CVE-2024-9264
Grafana SQL Expressions allow for remote code execution
Description
The SQL Expressions experimental feature of Grafana allows for the evaluation of `duckdb` queries containing user input. These queries are insufficiently sanitized before being passed to `duckdb`, leading to a command injection and local file inclusion vulnerability. Any user with the VIEWER or higher permission is capable of executing this attack. The `duckdb` binary must be present in Grafana's $PATH for this attack to function; by default, this binary is not installed in Grafana distributions.
INFO
Published Date :
Oct. 18, 2024, 4:15 a.m.
Last Modified :
March 14, 2025, 10:15 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 4.0 | CRITICAL | [email protected] |
Solution
- Update Grafana to a patched version.
- Refer to vendor advisory for specific instructions.
Public PoC/Exploit Available at Github
CVE-2024-9264 has a 54 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2024-9264.
| URL | Resource |
|---|---|
| https://grafana.com/security/security-advisories/cve-2024-9264/ | Vendor Advisory |
| https://security.netapp.com/advisory/ntap-20250314-0007/ |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2024-9264 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2024-9264
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Grafana CVE Scanner
cve cve-scanning grafana grafana-dashboard grafana-plugin python python3 tools
Python
Writeups and solve scripts for Midnight Flag CTF 2026 — 15 challenges across crypto, forensics, misc, OSINT, pwn, reversing, web, and web3
Python
Grafana scanner with all public CVEs that I collected in one script to make grafana testing easier
Python
None
Grafana SQL Expressions → DuckDB LFI (CVE-2024-9264)
Dockerfile Shell
An high-performance security scanner designed for comprehensive vulnerability assessment of monitoring and logging infrastructure stacks with concurrent processing and extensive CVE coverage.
Python
My collection of Nuclei templates
exploit hacking nuclei nuclei-templates recon
Grafana image with DuckDB binary present vulnerable to exploit CVE-2024-9264
Dockerfile
walkthrough for machines
Authenticated RCE in Grafana (v11.0) via SQL Expressions - PoC Exploit
Shell
Write-up for Planning machine from Hack The Box
Grafana RCE
Python
None
Python
备份的漏洞库,3月开始我们来维护
None
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2024-9264 vulnerability anywhere in the article.

-
Cybersecurity News
CVE-2023-28461 (CVSS 9.8): Critical Array Networks Vulnerability Added to KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added CVE-2023-28461, a high-severity security flaw impacting Array Networks AG and vxAG ArrayOS, to its Known Exploited Vulnerabil ... Read more

-
Cybersecurity News
7 Android & Pixel Vulnerabilities Exposed: Researcher Publishes PoC Exploits
Image: GoogleOversecured, a renowned cybersecurity firm, has unearthed seven vulnerabilities within the Android operating system and Google Pixel devices. Two of these vulnerabilities specifically end ... Read more

-
Cybersecurity News
Critical VMware vCenter Server Flaws Under Active Attack: CISA Issues Urgent Warning
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent warning regarding two critical vulnerabilities in VMware vCenter Server that are currently being exploited in the ... Read more

-
Cybersecurity News
CVE-2024-31141: Apache Kafka Vulnerability Exposes User Data to Potential Attackers
A newly discovered vulnerability in Apache Kafka, the popular open-source event streaming platform, could allow attackers to gain unauthorized access to sensitive information. The vulnerability, track ... Read more

-
Cybersecurity News
PXA Stealer: New Malware Targets Governments and Education Across Europe and Asia
Infection Chain | Image: Cisco TalosCisco Talos recently identified a sophisticated cyber campaign targeting sensitive information in government and educational sectors across Europe and Asia. Operate ... Read more

-
Cybersecurity News
2023’s Most Exploited Vulnerabilities: A Global Cybersecurity Advisory
In a joint cybersecurity advisory, the top cybersecurity agencies from the United States, Australia, Canada, New Zealand, and the United Kingdom have identified the most exploited vulnerabilities of 2 ... Read more

-
TheCyberThrone
The CyberThrone most exploited vulnerabilities review – November 9, 2024
Welcome to TheCyberThrone most exploited vulnerabilities review. This review is for the weeks ending Saturday, November 9, 2024.Grafana LabsThe vulnerability tracked as CVE-2024-9264 with a 9.4-severi ... Read more

-
Cybersecurity News
ZoneMinder’s CVE-2024-51482: A 10/10 Severity Vulnerability Exposes SQL Databases
A newly identified security vulnerability in ZoneMinder, a popular open-source video surveillance platform, could allow attackers to gain control over SQL databases, compromising data confidentiality ... Read more

-
The Cyber Express
New Vulnerabilities in Fortinet, SonicWall, and Grafana Pose Significant Risks
Cyble Research and Intelligence Labs (CRIL) has identified new IT vulnerabilities affecting Fortinet, SonicWall, Grafana Labs, and CyberPanel, among others. The report for the week of October 23-29 hi ... Read more

-
Cybersecurity News
MediaTek Security Bulletin Highlights High Severity Vulnerabilities in Mobile Chipsets
MediaTek, a leading global fabless semiconductor company, has issued a security bulletin disclosing multiple vulnerabilities across its chipset product line. These vulnerabilities impact a range of de ... Read more
-
The Cyber Express
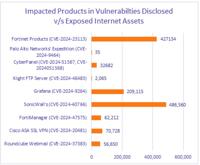
Nearly 1 Million Vulnerable Fortinet, SonicWall Devices Exposed to the Web
Nearly 1 million Fortinet and SonicWall devices with actively exploited vulnerabilities are exposed on the internet, according to Cyble’s weekly vulnerability report published today. The report also l ... Read more

-
Cybersecurity News
Patch Now! Grafana Hit by 9.9 Severity RCE Vulnerability (CVE-2024-9264)
A critical security vulnerability (CVE-2024-9264) has been discovered in Grafana, the popular open-source platform for monitoring and observability. This vulnerability, with a CVSS v3.1 score of 9.9, ... Read more
The following table lists the changes that have been made to the
CVE-2024-9264 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Mar. 14, 2025
Action Type Old Value New Value Added Reference https://security.netapp.com/advisory/ntap-20250314-0007/ -
Initial Analysis by [email protected]
Nov. 01, 2024
Action Type Old Value New Value Added CVSS V3.1 NIST AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Changed Reference Type https://grafana.com/security/security-advisories/cve-2024-9264/ No Types Assigned https://grafana.com/security/security-advisories/cve-2024-9264/ Vendor Advisory Added CWE NIST CWE-77 Added CPE Configuration OR *cpe:2.3:a:grafana:grafana:11.0.0:*:*:*:*:*:*:* -
CVE Received by [email protected]
Oct. 18, 2024
Action Type Old Value New Value Added Description The SQL Expressions experimental feature of Grafana allows for the evaluation of `duckdb` queries containing user input. These queries are insufficiently sanitized before being passed to `duckdb`, leading to a command injection and local file inclusion vulnerability. Any user with the VIEWER or higher permission is capable of executing this attack. The `duckdb` binary must be present in Grafana's $PATH for this attack to function; by default, this binary is not installed in Grafana distributions. Added Reference Grafana Labs https://grafana.com/security/security-advisories/cve-2024-9264/ [No types assigned] Added CWE Grafana Labs CWE-94 Added CVSS V3.1 Grafana Labs AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H Added CVSS V4.0 Grafana Labs CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:H/VI:H/VA:H/SC:H/SI:H/SA:H/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:X/R:X/V:X/RE:X/U:X