CVE-2025-27429
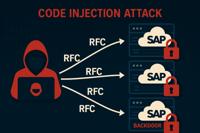
Code Injection Vulnerability in SAP S/4HANA (Private Cloud or On-Premise)
Description
SAP S/4HANA allows an attacker with user privileges to exploit a vulnerability in the function module exposed via RFC. This flaw enables the injection of arbitrary ABAP code into the system, bypassing essential authorization checks. This vulnerability effectively functions as a backdoor, creating the risk of full system compromise, undermining the confidentiality, integrity and availability of the system.
INFO
Published Date :
April 8, 2025, 8:15 a.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2025-27429
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
No affected product recoded yet
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Apply relevant SAP security notes immediately.
- Restrict access to exposed RFC function modules.
- Review and strengthen RFC authorization controls.
- Monitor system logs for suspicious RFC activity.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-27429.
| URL | Resource |
|---|---|
| https://me.sap.com/notes/3581961 | |
| https://url.sap/sapsecuritypatchday |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-27429 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-27429
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-27429 vulnerability anywhere in the article.

-
TheCyberThrone
CVE-2025-42957: Critical SAP S/4HANA Code Injection Vulnerability – Exploited in the Wild
September 7, 2025Executive SummaryA newly disclosed and actively exploited vulnerability, CVE-2025-42957, has sent shockwaves through the SAP ecosystem. This critical flaw (CVSS 9.9) affects all SAP S ... Read more

-
TheCyberThrone
SAP Patch Tuesday August 2025
August 13, 2025SAP’s August 2025 Patch Tuesday addresses 25–26 security issues with an emphasis on several critical vulnerabilities involving code injection and insecure deserialization. The updates p ... Read more

-
The Register
Microsoft's Patch Tuesday baker's dozen: 12 critical bugs plus a SharePoint RCE
Microsoft’s August Patch Tuesday flaw-fixing festival addresses 111 problems in its products, a dozen of which are deemed critical, and one moderate-severity flaw that is listed as being publicly know ... Read more

-
CybersecurityNews
SAP Security Patch Day – 15 Vulnerabilities Patched including 3 Critical Injection Vulnerabilities
SAP released a comprehensive security update on August 12th, 2025, addressing 15 new vulnerabilities across its enterprise software portfolio, including three critical code injection flaws that pose s ... Read more
-
Daily CyberSecurity
SAP Patch Day August 2025: Critical Code Injection Flaws Threaten Core ERP Systems
Today, 2025, SAP released 15 new Security Notes and 4 updates to previously issued advisories as part of its monthly Security Patch Day. While the update addresses a broad range of issues, several cri ... Read more

-
BleepingComputer
SAP fixes suspected Netweaver zero-day exploited in attacks
SAP has released out-of-band emergency NetWeaver updates to fix a suspected remote code execution (RCE) zero-day flaw actively exploited to hijack servers. The vulnerability, tracked under CVE-2025-31 ... Read more

-
Cyber Security News
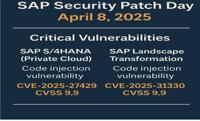
SAP April 2025 Security Update : Critical Code Injection Vulnerabilities Patched
SAP announced its latest Security Patch Day, unveiling 18 new Security Notes alongside updates to two previously released advisories. This comprehensive update focuses on addressing multiple vulnerabi ... Read more
-
Daily CyberSecurity
SAP April 2025 Patch Day: Critical Code Injection Risks
The SAP Security Patch Day on April 8, 2025, brought a wave of critical security updates, with a total of 18 new Security Notes and 2 updates to previously released notes. Among the fixes, several add ... Read more
The following table lists the changes that have been made to the
CVE-2025-27429 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
New CVE Received by [email protected]
Apr. 08, 2025
Action Type Old Value New Value Added Description SAP S/4HANA allows an attacker with user privileges to exploit a vulnerability in the function module exposed via RFC. This flaw enables the injection of arbitrary ABAP code into the system, bypassing essential authorization checks. This vulnerability effectively functions as a backdoor, creating the risk of full system compromise, undermining the confidentiality, integrity and availability of the system. Added CVSS V3.1 AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H Added CWE CWE-94 Added Reference https://me.sap.com/notes/3581961 Added Reference https://url.sap/sapsecuritypatchday