CVE-2025-29969
MS-EVEN RPC Remote Code Execution Vulnerability
Description
Time-of-check time-of-use (toctou) race condition in Windows Fundamentals allows an authorized attacker to execute code over a network.
INFO
Published Date :
May 13, 2025, 5:15 p.m.
Last Modified :
May 19, 2025, 2:20 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2025-29969
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] |
Solution
- Update Windows Fundamentals to the latest version.
- Apply vendor security patches promptly.
- Monitor system logs for suspicious activity.
Public PoC/Exploit Available at Github
CVE-2025-29969 has a 2 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-29969.
| URL | Resource |
|---|---|
| https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-29969 | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-29969 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-29969
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Exploitation of CVE-2025-29969
Python
EPSS & VEDAS Score Aggregator for CVEs
cve vulnerability exploit epss vedas exploit-maturity
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-29969 vulnerability anywhere in the article.

-
Daily CyberSecurity
Critical 9.4 CVSS RCE Flaws in n8n Turn Workflows into Backdoors
Security researchers have disclosed two critical vulnerabilities in n8n, the popular fair-code workflow automation platform used by technical teams to bridge the gap between low-code speed and full-co ... Read more

-
Daily CyberSecurity
Critical 9.8 CVSS Flaw in Pharos Mosaic Controllers Grants Root Access to Unauthenticated Attackers
A security advisory has been issued by CISA regarding a critical vulnerability discovered in Pharos Controls’ Mosaic Show Controller firmware. The flaw, which carries a severity CVSS score of 9.8, cou ... Read more

-
Daily CyberSecurity
Critical 9.3 CVSS Auth Bypass and XSS Flaws Hit MantisBT
Security researchers have identified a trio of significant vulnerabilities within MantisBT, the popular open-source issue tracking system used by teams worldwide for project collaboration. The flaws r ... Read more

-
Daily CyberSecurity
Proof-of-Concept Released: Public Exploit Details for Windows Error Reporting LPE (CVE-2026-20817)
Researcher Clément Labro published a deep-dive analysis and a functional Proof-of-Concept (PoC) exploit for a critical security flaw in the Windows Error Reporting (WER) service. The vulnerability, tr ... Read more

-
Daily CyberSecurity
BIND 9 Security Alert: ISC Releases Patches for Trio of Vulnerabilities
The Internet Systems Consortium (ISC) has issued an important security advisory for BIND 9, the world’s most widely used DNS software. The update addresses three distinct vulnerabilities that could al ... Read more

-
Daily CyberSecurity
High-Severity strongSwan Flaw Enables Remote VPN Gateway Crashes
A high-severity security vulnerability has been uncovered in strongSwan, the widely used open-source IPsec-based VPN solution. The flaw, tracked as CVE-2026-25075 with a CVSSv4 score of 8.7, resides i ... Read more

-
Daily CyberSecurity
Zabbix API Vulnerability: High-Severity SQL Injection Threatens Network Monitoring Security
A high-severity security vulnerability has been identified in the Zabbix API, a popular open-source monitoring solution used by enterprises worldwide to track the status of network services, servers, ... Read more

-
Daily CyberSecurity
Hackers Actively Exploiting 9.8 Critical RCE Flaw in Kali Forms WordPress Plugin
The attackers begin actively exploiting a critical vulnerability in Kali Forms, a popular drag-and-drop form builder WordPress plugin. With over 10,000 active installations, the plugin is a favorite f ... Read more

-
Daily CyberSecurity
DHCP Down: High-Severity Stack Overflow Flaw Threatens to Paralyze Kea Networks
The Internet Systems Consortium (ISC) has issued a high-severity security advisory regarding a critical vulnerability affecting the Kea DHCP suite. The flaw, tracked as CVE-2026-3608 (CVSS 7.5), could ... Read more

-
Daily CyberSecurity
Critical RCE Flaw in PTC Windchill and FlexPLM Puts Product Data at Risk
PTC has issued a high-priority security advisory regarding a critical vulnerability affecting its Windchill and FlexPLM product lifecycle management suites. The flaw, tracked as CVE-2026-4681 (CVSS 10 ... Read more

-
Daily CyberSecurity
Cisco Alert: Public Vulnerabilities in IOS XE Risk Service Denial and Privilege Escalation
Cisco has issued important security advisories for two distinct vulnerabilities within its Cisco IOS XE Software, targeting the Command Line Interface (CLI) and the Lobby Ambassador management API. Th ... Read more

-
Daily CyberSecurity
NAS Under Siege: Critical 9.8 CVSS Bug in Synology Telnet Opens the Door to Total Hijack
Synology has issued an urgent security update for its DiskStation Manager (DSM) operating system to address a critical vulnerability in the Telnet service. The flaw, tracked as CVE-2026-32746, could a ... Read more

-
Daily CyberSecurity
NVIDIA Patches Critical RCE and DoS Flaws Across ML Frameworks
NVIDIA has released a series of critical software updates to address high-severity vulnerabilities across its core AI and machine learning frameworks. The patches cover Megatron-LM, Triton Inference S ... Read more

-
Daily CyberSecurity
Public Flaws in Cisco IOx Allow Unauthenticated Log Injection and Admin XSS
Cisco has issued security advisories regarding two vulnerabilities in its Cisco IOx application hosting environment for Cisco IOS XE Software. The flaws, which include a stored cross-site scripting (X ... Read more
-
Daily CyberSecurity
The Backup Backdoor: How a Simple File Edit Grants Full SYSTEM Control in IDrive for Windows
A critical local privilege escalation vulnerability has been discovered in the IDrive Cloud Backup Client for Windows, potentially allowing low-privileged users to seize full control of an affected ma ... Read more

-
Daily CyberSecurity
PoC Exploit Publicly Disclosed: Windows ‘libarchive’ Flaw Leaks NetNTLMv2 Hashes
Security researchers Len Sadowski and Oğuz Bektaş have publicly pulled back the curtain on a vulnerability within Windows’ implementation of libarchive. The flaw, tracked as CVE-2025-59284, demonstrat ... Read more

-
Daily CyberSecurity
PoC Exploit Publicly Disclosed: ‘RegPwn’ Flaw Grants SYSTEM Access via Windows Accessibility
A newly discovered vulnerability, dubbed RegPwn, has pulled back the curtain on a significant security gap in the Windows Accessibility Infrastructure. Tracked as CVE-2026-24291, this local elevation ... Read more

-
Daily CyberSecurity
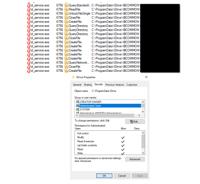
PoC Exploit Disclosed: Researcher Unveils Windows MS-EVEN RPC Vulnerability
The SafeBreach Labs research team has pulled back the curtain on a significant security weakness in the Windows MS-EVEN RPC service, revealing how even low-privileged credentials can be used to compro ... Read more
The following table lists the changes that have been made to the
CVE-2025-29969 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
May. 19, 2025
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:o:microsoft:windows_server_2008:r2:sp1:*:*:*:*:x64:* *cpe:2.3:o:microsoft:windows_server_2012:r2:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2008:-:sp2:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_server_2012:-:*:*:*:*:*:*:* *cpe:2.3:o:microsoft:windows_10_1809:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.17763.7314 *cpe:2.3:o:microsoft:windows_10_1809:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.17763.7314 *cpe:2.3:o:microsoft:windows_10_1507:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.10240.21014 *cpe:2.3:o:microsoft:windows_10_1507:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.10240.21014 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.14393.8066 *cpe:2.3:o:microsoft:windows_10_1607:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.14393.8066 *cpe:2.3:o:microsoft:windows_10_21h2:*:*:*:*:*:*:arm64:* versions up to (excluding) 10.0.19044.5854 *cpe:2.3:o:microsoft:windows_10_21h2:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.19044.5854 *cpe:2.3:o:microsoft:windows_10_21h2:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.19044.5854 *cpe:2.3:o:microsoft:windows_server_2016:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.14393.8066 *cpe:2.3:o:microsoft:windows_server_2019:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.17763.7314 *cpe:2.3:o:microsoft:windows_server_2022:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.20348.3692 *cpe:2.3:o:microsoft:windows_server_2022_23h2:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.25398.1611 *cpe:2.3:o:microsoft:windows_server_2025:*:*:*:*:*:*:*:* versions up to (excluding) 10.0.26100.4061 *cpe:2.3:o:microsoft:windows_10_22h2:*:*:*:*:*:*:arm64:* versions up to (excluding) 10.0.19045.5854 *cpe:2.3:o:microsoft:windows_10_22h2:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.19045.5854 *cpe:2.3:o:microsoft:windows_10_22h2:*:*:*:*:*:*:x86:* versions up to (excluding) 10.0.19045.5854 *cpe:2.3:o:microsoft:windows_11_22h2:*:*:*:*:*:*:arm64:* versions up to (excluding) 10.0.22621.5335 *cpe:2.3:o:microsoft:windows_11_22h2:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.22621.5335 *cpe:2.3:o:microsoft:windows_11_23h2:*:*:*:*:*:*:arm64:* versions up to (excluding) 10.0.22631.5335 *cpe:2.3:o:microsoft:windows_11_23h2:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.22631.5335 *cpe:2.3:o:microsoft:windows_11_24h2:*:*:*:*:*:*:arm64:* versions up to (excluding) 10.0.26100.4061 *cpe:2.3:o:microsoft:windows_11_24h2:*:*:*:*:*:*:x64:* versions up to (excluding) 10.0.26100.4061 Added Reference Type Microsoft Corporation: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-29969 Types: Vendor Advisory -
New CVE Received by [email protected]
May. 13, 2025
Action Type Old Value New Value Added Description Time-of-check time-of-use (toctou) race condition in Windows Fundamentals allows an authorized attacker to execute code over a network. Added CVSS V3.1 AV:N/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H Added CWE CWE-367 Added Reference https://msrc.microsoft.com/update-guide/vulnerability/CVE-2025-29969