CVE-2024-8640
Improper Neutralization of Special Elements used in a Command ('Command Injection') in GitLab
Description
An issue has been discovered in GitLab EE affecting all versions starting from 16.11 prior to 17.1.7, from 17.2 prior to 17.2.5, and from 17.3 prior to 17.3.2. Due to incomplete input filtering, it was possible to inject commands into a connected Cube server.
INFO
Published Date :
Sept. 12, 2024, 5:15 p.m.
Last Modified :
Nov. 21, 2024, 9:53 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Upgrade GitLab to version 17.1.7, 17.2.5, or 17.3.2 or later.
- Update the affected packages.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-8640.
| URL | Resource |
|---|---|
| https://gitlab.com/gitlab-org/gitlab/-/issues/486213 | Broken Link |
| https://hackerone.com/reports/2687770 | Permissions Required |
| https://about.gitlab.com/releases/2024/09/11/patch-release-gitlab-17-3-2-released/ |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-8640 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-8640
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-8640 vulnerability anywhere in the article.

-
Cybersecurity News
LemonDuck Exploits EternalBlue Vulnerability for Cryptomining Attacks
A recent report from security researchers at Aufa and NetbyteSEC Interns sheds light on the resurgence of the LemonDuck malware, which is now exploiting the EternalBlue vulnerability (CVE-2017-0144) i ... Read more
-
Cybersecurity News
Threat Actors Exploit HR-Related Phishing Tactics in Sophisticated Credential-Stealing Campaigns
Image: CofensePhishing attacks continue to evolve in complexity, and the latest report from the Cofense Phishing Defense Center highlights a troubling trend: cybercriminals are increasingly using HR-r ... Read more

-
Cybersecurity News
The Safe C++ Extensions Proposal: Strengthening Security in a Complex Ecosystem
In a decisive move to address long-standing memory safety concerns, the C++ community has unveiled the Safe C++ Extensions proposal, marking a crucial moment for the language. After two years of in-de ... Read more
-
Cybersecurity News
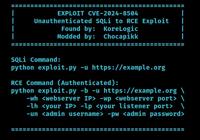
Critical Flaws Found in VICIdial Contact Center Suite: CVE-2024-8503 and CVE-2024-8504, PoC Published
In a concerning development for call centers using VICIdial, a popular open-source contact center solution, two high-severity security vulnerabilities have been discovered that could lead to severe da ... Read more
-
Cybersecurity News
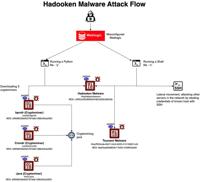
Hadooken Malware: A New Threat to WebLogic Servers
The entire attack flow | Image: Aqua NautilusCybersecurity researchers at Aqua Nautilus have discovered a new Linux malware strain, dubbed “Hadooken,” that is specifically targeting Oracle WebLogic se ... Read more

-
TheCyberThrone
GitLab fixes several vulnerabilities including CVE-2024-6678
GitLab has released critical security patches for its Community Edition (CE) and Enterprise Edition (EE) that could allow an attacker to execute arbitrary code.Vulnerability detailsCVE-2024-6678 with ... Read more

-
BleepingComputer
GitLab warns of critical pipeline execution vulnerability
GitLab has released critical updates to address multiple vulnerabilities, the most severe of them (CVE-2024-6678) allowing an attacker to trigger pipelines as arbitrary users under certain conditions. ... Read more

-
The Cyber Express
GitLab Issues Critical Patch Releases: Versions 17.3.2, 17.2.5, and 17.1.7 Address Key Vulnerabilities
GitLab has released critical patch updates across its Community Edition (CE) and Enterprise Edition (EE) to address security vulnerabilities and bugs. The GitLab critical patch release includes vital ... Read more

-
Cybersecurity News
GitLab Issues Critical Security Patch for CVE-2024-6678 (CVSS 9.9), Urges Immediate Update
In a recent security advisory, GitLab announced the release of critical security patches for its Community Edition (CE) and Enterprise Edition (EE). The patches address several vulnerabilities, includ ... Read more
The following table lists the changes that have been made to the
CVE-2024-8640 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 21, 2024
Action Type Old Value New Value Added Reference https://about.gitlab.com/releases/2024/09/11/patch-release-gitlab-17-3-2-released/ -
Initial Analysis by [email protected]
Sep. 14, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://gitlab.com/gitlab-org/gitlab/-/issues/486213 No Types Assigned https://gitlab.com/gitlab-org/gitlab/-/issues/486213 Broken Link Changed Reference Type https://hackerone.com/reports/2687770 No Types Assigned https://hackerone.com/reports/2687770 Permissions Required Added CWE NIST CWE-77 Added CPE Configuration OR *cpe:2.3:a:gitlab:gitlab:*:*:*:*:enterprise:*:*:* versions from (including) 16.11.0 up to (excluding) 17.1.7 *cpe:2.3:a:gitlab:gitlab:*:*:*:*:enterprise:*:*:* versions from (including) 17.2.0 up to (excluding) 17.2.5 *cpe:2.3:a:gitlab:gitlab:*:*:*:*:enterprise:*:*:* versions from (including) 17.3.0 up to (excluding) 17.3.2 -
CVE Received by [email protected]
Sep. 12, 2024
Action Type Old Value New Value Added Description An issue has been discovered in GitLab EE affecting all versions starting from 16.11 prior to 17.1.7, from 17.2 prior to 17.2.5, and from 17.3 prior to 17.3.2. Due to incomplete input filtering, it was possible to inject commands into a connected Cube server. Added Reference GitLab Inc. https://gitlab.com/gitlab-org/gitlab/-/issues/486213 [No types assigned] Added Reference GitLab Inc. https://hackerone.com/reports/2687770 [No types assigned] Added CWE GitLab Inc. CWE-77 Added CVSS V3.1 GitLab Inc. AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H