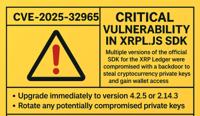
CVE-2025-32965
Compromised xrpl.js versions 4.2.1, 4.2.2, 4.2.3, 4.2.4, and 2.14.2
Description
xrpl.js is a JavaScript/TypeScript API for interacting with the XRP Ledger in Node.js and the browser. Versions 4.2.1, 4.2.2, 4.2.3, and 4.2.4 of xrpl.js were compromised and contained malicious code designed to exfiltrate private keys. Version 2.14.2 is also malicious, though it is less likely to lead to exploitation as it is not compatible with other 2.x versions. Anyone who used one of these versions should stop immediately and rotate any private keys or secrets used with affected systems. Users of xrpl.js should pgrade to version 4.2.5 or 2.14.3 to receive a patch. To secure funds, think carefully about whether any keys may have been compromised by this supply chain attack, and mitigate by sending funds to secure wallets, and/or rotating keys. If any account's master key is potentially compromised, disable the key.
INFO
Published Date :
April 22, 2025, 9:15 p.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
Affected Products
The following products are affected by CVE-2025-32965
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
No affected product recoded yet
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 4.0 | CRITICAL | [email protected] |
Solution
- Update xrpl.js to version 4.2.5 or 2.14.3.
- Rotate any compromised private keys or secrets.
- Migrate funds to secure wallets if keys were exposed.
- Disable potentially compromised master keys.
Public PoC/Exploit Available at Github
CVE-2025-32965 has a 3 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-32965.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-32965 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-32965
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Mirror of https://github.com/nomi-sec/PoC-in-GitHub
CVE Kodu: CVE-2025-32965 Zafiyet Türü: Supply Chain Attack (CWE-506: Embedded Malicious Code) Hedef: xrpl.js kütüphanesinin 4.2.1–4.2.4 ve 2.14.2 versiyonları Etki: Kullanıcının cüzdan seed/secret verisinin saldırgana gönderilmesi
Dockerfile JavaScript
None
HTML Python Shell
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-32965 vulnerability anywhere in the article.

-
Daily CyberSecurity
“G_Wagon” Malware Hides in Fake NPM UI Library to Steal Cloud Keys
It looked like just another UI library. “ansi-universal-ui” promised to be a “lightweight, modular UI component system for modern web applications.” But behind the professional description and version ... Read more

-
Daily CyberSecurity
High-Severity SonicWall SSLVPN Vulnerability Allows Firewall Crashing
SonicWall has disclosed a vulnerability affecting its SonicOS SSLVPN Virtual Office interface, which, if exploited, could allow remote attackers to crash firewall appliances. Tracked as CVE-2025-32818 ... Read more
-
Daily CyberSecurity
CVE-2025-32965: Backdoor in xrpl.js SDK Puts Crypto Wallets at Risk
Aikido Intel has issued an urgent alert after detecting a backdoor in multiple versions of xrpl.js, the official SDK for the XRP Ledger, marking one of the most severe supply chain attacks to hit the ... Read more

-
Daily CyberSecurity
CVE-2025-34028: Critical RCE Flaw in Commvault Command Center Scores CVSS 10
Commvault has disclosed a critical vulnerability affecting its Command Center, identified as CVE-2025-34028, with the maximum CVSS score of 10.0. The flaw allows unauthenticated remote attackers to ex ... Read more

-
The Register
Ripple NPM supply chain attack hunts for private keys
Many versions of the Ripple ledger (XRPL) official NPM package are compromised with malware injected to steal cryptocurrency. The NPM package, xrpl, is a JavaScript/TypeScript library that devs use to ... Read more
The following table lists the changes that have been made to the
CVE-2025-32965 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
New CVE Received by [email protected]
Apr. 22, 2025
Action Type Old Value New Value Added Description xrpl.js is a JavaScript/TypeScript API for interacting with the XRP Ledger in Node.js and the browser. Versions 4.2.1, 4.2.2, 4.2.3, and 4.2.4 of xrpl.js were compromised and contained malicious code designed to exfiltrate private keys. Version 2.14.2 is also malicious, though it is less likely to lead to exploitation as it is not compatible with other 2.x versions. Anyone who used one of these versions should stop immediately and rotate any private keys or secrets used with affected systems. Users of xrpl.js should pgrade to version 4.2.5 or 2.14.3 to receive a patch. To secure funds, think carefully about whether any keys may have been compromised by this supply chain attack, and mitigate by sending funds to secure wallets, and/or rotating keys. If any account's master key is potentially compromised, disable the key. Added CVSS V4.0 AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:X/R:X/V:X/RE:X/U:X Added CWE CWE-506 Added Reference https://github.com/XRPLF/xrpl.js/security/advisories/GHSA-33qr-m49q-rxfx Added Reference https://www.aikido.dev/blog/xrp-supplychain-attack-official-npm-package-infected-with-crypto-stealing-backdoor Added Reference https://xrpl.org/docs/tutorials/how-tos/manage-account-settings/assign-a-regular-key-pair Added Reference https://xrpl.org/docs/tutorials/how-tos/manage-account-settings/disable-master-key-pair