CVE-2024-7923
Puppet-pulpcore: an authentication bypass vulnerability exists in pulpcore
Description
An authentication bypass vulnerability has been identified in Pulpcore when deployed with Gunicorn versions prior to 22.0, due to the puppet-pulpcore configuration. This issue arises from Apache's mod_proxy not properly unsetting headers because of restrictions on underscores in HTTP headers, allowing authentication through a malformed header. This flaw impacts all active Satellite deployments (6.13, 6.14 and 6.15) which are using Pulpcore version 3.0+ and could potentially enable unauthorized users to gain administrative access.
INFO
Published Date :
Sept. 4, 2024, 2:15 p.m.
Last Modified :
Nov. 24, 2024, 7:15 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.0 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Update the affected packages.
- Update the foreman-installer and/or foreman-installer-katello packages.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-7923.
| URL | Resource |
|---|---|
| https://access.redhat.com/errata/RHSA-2024:6335 | Vendor Advisory |
| https://access.redhat.com/errata/RHSA-2024:6336 | Vendor Advisory |
| https://access.redhat.com/errata/RHSA-2024:6337 | Vendor Advisory |
| https://access.redhat.com/errata/RHSA-2024:8906 | |
| https://access.redhat.com/security/cve/CVE-2024-7923 | Vendor Advisory |
| https://bugzilla.redhat.com/show_bug.cgi?id=2305718 | Issue Tracking |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-7923 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-7923
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-7923 vulnerability anywhere in the article.

-
Cybersecurity News
PLANET Technology Switches Face CVE-2024-8456 (CVSS 9.8), Urgent Firmware Updates Advised
The Taiwan Computer Emergency Response Team (TWCERT/CC) has released a series of security advisories highlighting critical vulnerabilities affecting various PLANET Technology switch models. These vuln ... Read more

-
Cybersecurity News
CVSS 9.8 Vulnerabilities Expose Aruba Access Points to RCE: HPE Urges Immediate Action
The Hewlett Packard Enterprise (HPE) Product Security Response Team has issued a critical advisory concerning multiple command injection vulnerabilities (CVE-2024-42505, CVE-2024-42506, CVE-2024-42507 ... Read more

-
Cybersecurity News
CVE-2024-47062 (CVSS 9.4): Flaws Discovered in Navidrome Music Server Expose Sensitive Data
In a newly published security advisory, several critical vulnerabilities have been identified in Navidrome, a popular open-source music streaming server. These flaws, disclosed under CVE-2024-47062 wi ... Read more
-
Cybersecurity News
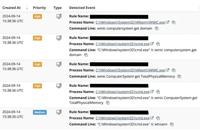
Hackers Exploit Foundation Software, Exposing Sensitive Contractor Data
Attacker commands enumerating machine details | Image: HuntressRecently, the cybersecurity company Huntress reported a new wave of cyberattacks targeting the widely-used Foundation Accounting Software ... Read more

-
Cybersecurity News
CVE-2024-35783 (CVSS 9.4): Critical-Severity Flaw Exposes Siemens Industrial Systems
Siemens has issued a critical security advisory regarding a remote code execution (RCE) vulnerability in several of its SIMATIC products, including SIMATIC Process Historian, SIMATIC PCS 7, and SIMATI ... Read more

-
Cybersecurity News
Red Hat Issues Critical Patch for Pulpcore Authentication Bypass Flaw (CVE-2024-7923)
Red Hat has issued a critical security advisory warning of an authentication bypass vulnerability (CVE-2024-7923) in Pulpcore, a content management system used in Red Hat Satellite deployments. The vu ... Read more
The following table lists the changes that have been made to the
CVE-2024-7923 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by [email protected]
Nov. 24, 2024
Action Type Old Value New Value Added Reference https://access.redhat.com/errata/RHSA-2024:8906 -
Initial Analysis by [email protected]
Sep. 05, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://access.redhat.com/errata/RHSA-2024:6335 No Types Assigned https://access.redhat.com/errata/RHSA-2024:6335 Vendor Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:6336 No Types Assigned https://access.redhat.com/errata/RHSA-2024:6336 Vendor Advisory Changed Reference Type https://access.redhat.com/errata/RHSA-2024:6337 No Types Assigned https://access.redhat.com/errata/RHSA-2024:6337 Vendor Advisory Changed Reference Type https://access.redhat.com/security/cve/CVE-2024-7923 No Types Assigned https://access.redhat.com/security/cve/CVE-2024-7923 Vendor Advisory Changed Reference Type https://bugzilla.redhat.com/show_bug.cgi?id=2305718 No Types Assigned https://bugzilla.redhat.com/show_bug.cgi?id=2305718 Issue Tracking Added CPE Configuration OR *cpe:2.3:a:redhat:satellite:6.13:*:*:*:*:*:*:* *cpe:2.3:a:redhat:satellite:6.14:*:*:*:*:*:*:* *cpe:2.3:a:redhat:satellite:6.15:*:*:*:*:*:*:* -
CVE Modified by [email protected]
Sep. 04, 2024
Action Type Old Value New Value Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:6335 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:6336 [No types assigned] Added Reference Red Hat, Inc. https://access.redhat.com/errata/RHSA-2024:6337 [No types assigned] -
CVE Modified by [email protected]
Sep. 04, 2024
Action Type Old Value New Value Changed Description An authentication bypass vulnerability has been identified in Foreman when deployed with Gunicorn versions prior to 22.0, due to the puppet-foreman configuration. This issue arises from Apache's mod_proxy not properly unsetting headers because of restrictions on underscores in HTTP headers, allowing authentication through a malformed header. This flaw impacts all active Satellite deployments (6.13, 6.14 and 6.15) which are using Pulpcore version 4.0+ and could potentially enable unauthorized users to gain administrative access. An authentication bypass vulnerability has been identified in Pulpcore when deployed with Gunicorn versions prior to 22.0, due to the puppet-pulpcore configuration. This issue arises from Apache's mod_proxy not properly unsetting headers because of restrictions on underscores in HTTP headers, allowing authentication through a malformed header. This flaw impacts all active Satellite deployments (6.13, 6.14 and 6.15) which are using Pulpcore version 3.0+ and could potentially enable unauthorized users to gain administrative access. Removed CVSS V3 Red Hat, Inc. AV:L/AC:L/PR:H/UI:N/S:U/C:L/I:L/A:L Added CVSS V3 Red Hat, Inc. AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H -
CVE Received by [email protected]
Sep. 04, 2024
Action Type Old Value New Value Added Description An authentication bypass vulnerability has been identified in Foreman when deployed with Gunicorn versions prior to 22.0, due to the puppet-foreman configuration. This issue arises from Apache's mod_proxy not properly unsetting headers because of restrictions on underscores in HTTP headers, allowing authentication through a malformed header. This flaw impacts all active Satellite deployments (6.13, 6.14 and 6.15) which are using Pulpcore version 4.0+ and could potentially enable unauthorized users to gain administrative access. Added Reference Red Hat, Inc. https://access.redhat.com/security/cve/CVE-2024-7923 [No types assigned] Added Reference Red Hat, Inc. https://bugzilla.redhat.com/show_bug.cgi?id=2305718 [No types assigned] Added CWE Red Hat, Inc. CWE-287 Added CVSS V3 Red Hat, Inc. AV:L/AC:L/PR:H/UI:N/S:U/C:L/I:L/A:L