CVE-2025-31115
XZ has a heap-use-after-free bug in threaded .xz decoder
Description
XZ Utils provide a general-purpose data-compression library plus command-line tools. In XZ Utils 5.3.3alpha to 5.8.0, the multithreaded .xz decoder in liblzma has a bug where invalid input can at least result in a crash. The effects include heap use after free and writing to an address based on the null pointer plus an offset. Applications and libraries that use the lzma_stream_decoder_mt function are affected. The bug has been fixed in XZ Utils 5.8.1, and the fix has been committed to the v5.4, v5.6, v5.8, and master branches in the xz Git repository. No new release packages will be made from the old stable branches, but a standalone patch is available that applies to all affected releases.
INFO
Published Date :
April 3, 2025, 5:15 p.m.
Last Modified :
May 12, 2026, 1:16 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 4.0 | HIGH | [email protected] |
Solution
- Update XZ Utils to version 5.8.1.
- Apply the standalone patch if updating is not possible.
Public PoC/Exploit Available at Github
CVE-2025-31115 has a 5 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-31115.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-31115 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-31115
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Security issues CVE-2025-31115: Threaded .xz decoder frees memory too early CVE-2024-47611: Argument injection on Windows CVE-2024-3094: liblzma backdoor CVE-2022-1271: xzgrep filename handling CVE-2020-22916: A bogus CVE
Batchfile Shell JavaScript Makefile C CMake
Multi-threaded LZMA/XZ compression for Python
compression python xz-utils
Python Cython
None
Dockerfile Python HCL
Standalone Container Security Tests
None
Makefile Smarty Dockerfile Shell HCL JavaScript Go HTML TypeScript CSS
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-31115 vulnerability anywhere in the article.

-
Daily CyberSecurity
The Pixel 9 Zero-Click Exploit Chain That Breaks the Kernel
One need not even open a missive or engage the “play” interface for a device to commence the background parsing of an attachment, all in the service of providing a seamless transcription or indexing f ... Read more

-
Daily CyberSecurity
Critical XZ Backdoor Still Lurks in Docker Images, Posing Supply Chain Risk
The backdoor vulnerability in XZ-Utils first came to light in March 2024, and had it not been discovered in time, it could have posed a grave security threat to the entire technology sector. Yet, even ... Read more

-
Daily CyberSecurity
Fortinet: Critical Unverified Password Change Flaw in FortiSwitch
Fortinet has released a security advisory addressing a critical vulnerability in FortiSwitch products. The vulnerability, identified as CVE-2024-48887 (CVSS 9.3), could allow attackers to gain unautho ... Read more

-
Daily CyberSecurity
Siemens Industrial Edge: Critical Authentication Flaw (CVE-2024-54092)
Siemens has issued security advisories SSA-634640 and SSA-819629 to address a weak authentication vulnerability affecting its Industrial Edge Devices and Industrial Edge Device Kit. The vulnerability, ... Read more
-
Daily CyberSecurity
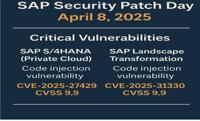
SAP April 2025 Patch Day: Critical Code Injection Risks
The SAP Security Patch Day on April 8, 2025, brought a wave of critical security updates, with a total of 18 new Security Notes and 2 updates to previously released notes. Among the fixes, several add ... Read more

-
Daily CyberSecurity
TVT DVRs Under Siege: Massive Exploitation Attempts Expose Critical Flaw
A significant surge in malicious cyber activity has been detected, raising alarms for organizations utilizing TVT NVMS9000 DVRs. GreyNoise intelligence reports “a significant spike 3 times that of typ ... Read more

-
Daily CyberSecurity
Top 5 VPN Vulnerabilities in 2025
I. Executive SummaryThe reliance on Virtual Private Networks (VPNs) has grown significantly as organizations embrace remote work and individuals seek enhanced online privacy and security. However, thi ... Read more

-
Daily CyberSecurity
WhatsApp for Windows Spoofing Vulnerability: Execute Code Risk (CVE-2025-30401)
A security advisory from Facebook details a spoofing vulnerability in WhatsApp for Windows, highlighting a potential risk where malicious actors could trick users into executing arbitrary code. The vu ... Read more

-
Daily CyberSecurity
CVE-2025-27520: Critical BentoML Flaw Allows Full Remote Code Execution, Exploit Available
A severe security vulnerability has been identified in BentoML, a Python library used for building online serving systems optimized for AI applications and model inference. The vulnerability, tracked ... Read more

-
Daily CyberSecurity
PoC Released for CVE-2025-3155: Yelp Flaw Can Expose SSH Keys on Ubuntu Systems
A security vulnerability, identified as CVE-2025-3155, has been discovered in Yelp, the GNOME user help application that comes pre-installed on Ubuntu desktop. The vulnerability involves the way Yelp ... Read more

-
Daily CyberSecurity
MediaTek’s April 2025 Security Bulletin: Critical WLAN Vulnerability Exposes Chipsets
MediaTek has released its April 2025 Product Security Bulletin, detailing a range of security vulnerabilities affecting its various chipsets. The bulletin covers vulnerabilities in chipsets used in sm ... Read more
-
Daily CyberSecurity
Linux Kernel Vulnerability Exposes Local Systems to Privilege Escalation, PoC Published
A security researcher has recently disclosed technical details and proof-of-concept (PoC) exploit code for a vulnerability in the Linux kernel’s Performance Events system component. This flaw, identif ... Read more

-
Daily CyberSecurity
MinIO Urgently Patches High-Severity Incomplete Signature Validation Vulnerability
MinIO, a high-performance object storage server compatible with Amazon S3, has released a patch to address a critical security vulnerability. The vulnerability, tracked as CVE-2025-31489, involves inc ... Read more

-
Daily CyberSecurity
Bitdefender GravityZone Console Hit by Critical PHP Deserialization Vulnerability
A critical-severity vulnerability has been discovered in the Bitdefender GravityZone Console, posing a significant risk to affected systems. The flaw, tracked as CVE-2025-2244 (CVSSv4 9.5), is an inse ... Read more
The following table lists the changes that have been made to the
CVE-2025-31115 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by 0b142b55-0307-4c5a-b3c9-f314f3fb7c5e
May. 12, 2026
Action Type Old Value New Value Added Reference https://cert-portal.siemens.com/productcert/html/ssa-082556.html -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Apr. 03, 2025
Action Type Old Value New Value Added Reference http://www.openwall.com/lists/oss-security/2025/04/03/3 -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Apr. 03, 2025
Action Type Old Value New Value Added Reference http://www.openwall.com/lists/oss-security/2025/04/03/1 Added Reference http://www.openwall.com/lists/oss-security/2025/04/03/2 -
New CVE Received by [email protected]
Apr. 03, 2025
Action Type Old Value New Value Added Description XZ Utils provide a general-purpose data-compression library plus command-line tools. In XZ Utils 5.3.3alpha to 5.8.0, the multithreaded .xz decoder in liblzma has a bug where invalid input can at least result in a crash. The effects include heap use after free and writing to an address based on the null pointer plus an offset. Applications and libraries that use the lzma_stream_decoder_mt function are affected. The bug has been fixed in XZ Utils 5.8.1, and the fix has been committed to the v5.4, v5.6, v5.8, and master branches in the xz Git repository. No new release packages will be made from the old stable branches, but a standalone patch is available that applies to all affected releases. Added CVSS V4.0 AV:N/AC:L/AT:N/PR:N/UI:N/VC:N/VI:N/VA:H/SC:N/SI:N/SA:N/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:X/R:X/V:X/RE:X/U:X Added CWE CWE-476 Added CWE CWE-416 Added CWE CWE-366 Added CWE CWE-826 Added Reference https://github.com/tukaani-project/xz/commit/d5a2ffe41bb77b918a8c96084885d4dbe4bf6480 Added Reference https://github.com/tukaani-project/xz/security/advisories/GHSA-6cc8-p5mm-29w2 Added Reference https://tukaani.org/xz/xz-cve-2025-31115.patch