CVE-2025-10729
Use-after-free vulnerability in Qt SVG qsvghandler.cpp allows denial of service via crafted SVG
Description
The module will parse a <pattern> node which is not a child of a structural node. The node will be deleted after creation but might be accessed later leading to a use after free.
INFO
Published Date :
Oct. 3, 2025, 4:16 p.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
No
Source :
a59d8014-47c4-4630-ab43-e1b13cbe58e3
Affected Products
The following products are affected by CVE-2025-10729
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
No affected product recoded yet
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 4.0 | CRITICAL | a59d8014-47c4-4630-ab43-e1b13cbe58e3 | ||||
| CVSS 4.0 | CRITICAL | a59d8014-47c4-4630-ab43-e1b13cbe58e3 |
Solution
- Ensure nodes are not accessed after deletion.
- Review memory allocation and deallocation logic.
- Implement robust error handling for node access.
- Apply vendor patches if available.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-10729.
| URL | Resource |
|---|---|
| https://codereview.qt-project.org/c/qt/qtsvg/+/676473 |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-10729 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-10729
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-10729 vulnerability anywhere in the article.
-
Daily CyberSecurity
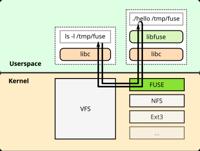
Critical libfuse io_uring Vulnerabilities Threaten Linux and Kubernetes Infrastructure
The FUSE (Filesystem in Userspace) project, a staple of the Linux ecosystem that allows non-privileged users to create their own file systems, is facing a dual-threat. Researchers have identified two ... Read more
The following table lists the changes that have been made to the
CVE-2025-10729 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
New CVE Received by a59d8014-47c4-4630-ab43-e1b13cbe58e3
Oct. 03, 2025
Action Type Old Value New Value Added Description The module will parse a <pattern> node which is not a child of a structural node. The node will be deleted after creation but might be accessed later leading to a use after free. Added CVSS V4.0 AV:L/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:H/SI:H/SA:H/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:P/AU:X/R:X/V:X/RE:H/U:Red Added CWE CWE-416 Added Reference https://codereview.qt-project.org/c/qt/qtsvg/+/676473