9.8): Zyxel Patches Critical Vulnerability in Wi-Fi Devices
Zyxel, a prominent networking equipment manufacturer, has issued a security advisory urging users to promptly update their firmware to address a critical vulnerability affecting a range of their acces ... Read more
The following table lists the changes that have been made to the
CVE-2024-7261 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Sep. 13, 2024
Action Type Old Value New Value Changed Reference Type https://www.zyxel.com/global/en/support/security-advisories/zyxel-security-advisory-for-os-command-injection-vulnerability-in-aps-and-security-router-devices-09-03-2024 No Types Assigned https://www.zyxel.com/global/en/support/security-advisories/zyxel-security-advisory-for-os-command-injection-vulnerability-in-aps-and-security-router-devices-09-03-2024 Vendor Advisory Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa110ax_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(abtg.2\) OR cpe:2.3:h:zyxel:nwa110ax:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa1123-ac_pro_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 6.28\(abhd.3\) OR cpe:2.3:h:zyxel:nwa1123-ac_pro:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa1123acv3_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 6.70\(abvt.5\) OR cpe:2.3:h:zyxel:nwa1123acv3:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa130be_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(acil.2\) OR cpe:2.3:h:zyxel:nwa130be:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa210ax_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(abtd.2\) OR cpe:2.3:h:zyxel:nwa210ax:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa220ax-6e_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(acco.2\) OR cpe:2.3:h:zyxel:nwa220ax-6e:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa50ax_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(abyw.2\) OR cpe:2.3:h:zyxel:nwa50ax:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa50ax_pro_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(acge.2\) OR cpe:2.3:h:zyxel:nwa50ax_pro:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa55axe_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(abzl.2\) OR cpe:2.3:h:zyxel:nwa55axe:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa90ax_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(accv.2\) OR cpe:2.3:h:zyxel:nwa90ax:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:nwa90ax_pro_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(acgf.2\) OR cpe:2.3:h:zyxel:nwa90ax_pro:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:usg_lite_60ax_firmware:*:*:*:*:*:*:*:* versions up to (excluding) v2.00\(acip.3\) OR cpe:2.3:h:zyxel:usg_lite_60ax:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wac500_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 6.70\(abvs.5\) OR cpe:2.3:h:zyxel:wac500:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wac500h_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 6.70\(abwa.5\) OR cpe:2.3:h:zyxel:wac500h:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wac6103d-i_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 6.28\(aaxh.3\) OR cpe:2.3:h:zyxel:wac6103d-i:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wac6502d-s_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 6.28\(aase.3\) OR cpe:2.3:h:zyxel:wac6502d-s:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wac6503d-s_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 6.28\(aasf.3\) OR cpe:2.3:h:zyxel:wac6503d-s:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wac6552d-s_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 6.28\(abio.3\) OR cpe:2.3:h:zyxel:wac6552d-s:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wac6553d-e_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 6.28\(aasg.3\) OR cpe:2.3:h:zyxel:wac6553d-e:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wax300h_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(achf.2\) OR cpe:2.3:h:zyxel:wax300h:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wax510d_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(abtf.2\) OR cpe:2.3:h:zyxel:wax510d:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wax610d_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(abte.2\) OR cpe:2.3:h:zyxel:wax610d:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wax620d-6e_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(accn.2\) OR cpe:2.3:h:zyxel:wax620d-6e:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wax630s_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(abzd.2\) OR cpe:2.3:h:zyxel:wax630s:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wax640s-6e_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(accm.2\) OR cpe:2.3:h:zyxel:wax640s-6e:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wax650s_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(abrm.2\) OR cpe:2.3:h:zyxel:wax650s:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wax655e_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(acdo.2\) OR cpe:2.3:h:zyxel:wax655e:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wbe530_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(acle.2\) OR cpe:2.3:h:zyxel:wbe530:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:zyxel:wbe660s_firmware:*:*:*:*:*:*:*:* versions up to (excluding) 7.00\(acgg.2\) OR cpe:2.3:h:zyxel:wbe660s:-:*:*:*:*:*:*:* -
CVE Received by [email protected]
Sep. 03, 2024
Action Type Old Value New Value Added Description The improper neutralization of special elements in the parameter "host" in the CGI program of Zyxel NWA1123ACv3 firmware version 6.70(ABVT.4) and earlier, WAC500 firmware version 6.70(ABVS.4) and earlier, WAX655E firmware version 7.00(ACDO.1) and earlier, WBE530 firmware version 7.00(ACLE.1) and earlier, and USG LITE 60AX firmware version V2.00(ACIP.2) could allow an unauthenticated attacker to execute OS commands by sending a crafted cookie to a vulnerable device. Added Reference Zyxel Corporation https://www.zyxel.com/global/en/support/security-advisories/zyxel-security-advisory-for-os-command-injection-vulnerability-in-aps-and-security-router-devices-09-03-2024 [No types assigned] Added CWE Zyxel Corporation CWE-78 Added CVSS V3.1 Zyxel Corporation AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H