CVE-2024-8923
Sandbox Escape in Now Platform
Description
ServiceNow has addressed an input validation vulnerability that was identified in the Now Platform. This vulnerability could enable an unauthenticated user to remotely execute code within the context of the Now Platform. ServiceNow deployed an update to hosted instances and ServiceNow provided the update to our partners and self-hosted customers. Further, the vulnerability is addressed in the listed patches and hot fixes.
INFO
Published Date :
Oct. 29, 2024, 4:15 p.m.
Last Modified :
Nov. 27, 2024, 7:31 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 4.0 | CRITICAL | [email protected] |
Public PoC/Exploit Available at Github
CVE-2024-8923 has a 1 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-8923.
| URL | Resource |
|---|---|
| https://support.servicenow.com/kb?id=kb_article_view&sysparm_article=KB1706070 | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-8923 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-8923
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Comprehensive cybersecurity research notes, methodologies, and reference collection. This collection contains detailed notes for vulnerability research, penetration testing, exploit development, and security analysis.
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-8923 vulnerability anywhere in the article.

-
Daily CyberSecurity
AI Identity Theft: Critical ServiceNow Flaw (CVE-2025-12420) Allows Unauthenticated Impersonation
A critical vulnerability has been uncovered in the ServiceNow AI Platform, potentially allowing unauthenticated attackers to masquerade as legitimate users. With a severity score of 9.3 out of 10, the ... Read more

-
Cybersecurity News
Raspberry Robin’s Stealth Tactics: USB Infections, Exploits, and Advanced Obfuscation Unveiled
Raspberry Robin, also known as Roshtyak, stands out as a highly advanced malicious downloader. Discovered in 2021, it has gained notoriety for its use of infected USB drives and sophisticated techniqu ... Read more

-
Cybersecurity News
WorkflowKit Race Vulnerability (CVE-2024-27821): Researcher Reveals Exploit that Let Malicious Apps Hijack Shortcuts
Security researcher Snoolie K has published an in-depth analysis of a significant security flaw in WorkflowKit, which has been assigned CVE-2024-27821. This vulnerability, dubbed the “WorkflowKit Race ... Read more

-
Cybersecurity News
Ghostscript Update Patches Six Critical Vulnerabilities: Code Execution, Buffer Overflow, and Path Traversal Risks
Popular document rendering engine Ghostscript has released a critical security update addressing multiple vulnerabilities, some of which could lead to remote code execution.Ghostscript, a widely used ... Read more
-
TheCyberThrone
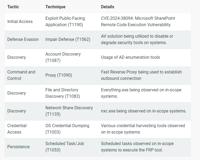
Microsoft Sharepoint Server CVE-2024-38094 Exploited
Threat actors have exploited a vulnerability in Microsoft SharePoint Server, identified as CVE-2024-38094, allowing them to gain complete domain access and compromise critical systems. The Rapid7 inci ... Read more

-
TheCyberThrone
WordPress Plugin LiteSpeed Cache Flaw CVE-2024-50550
Security researcher has identified a vulnerability in the LiteSpeed Cache plugin that could compromise WordPress sites with its unauthenticated privilege escalation capabilities.The vulnerability trac ... Read more

-
TheCyberThrone
The CyberThrone Most Exploited Vulnerabilities Top 10 – October 2024
Welcome to TheCyberThrone most exploited vulnerabilities review. This review is for the month of October 2024CVE-2024-21762: Fortinet FortiOS: Out-of-bounds WriteCVSS 3.1 score : 9.8 CISA KEV : Y ... Read more
The following table lists the changes that have been made to the
CVE-2024-8923 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Reanalysis by [email protected]
Nov. 27, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H Removed CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed CPE Configuration OR *cpe:2.3:a:servicenow:servicenow:vancouver:-:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_2_hotfix1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4_hotfix_1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4_hotfix_1b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_5:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_6:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_1b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_2a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_2b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_8:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:ptach_7:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:-:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_1_hotfix_2a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_3:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:xanadu:-:*:*:*:*:*:* OR *cpe:2.3:a:servicenow:servicenow:xanadu:early_availability:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:xanadu:early_availability_hotfix_1:*:*:*:*:*:* Added CPE Configuration OR *cpe:2.3:a:servicenow:servicenow:vancouver:-:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:early_availability:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:early_availability_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:early_availability_hotfix_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_1_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_2_hotfix1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_2_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_2_hotfix_1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_2_hotfix_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_2_hotfix_3:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_3:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_3_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_3_hotfix_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_3_hotfix_3:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_3_hotfix_4:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4_hotfix_1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4_hotfix_1b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4_hotfix_2b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_5:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_5_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_6:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_6_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_6_hotfix_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotfix_1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotfix_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotfix_2a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotfix_2b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotfix_3a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotfix_3b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotfix_4:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_1b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_2a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_2b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_8:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_8_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_8_hotfix_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_8_hotfix_3:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_8_hotfix_4:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_8_hotfix_5:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_9:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_9_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_9_hotfix_2:*:*:*:*:*:* Added CPE Configuration OR *cpe:2.3:a:servicenow:servicenow:washington_dc:-:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:early_availability:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:early_availability_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_1_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_1_hotfix_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_1_hotfix_2a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_1_hotfix_2b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_1_hotfix_3b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_2_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_2_hotfix_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_3:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_3_hotfix_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_3_hotfix_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_3_hotfix_3:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_4:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_4_hotfix_1:*:*:*:*:*:* -
Initial Analysis by [email protected]
Nov. 07, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://support.servicenow.com/kb?id=kb_article_view&sysparm_article=KB1706070 No Types Assigned https://support.servicenow.com/kb?id=kb_article_view&sysparm_article=KB1706070 Vendor Advisory Added CWE NIST CWE-94 Added CPE Configuration OR *cpe:2.3:a:servicenow:servicenow:vancouver:-:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_2_hotfix1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4_hotfix_1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_4_hotfix_1b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_5:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_6:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_1a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_1b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_2a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_7_hotifix_2b:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:patch_8:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:vancouver:ptach_7:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:-:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_1:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_1_hotfix_2a:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_2:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:washington_dc:patch_3:*:*:*:*:*:* *cpe:2.3:a:servicenow:servicenow:xanadu:-:*:*:*:*:*:* -
CVE Modified by [email protected]
Oct. 29, 2024
Action Type Old Value New Value Added CWE ServiceNow CWE-94 -
CVE Received by [email protected]
Oct. 29, 2024
Action Type Old Value New Value Added Description ServiceNow has addressed an input validation vulnerability that was identified in the Now Platform. This vulnerability could enable an unauthenticated user to remotely execute code within the context of the Now Platform. ServiceNow deployed an update to hosted instances and ServiceNow provided the update to our partners and self-hosted customers. Further, the vulnerability is addressed in the listed patches and hot fixes. Added Reference ServiceNow https://support.servicenow.com/kb?id=kb_article_view&sysparm_article=KB1706070 [No types assigned] Added CVSS V3.1 ServiceNow AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Added CVSS V4.0 ServiceNow CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:X/R:X/V:X/RE:X/U:X