CVE-2025-10035
Fortra GoAnywhere MFT Deserialization of Untrusted Data Vulnerability - [Actively Exploited]
Description
A deserialization vulnerability in the License Servlet of Fortra's GoAnywhere MFT allows an actor with a validly forged license response signature to deserialize an arbitrary actor-controlled object, possibly leading to command injection.
INFO
Published Date :
Sept. 18, 2025, 10:15 p.m.
Last Modified :
Oct. 24, 2025, 1:44 p.m.
Remotely Exploit :
Yes !
Source :
df4dee71-de3a-4139-9588-11b62fe6c0ff
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Fortra GoAnywhere MFT contains a deserialization of untrusted data vulnerability allows an actor with a validly forged license response signature to deserialize an arbitrary actor-controlled object, possibly leading to command injection.
Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable.
Known Detected Feb 26, 2026
https://www.fortra.com/security/advisories/product-security/fi-2025-012 ; https://nvd.nist.gov/vuln/detail/CVE-2025-10035
Affected Products
The following products are affected by CVE-2025-10035
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | df4dee71-de3a-4139-9588-11b62fe6c0ff | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Validate license response signatures.
- Sanitize all user-supplied input.
- Update to a patched version.
- Restrict access to the License Servlet.
Public PoC/Exploit Available at Github
CVE-2025-10035 has a 15 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-10035.
| URL | Resource |
|---|---|
| https://www.fortra.com/security/advisories/product-security/fi-2025-012 | Vendor Advisory |
| https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-10035 | US Government Resource |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-10035 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-10035
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Mirror of https://github.com/nomi-sec/PoC-in-GitHub
Nuclei scripts created by @rxerium for zero days / actively exploited vulnerabilities.
kev nuclei zero-day vkev
Vulnerability detection scripts for the Goanywhere MFT product.
fortra nuclei vulnerability-management
CVE-2025-10035
For educational and cybersecurity purposes.
dll-injection fileless-malware ioc living-off-the-land malware-analysis mitre-attack cve-research pentesting dns-attacks ransomware-dectection threat-detection vibe-coding wsl2 windows
YARA HTML C++ Batchfile
CVE-2025-10035_GoAnywhere Get RCE
Python
A deserialization vulnerability in the License Servlet of Fortra's GoAnywhere MFT allows an actor with a validly forged license response signature to deserialize an arbitrary actor-controlled object, possibly leading to command injection.
Python
Detection for CVE-2025-10035
goanywhere mft nuclei poc
None
监控Github最新网络安全相关的仓库...
cve cybersecurity github spider
Shell Python Nix
A collection of Vulnerability Research and Reverse Engineering writeups.
A list of all of my starred repos, automated using Github Actions 🌟
github-actions stars
Ostorlab KEV: One-command to detect most remotely known exploitable vulnerabilities. Sourced from CISA KEV, Google's Tsunami, Ostorlab's Asteroid and Bug Bounty programs.
cisa-kev vulnerability 0day cisa exploits
Satori CI - Playbook Marketplace
security security-audit security-automation security-medium security-scan security-scanner security-tools security-vulnerability testing testing-framework testing-tool testing-tools
📡 PoC auto collect from GitHub. ⚠️ Be careful Malware.
security cve exploit poc vulnerability
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-10035 vulnerability anywhere in the article.

-
CybersecurityNews
Microsoft Warns Storm-1175 Exploits Web-Facing Assets 0-Day Flaws in Medusa Ransomware Attacks
A new ransomware campaign is putting organizations on high alert. A financially motivated threat group known as Storm-1175 has been running fast-paced attacks targeting vulnerable, internet-facing sys ... Read more

-
The Hacker News
China-Linked Storm-1175 Exploits Zero-Days to Rapidly Deploy Medusa Ransomware
A China-based threat actor known for deploying Medusa ransomware has been linked to the weaponization of a combination of zero-day and N-day vulnerabilities to orchestrate "high-velocity" attacks and ... Read more

-
Daily CyberSecurity
CVE-2026-24936: Critical ASUSTOR Flaw (CVSS 9.5) Allows Remote System Takeover
A severe vulnerability has been discovered in ASUSTOR ADM (ASUSTOR Data Master), the operating system that powers ASUSTOR’s network-attached storage (NAS) devices. Tracked as CVE-2026-24936, this flaw ... Read more

-
Daily CyberSecurity
Hard-Coded Keys and Open Doors: Critical Flaws Found in PrismX AP Controllers
A trio of security vulnerabilities has been discovered in Browan Communications’ PrismX MX100 AP Controller, the most severe of which essentially leaves the digital keys under the doormat. In a new vu ... Read more

-
Daily CyberSecurity
CVE-2025-52694 (CVSS 10): Critical Advantech SQL Injection Exposes IoT Devices
The Cyber Security Agency of Singapore (CSA) has issued a high-priority alert regarding a devastating vulnerability in Advantech’s IoT product line. The flaw, tracked as CVE-2025-52694, carries the ma ... Read more

-
CybersecurityNews
CISA Expands KEV Catalog with 1,484 New Vulnerabilities as Active Exploitation Surges 20% in 2025
The United States Cybersecurity and Infrastructure Security Agency (CISA) has significantly expanded its Known Exploited Vulnerabilities (KEV) Catalog to 1,484 vulnerabilities as of December 2025, mar ... Read more

-
Daily CyberSecurity
Eaton UPS Software Flaws Expose Systems to High-Risk Code Execution
Power management giant Eaton dropped a critical security advisory on Christmas Eve, warning users of its UPS Companion (EUC) software to update immediately. The alert details two significant vulnerabi ... Read more
-
TheCyberThrone
When Silence Broke Security: Zero-Days in 2025
PrefaceIn 2025, zero-day vulnerabilities emerged as one of the most decisive factors shaping the global cyber-threat landscape. Attackers increasingly shifted from noisy, opportunistic exploits to pre ... Read more

-
CybersecurityNews
Ransomware Attack 2025 Recap – From Critical Data Extortion to Operational Disruption
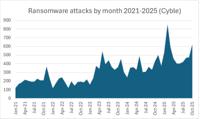
The ransomware landscape in 2025 has reached new heights, evolving from a cybersecurity issue into a strategic threat to national security and global economic stability. This year saw a 34%-50% surge ... Read more

-
The Cyber Express
Cyble Global Cybersecurity Report 2025: 6,000 Ransomware Attacks Mark a 50% Surge
2025 will be remembered as the year cyber threats reached a breaking point. With nearly 6,000 ransomware incidents, more than 6,000 data breaches, and over 3,000 sales of compromised corporate access, ... Read more
-
The Cyber Express
Ransomware Attacks Soared 30% in October
Ransomware attacks soared 30% in October to the second-highest total on record, Cyble reported today. The 623 ransomware attacks recorded in October were second only to February 2025’s record attacks, ... Read more

-
hackread.com
Medusa Ransomware Leaks 834 GB of Comcast Data After $1.2M Demand
The Medusa ransomware group has leaked 186.36 GB of compressed data it claimed to have stolen from Comcast Corporation, a global media and technology company. According to Hackread.com’s earlier repor ... Read more

-
The Hacker News
From Detection to Patch: Fortra Reveals Full Timeline of CVE-2025-10035 Exploitation
Oct 10, 2025Ravie LakshmananVulnerability / Network Security Fortra on Thursday revealed the results of its investigation into CVE-2025-10035, a critical security flaw in GoAnywhere Managed File Tra ... Read more

-
Hackread - Latest Cybersecurity, Hacking News, Tech, AI & Crypto
Medusa Ransomware Exploiting GoAnywhere MFT Flaw, Confirms Microsoft
A CVSS 10.0 deserialization vulnerability in Fortra’s GoAnywhere Managed File Transfer (MFT) solution is now being actively exploited by the Medusa ransomware group, according to a latest update from ... Read more

-
The Cyber Express
Attackers Deployed Medusa Ransomware via GoAnywhere MFT Zero-Day
Cybercriminals exploited a critical deserialization flaw in Fortra’s GoAnywhere Managed File Transfer (MFT) tool—tracked as CVE-2025-10035—to drop Medusa ransomware, Microsoft disclosed Monday. The ca ... Read more

-
CybersecurityNews
GoAnywhere 0-Day RCE Vulnerability Exploited in the Wild to Deploy Medusa Ransomware
A critical deserialization flaw in GoAnywhere MFT’s License Servlet, tracked as CVE-2025-10035, has already been weaponized by the Storm-1175 group to execute the Medusa ransomware. The vulnerability ... Read more

-
The Hacker News
Microsoft Links Storm-1175 to GoAnywhere Exploit Deploying Medusa Ransomware
Oct 07, 2025Ravie LakshmananVulnerability / Cloud Security Microsoft on Monday attributed a threat actor it tracks as Storm-1175 to the exploitation of a critical security flaw in Fortra GoAnywhere ... Read more

-
security.nl
Microsoft: kritiek GoAnywhere MFT-lek gebruikt bij ransomware-aanvallen
Een kritieke kwetsbaarheid in Fortra GoAnywhere MFT is gebruikt bij ransomware-aanvallen en op het moment van de aanvallen was er nog geen beveiligingsupdate voor het probleem beschikbaar. Dat laat Mi ... Read more

-
Daily CyberSecurity
Critical Flaw CVE-2025-59159 (CVSS 9.7) in SillyTavern Allows Full Remote Control of Local AI Instances
The developers of SillyTavern, a popular locally hosted interface for large language models (LLMs) and AI tools, have issued a security advisory warning users of a critical web interface vulnerability ... Read more

-
Daily CyberSecurity
Critical RCE (CVE-2025-10035) in GoAnywhere MFT Used by Medusa Ransomware Group
Microsoft Threat Intelligence has issued a warning following the discovery of active exploitation of a newly disclosed critical vulnerability in GoAnywhere Managed File Transfer (MFT) software by the ... Read more
The following table lists the changes that have been made to the
CVE-2025-10035 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Oct. 24, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-10035 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-10035 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-10035 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-10035 -
Reanalysis by [email protected]
Oct. 16, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H Added CWE CWE-77 Added CWE CWE-502 -
Initial Analysis by [email protected]
Sep. 30, 2025
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:a:fortra:goanywhere_managed_file_transfer:*:*:*:*:*:*:*:* versions up to (excluding) 7.6.3 *cpe:2.3:a:fortra:goanywhere_managed_file_transfer:*:*:*:*:*:*:*:* versions from (including) 7.7.0 up to (excluding) 7.8.4 Added Reference Type Fortra: https://www.fortra.com/security/advisories/product-security/fi-2025-012 Types: Vendor Advisory -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Sep. 30, 2025
Action Type Old Value New Value Added Date Added 2025-09-29 Added Due Date 2025-10-20 Added Required Action Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable. Added Vulnerability Name Fortra GoAnywhere MFT Deserialization of Untrusted Data Vulnerability -
CVE Modified by df4dee71-de3a-4139-9588-11b62fe6c0ff
Sep. 18, 2025
Action Type Old Value New Value Added Reference https://www.fortra.com/security/advisories/product-security/fi-2025-012 Removed Reference https://www.fortra.com/security/advisories/product-security/fi-2025-011 -
New CVE Received by df4dee71-de3a-4139-9588-11b62fe6c0ff
Sep. 18, 2025
Action Type Old Value New Value Added Description A deserialization vulnerability in the License Servlet of Fortra's GoAnywhere MFT allows an actor with a validly forged license response signature to deserialize an arbitrary actor-controlled object, possibly leading to command injection. Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H Added CWE CWE-77 Added CWE CWE-502 Added Reference https://www.fortra.com/security/advisories/product-security/fi-2025-011