CVE-2025-20654
Aruba Networks Wlan Remote Code Execution (Out-of-Bounds Write)
Description
In wlan service, there is a possible out of bounds write due to an incorrect bounds check. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation. Patch ID: WCNCR00406897; Issue ID: MSV-2875.
INFO
Published Date :
April 7, 2025, 4:15 a.m.
Last Modified :
April 9, 2025, 3:46 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2025-20654
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Apply the latest security patches for the WLAN service.
- Update the WLAN service firmware.
- Verify the security configuration of the WLAN service.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-20654.
| URL | Resource |
|---|---|
| https://corp.mediatek.com/product-security-bulletin/April-2025 | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-20654 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-20654
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-20654 vulnerability anywhere in the article.

-
Daily CyberSecurity
Kibana Code Injection Vulnerability: Prototype Pollution Threat (CVE-2024-12556)
A newly disclosed vulnerability in Kibana, the popular open-source data visualization front-end for Elasticsearch, has been rated CVSS 8.7 due to its potential to allow remote code injection under spe ... Read more

-
Daily CyberSecurity
Chrome Update Fixes High-Severity “Use After Free” Vulnerability
The Chrome Stable channel has been updated to version 135.0.7049.84/.85 for Windows and Mac, and to 135.0.7049.84 for Linux. This update will be rolling out to users over the coming days and weeks. Th ... Read more

-
Daily CyberSecurity
Microsoft April 2025 Patch Tuesday: Critical Security Updates and Zero-Day Exploits
This April, Microsoft’s Patch Tuesday release addresses a significant number of vulnerabilities, highlighting the ever-present need for robust cybersecurity practices. The tech giant rolled out fixes ... Read more

-
Daily CyberSecurity
Apache mod_auth_openidc Vulnerability Exposes Protected Content
In a recently published security advisory, OpenIDC has revealed a vulnerability in mod_auth_openidc, the widely used OpenID Connect module for the Apache HTTP server. The flaw, tracked as CVE-2025-314 ... Read more

-
Daily CyberSecurity
Fortinet: Critical Unverified Password Change Flaw in FortiSwitch
Fortinet has released a security advisory addressing a critical vulnerability in FortiSwitch products. The vulnerability, identified as CVE-2024-48887 (CVSS 9.3), could allow attackers to gain unautho ... Read more

-
Daily CyberSecurity
Siemens Industrial Edge: Critical Authentication Flaw (CVE-2024-54092)
Siemens has issued security advisories SSA-634640 and SSA-819629 to address a weak authentication vulnerability affecting its Industrial Edge Devices and Industrial Edge Device Kit. The vulnerability, ... Read more
-
Daily CyberSecurity
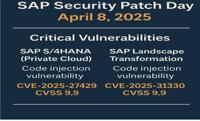
SAP April 2025 Patch Day: Critical Code Injection Risks
The SAP Security Patch Day on April 8, 2025, brought a wave of critical security updates, with a total of 18 new Security Notes and 2 updates to previously released notes. Among the fixes, several add ... Read more

-
Daily CyberSecurity
TVT DVRs Under Siege: Massive Exploitation Attempts Expose Critical Flaw
A significant surge in malicious cyber activity has been detected, raising alarms for organizations utilizing TVT NVMS9000 DVRs. GreyNoise intelligence reports “a significant spike 3 times that of typ ... Read more

-
Daily CyberSecurity
Top 5 VPN Vulnerabilities in 2025
I. Executive SummaryThe reliance on Virtual Private Networks (VPNs) has grown significantly as organizations embrace remote work and individuals seek enhanced online privacy and security. However, thi ... Read more

-
Daily CyberSecurity
WhatsApp for Windows Spoofing Vulnerability: Execute Code Risk (CVE-2025-30401)
A security advisory from Facebook details a spoofing vulnerability in WhatsApp for Windows, highlighting a potential risk where malicious actors could trick users into executing arbitrary code. The vu ... Read more

-
Daily CyberSecurity
CVE-2025-27520: Critical BentoML Flaw Allows Full Remote Code Execution, Exploit Available
A severe security vulnerability has been identified in BentoML, a Python library used for building online serving systems optimized for AI applications and model inference. The vulnerability, tracked ... Read more

-
Daily CyberSecurity
PoC Released for CVE-2025-3155: Yelp Flaw Can Expose SSH Keys on Ubuntu Systems
A security vulnerability, identified as CVE-2025-3155, has been discovered in Yelp, the GNOME user help application that comes pre-installed on Ubuntu desktop. The vulnerability involves the way Yelp ... Read more

-
Cyber Security News
MediaTek Security Update – Patch for Vulnerabilities Affecting Smartphone, Tablet, & other Devices
MediaTek has released a critical security update addressing multiple vulnerabilities in its chipsets, with one critical flaw that could potentially allow attackers to execute malicious code remotely o ... Read more

-
Daily CyberSecurity
MediaTek’s April 2025 Security Bulletin: Critical WLAN Vulnerability Exposes Chipsets
MediaTek has released its April 2025 Product Security Bulletin, detailing a range of security vulnerabilities affecting its various chipsets. The bulletin covers vulnerabilities in chipsets used in sm ... Read more
The following table lists the changes that have been made to the
CVE-2025-20654 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Apr. 09, 2025
Action Type Old Value New Value Added CWE CWE-787 Added CPE Configuration AND OR *cpe:2.3:a:mediatek:software_development_kit:*:*:*:*:*:*:*:* versions up to (including) 7.4.0.1 OR *cpe:2.3:h:mediatek:mt7622:-:*:*:*:*:*:*:* *cpe:2.3:h:mediatek:mt7915:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:a:mediatek:software_development_kit:*:*:*:*:*:*:*:* versions up to (including) 7.6.7.0 OR *cpe:2.3:h:mediatek:mt7915:-:*:*:*:*:*:*:* *cpe:2.3:h:mediatek:mt7916:-:*:*:*:*:*:*:* *cpe:2.3:h:mediatek:mt7986:-:*:*:*:*:*:*:* *cpe:2.3:h:mediatek:mt7981:-:*:*:*:*:*:*:* Added CPE Configuration AND OR *cpe:2.3:o:openwrt:openwrt:19.07.0:-:*:*:*:*:*:* *cpe:2.3:o:openwrt:openwrt:21.02.0:-:*:*:*:*:*:* OR *cpe:2.3:h:mediatek:mt6890:-:*:*:*:*:*:*:* Added Reference Type MediaTek, Inc.: https://corp.mediatek.com/product-security-bulletin/April-2025 Types: Vendor Advisory -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Apr. 07, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H -
New CVE Received by [email protected]
Apr. 07, 2025
Action Type Old Value New Value Added Description In wlan service, there is a possible out of bounds write due to an incorrect bounds check. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation. Patch ID: WCNCR00406897; Issue ID: MSV-2875. Added CWE CWE-787 Added Reference https://corp.mediatek.com/product-security-bulletin/April-2025