CVE-2024-7646
"Ingress-Nginx Unsecured Command Injection and Credential Exposure"
Description
A security issue was discovered in ingress-nginx where an actor with permission to create Ingress objects (in the `networking.k8s.io` or `extensions` API group) can bypass annotation validation to inject arbitrary commands and obtain the credentials of the ingress-nginx controller. In the default configuration, that credential has access to all secrets in the cluster.
INFO
Published Date :
Aug. 16, 2024, 6:15 p.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Public PoC/Exploit Available at Github
CVE-2024-7646 has a 6 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-7646.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-7646 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-7646
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
K8 Security Lab
CSS JavaScript HTML Shell
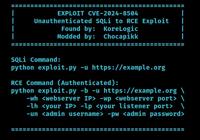
Walkthrough: ingress-nginx Configuration Injection via rewrite-target Annotation
cwe-20 kubernetes nginx rce
None
C Java Kotlin Python Ruby TypeScript HCL Dockerfile Shell
PoC CVE-2024-7646
PoC CVE-2024-7646
poc for CVE-2024-7646
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-7646 vulnerability anywhere in the article.

-
Cybersecurity News
Researcher Drops PoC for 9.8 CVSS Ingress-NGINX CVE-2025-1974 Flaw in Kubernetes
A series of critical security vulnerabilities has been discovered in the Ingress-NGINX Controller for Kubernetes, posing a significant risk to Kubernetes deployments. Security researcher Jacob Sandum ... Read more
-
Cybersecurity News
Critical Flaws Found in VICIdial Contact Center Suite: CVE-2024-8503 and CVE-2024-8504, PoC Published
In a concerning development for call centers using VICIdial, a popular open-source contact center solution, two high-severity security vulnerabilities have been discovered that could lead to severe da ... Read more
-
Cybersecurity News
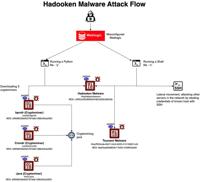
Hadooken Malware: A New Threat to WebLogic Servers
The entire attack flow | Image: Aqua NautilusCybersecurity researchers at Aqua Nautilus have discovered a new Linux malware strain, dubbed “Hadooken,” that is specifically targeting Oracle WebLogic se ... Read more

-
Cybersecurity News
Cisco Issues Security Advisories: Critical Vulnerabilities Impact Multiple Products
Cisco Systems has released a series of urgent security advisories, revealing a total of nine vulnerabilities affecting various products, including Cisco IOS XR Software, Crosswork Network Services Orc ... Read more

-
Cybersecurity News
HAProxy Vulnerability CVE-2024-45506 Under Active Exploit: Urgent Patching Required
In the latest security advisory, HAProxy revealed that CVE-2024-45506, a vulnerability in its popular load balancing and proxy software, is now actively exploited. The vulnerability, which has a CVSS ... Read more

-
Cybersecurity News
CVE-2024-7988 (CVSS 9.8): Rockwell Automation’s ThinManager Flaw Allows RCE
Rockwell Automation has issued a critical security advisory concerning multiple vulnerabilities discovered in its ThinManager ThinServer software. These vulnerabilities, reported by Nicholas Zubrisky ... Read more

-
Cybersecurity News
CVE-2024-43403: Kanister Vulnerability Opens Door to Cluster-Level Privilege Escalation
A critical vulnerability in the popular data protection workflow management tool, Kanister, has been discovered, potentially allowing attackers to gain full control over Kubernetes clusters. The vulne ... Read more

-
Cybersecurity News
Styx Stealer: The Evolved Threat to Your Crypto and Data
Recently, Check Point Research (CPR) discovered a new malware variant, Styx Stealer. Derived from the notorious Phemedrone Stealer, Styx was being sold via subscription with advanced capabilities such ... Read more

-
The Hacker News
Researchers Uncover TLS Bootstrap Attack on Azure Kubernetes Clusters
Vulnerability / Container Security Cybersecurity researchers have disclosed a security flaw impacting Microsoft Azure Kubernetes Services that, if successfully exploited, could allow an attacker to es ... Read more

-
Cyber Security News
New Kubernetes Vulnerability Allows Attackers to Access Clusters Remotely
A critical vulnerability tracked as CVE-2024-7646, has been uncovered in the widely used ingress-nginx Kubernetes controller. The flaw allows attackers to bypass annotation validation, poses a signifi ... Read more

-
Cybersecurity News
HookChain: The Technique That Bypass Exposes EDR in 94% of Security Solutions
Image Credit: M4v3r1ckIn an ever-evolving cybersecurity landscape, where threats are becoming more sophisticated by the day, the focus on Endpoint Detection and Response (EDR) systems has never been m ... Read more

-
Cybersecurity News
CVE-2024-7646: A Threat to Kubernetes Clusters Running ingress-nginx
A newly discovered security vulnerability, CVE-2024-7646, has been identified in the widely used ingress-nginx controller for Kubernetes, posing a severe threat to multi-tenant environments. With a CV ... Read more
The following table lists the changes that have been made to the
CVE-2024-7646 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference http://www.openwall.com/lists/oss-security/2024/08/16/5 -
CVE Received by [email protected]
Aug. 16, 2024
Action Type Old Value New Value Added Description A security issue was discovered in ingress-nginx where an actor with permission to create Ingress objects (in the `networking.k8s.io` or `extensions` API group) can bypass annotation validation to inject arbitrary commands and obtain the credentials of the ingress-nginx controller. In the default configuration, that credential has access to all secrets in the cluster. Added Reference Kubernetes https://github.com/kubernetes/kubernetes/issues/126744 [No types assigned] Added Reference Kubernetes https://groups.google.com/g/kubernetes-security-announce/c/a1__cKjWkfA [No types assigned] Added Reference Kubernetes https://github.com/kubernetes/ingress-nginx/pull/11719 [No types assigned] Added Reference Kubernetes https://github.com/kubernetes/ingress-nginx/pull/11721 [No types assigned] Added CWE Kubernetes CWE-20 Added CVSS V3.1 Kubernetes AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H