CVE-2025-38352
Linux Kernel Time-of-Check Time-of-Use (TOCTOU) Race Condition Vulnerability - [Actively Exploited]
Description
In the Linux kernel, the following vulnerability has been resolved: posix-cpu-timers: fix race between handle_posix_cpu_timers() and posix_cpu_timer_del() If an exiting non-autoreaping task has already passed exit_notify() and calls handle_posix_cpu_timers() from IRQ, it can be reaped by its parent or debugger right after unlock_task_sighand(). If a concurrent posix_cpu_timer_del() runs at that moment, it won't be able to detect timer->it.cpu.firing != 0: cpu_timer_task_rcu() and/or lock_task_sighand() will fail. Add the tsk->exit_state check into run_posix_cpu_timers() to fix this. This fix is not needed if CONFIG_POSIX_CPU_TIMERS_TASK_WORK=y, because exit_task_work() is called before exit_notify(). But the check still makes sense, task_work_add(&tsk->posix_cputimers_work.work) will fail anyway in this case.
INFO
Published Date :
July 22, 2025, 8:15 a.m.
Last Modified :
Jan. 8, 2026, 4:28 p.m.
Remotely Exploit :
No
Source :
416baaa9-dc9f-4396-8d5f-8c081fb06d67
CISA KEV (Known Exploited Vulnerabilities)
For the benefit of the cybersecurity community and network defenders—and to help every organization better manage vulnerabilities and keep pace with threat activity—CISA maintains the authoritative source of vulnerabilities that have been exploited in the wild.
Linux kernel contains a time-of-check time-of-use (TOCTOU) race condition vulnerability that has a high impact on confidentiality, integrity, and availability.
Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable.
Unknown
This vulnerability affects a common open-source component, third-party library, or a protocol used by different products. Please check with specific vendors for information on patching status. For more information, please see: https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux.git/commit/?id=2c72fe18cc5f9f1750f5bc148cf1c94c29e106ff ; https://source.android.com/docs/security/bulletin/2025-09-01 ; https://nvd.nist.gov/vuln/detail/CVE-2025-38352
Affected Products
The following products are affected by CVE-2025-38352
vulnerability.
Even if cvefeed.io is aware of the exact versions of the
products
that
are
affected, the information is not represented in the table below.
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Update the Linux kernel to the latest version.
- Apply the provided patch for the POSIX CPU timers.
- Ensure CONFIG_POSIX_CPU_TIMERS_TASK_WORK is handled correctly.
Public PoC/Exploit Available at Github
CVE-2025-38352 has a 17 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-38352.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-38352 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-38352
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Multi-architecture Linux privilege escalation toolkit with 18 pre-built and runtime-compilable exploits. Auto-detects kernel version, filters patched exploits, tries each until root.
ctf cybersecurity exploit gtfobins kernel-exploit linux penetration-testing privilege-escalation security
Makefile Shell C Go
The most comprehensive Android & iOS security reference — tools, research papers, exploit techniques, platform internals, CTFs, and more. Built for security engineers.
The official Sentinel Edition v7.11 - Hypervisor Detection & Kernel Memory Audit Suite for Honor Magic V2. Investigating CVE-2025-38352 and EL2 RKP defenses.
Python C
Ubuntu VPS Maximum Security Hardening Toolkit — 20 modules, one command
Shell Go Template
None
Makefile Shell C
Mirror of https://github.com/nomi-sec/PoC-in-GitHub
🚀 Exploit the Android/Linux kernel using CVE-2025-38352 with Chronomaly, designed for vulnerable v5.10.x kernels without needing specific offsets.
None
agentic-ai agents ai-framework ai-frameworks authentication exploit gluon large-language-models machine-learning neural-network pocketflow research retrieval-augmented-generation scada workflow workflow-orchestration zdi
Makefile C
Android kernel exploit for CVE-2025-38352, previously exploited in-the-wild. Targets vulnerable Linux kernels v5.10.x.
Makefile C Shell
This is a proof of concept for CVE-2025-38352, a vulnerability in the Linux kernel's POSIX CPU timers implementation. The September 2025 Android Bulletin mentions that this vulnerability has been used in limited, targeted exploitation in the wild.
Makefile C
A Rust-based Linux application that generates endpoint telemetry aligned with MITRE ATT&CK techniques for security analytics, research, and training environments.
Rust Shell Nix
None
Shell
🛠️ Exploit the CVE-2025-38352 vulnerability in the Android/Linux kernel with Chronomaly, designed for efficient use on vulnerable v5.10.x kernels.
analytics-tool dashboard data-analysis data-visualization development event-logging integration-tool open-source productivity project-management software-engineering task-automation time-series time-tracking user-experience
Makefile C Shell
Cybersecurity oriented awesome list
awesome awesome-list cybersecurity exploitation reverse-engineering
awesome game security [Welcome to PR]
game awesome cheat anticheat windows debug antidebug engine security anti driver kernel hack gamehack system android game-development blockchain ethereum
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-38352 vulnerability anywhere in the article.

-
The Cyber Express
Google Chrome Update Fixes 21 Flaws, Warns of Actively Exploited Vulnerability
Google has released a Stable Channel Update for Chrome, addressing 21 security vulnerabilities, including a high-profile code smuggling vulnerability that is actively being exploited in the wild. The ... Read more
-
Google Cloud
Look What You Made Us Patch: 2025 Zero-Days in Review
Written by: Casey Charrier, James Sadowski, Zander Work, Clement Lecigne, Benoît Sevens, Fred Plan Executive Summary Google Threat Intelligence Group (GTIG) tracked 90 zero-day vulnerabilities exploit ... Read more

-
Daily CyberSecurity
Security Alert: Android March 2026 Update Targets Actively Exploited Zero-Day
Google has released its most substantial security update in years, addressing a total of 129 vulnerabilities in the March 2026 Android Security Bulletin. The massive patch arrives amid warnings that a ... Read more
-
Daily CyberSecurity
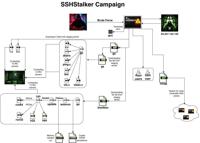
Back to the Future: SSHStalker Botnet Revives 2009 Tactics to Hijack Linux Servers
Image: Flare A previously undocumented Linux botnet has been discovered prowling the internet, using a mix of ancient tactics and modern automation to compromise servers. Dubbed SSHStalker by research ... Read more

-
CybersecurityNews
PoC Exploit Released for Android/Linux Kernel Vulnerability CVE-2025-38352
A proof-of-concept (PoC) exploit for CVE-2025-38352, a critical race condition vulnerability in the Linux kernel, has been publicly released on GitHub. The vulnerability, discovered earlier this year, ... Read more
-
Daily CyberSecurity
Zero-Day Chronomaly Exploit Grants Root Access to Vulnerable Linux Kernels
Cybersecurity researcher farazsth98 has presented new findings related to an exploited security issue in Linux kernel flaw that could be abused by an attacker to privilege escalation. The vulnerabilit ... Read more

-
Daily CyberSecurity
PoC Exploit Released for CVE-2025-55680 – Windows Cloud Files Mini Filter Driver Elevation of Privilege Flaw
Security researchers from TyphoonPWN, the Windows PE Winner team, in collaboration with SSD Secure Disclosure, have uncovered a time-of-check to time-of-use (TOCTOU) race condition affecting the Windo ... Read more

-
The Cyber Express
Unity Warns Developers of Security Vulnerability Affecting Games on Android, Windows, and Linux Platforms
A recently disclosed security vulnerability in Unity has prompted security updates and, in some cases, game removals across platforms like Steam. The issue affects Unity versions 2017.1 and later, spa ... Read more

-
Daily CyberSecurity
Researcher Details Zero-Day Linux/Android Kernel Flaw (CVE-2025-38352)
Security researcher StreyPaws has published an in-depth analysis of CVE-2025-38352, a Time-of-Check to Time-of-Use (TOCTOU) race condition in the Linux/Android kernel’s POSIX CPU Timer subsystem. The ... Read more

-
Daily CyberSecurity
CVE-2025-9242: Critical WatchGuard Flaw Allows Remote Code Execution
WatchGuard has issued a security advisory addressing a critical vulnerability in its Fireware OS, tracked as CVE-2025-9242 with a CVSS v4 score of 9.3. The flaw resides in the iked process and could a ... Read more

-
Daily CyberSecurity
Kubernetes C# Client Flaw Exposes API to MITM Attacks (CVE-2025-9708)
A newly disclosed vulnerability in the Kubernetes C# client has been assigned CVE-2025-9708 with a CVSS score of 6.8 (Medium severity). The flaw stems from improper certificate validation in custom Ce ... Read more

-
Daily CyberSecurity
KSMBDrain (CVE-2025-38501): Linux Kernel Flaw Allows Remote DoS Attacks, PoC Available
A newly disclosed vulnerability in the Linux kernel’s KSMBD subsystem has been assigned CVE-2025-38501, allowing remote attackers to exhaust server resources and cause denial-of-service (DoS) conditio ... Read more

-
Daily CyberSecurity
AISURU Botnet: From Record-Breaking DDoS to Residential Proxy Empire
The AISURU botnet, first disclosed by XLab in 2024, has rapidly become one of the most dangerous forces in the DDoS landscape. In 2025 alone, it was linked to multiple record-breaking attacks, includi ... Read more

-
Daily CyberSecurity
Chrome’s New Preloading is a Game-Changer
Google has long experimented with prerendering technology in Chrome to accelerate page loading by rendering content in advance so that pages would open instantly upon a click. However, this approach o ... Read more

-
Daily CyberSecurity
China Accuses NVIDIA of Anti-Monopoly Violations
China’s State Administration for Market Regulation (SAMR) issued a statement today declaring that NVIDIA’s $6.9 billion acquisition of Mellanox in 2019 violated both the Anti-Monopoly Law of the Peopl ... Read more

-
Daily CyberSecurity
Apple Ends iCloud Support for Older Devices
According to Apple’s newly published support documentation, devices running iOS 10 or macOS 10.12 no longer meet the minimum system requirements for iCloud services. As a result, these systems will lo ... Read more

-
Daily CyberSecurity
CVE-2025-5821: Critical Authentication Bypass in WordPress Case Theme User Plugin Exploited in the Wild
Hackers are exploiting a critical authentication bypass vulnerability in the Case Theme User plugin, a WordPress plugin with an estimated 12,000 active installations. This plugin is bundled in multipl ... Read more

-
Daily CyberSecurity
PoC Published: Linux Kernel 0-Click RCE Vulnerability Found in ksmbd
Image: BitsByWill In a recent deep-dive analysis, security researcher BitsByWill examined two critical Linux kernel vulnerabilities—CVE-2023-52440 and CVE-2023-4130—both impacting ksmbd, the in-kernel ... Read more

-
The Cyber Express
CVE-2025-58434: Critical FlowiseAI Flaw Enables Full Account Takeover
A severe security vulnerability has been discovered in FlowiseAI, an open-source AI workflow automation tool, exposing users to the risk of complete account compromise. Tracked as CVE-2025-58434, this ... Read more

-
Daily CyberSecurity
OpenAI’s New Grove Incubator Is Building the Next Generation of AI Startups
OpenAI recently unveiled its internal incubation initiative, OpenAI Grove. Unlike traditional startup accelerators or incubator programs, Grove emphasizes engaging with potential founders before their ... Read more
The following table lists the changes that have been made to the
CVE-2025-38352 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Modified Analysis by [email protected]
Jan. 08, 2026
Action Type Old Value New Value Added Reference Type CISA-ADP: https://github.com/farazsth98/chronomaly Types: Exploit -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Jan. 07, 2026
Action Type Old Value New Value Added Reference https://github.com/farazsth98/chronomaly -
Modified Analysis by [email protected]
Nov. 04, 2025
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:o:debian:debian_linux:11.0:*:*:*:*:*:*:* Added Reference Type CVE: https://lists.debian.org/debian-lts-announce/2025/10/msg00007.html Types: Mailing List, Third Party Advisory Added Reference Type CVE: https://lists.debian.org/debian-lts-announce/2025/10/msg00008.html Types: Mailing List, Third Party Advisory -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 03, 2025
Action Type Old Value New Value Added Reference https://lists.debian.org/debian-lts-announce/2025/10/msg00007.html Added Reference https://lists.debian.org/debian-lts-announce/2025/10/msg00008.html -
Modified Analysis by [email protected]
Oct. 24, 2025
Action Type Old Value New Value Added Reference Type CISA-ADP: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-38352 Types: US Government Resource -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-38352 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Removed Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-38352 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Oct. 21, 2025
Action Type Old Value New Value Added Reference https://www.cisa.gov/known-exploited-vulnerabilities-catalog?field_cve=CVE-2025-38352 -
Initial Analysis by [email protected]
Sep. 05, 2025
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 2.6.36 up to (excluding) 5.4.295 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 5.11 up to (excluding) 5.15.186 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 5.16 up to (excluding) 6.1.142 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 5.5 up to (excluding) 5.10.239 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 6.13 up to (excluding) 6.15.3 *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 6.7 up to (excluding) 6.12.34 *cpe:2.3:o:linux:linux_kernel:6.16:rc1:*:*:*:*:*:* *cpe:2.3:o:linux:linux_kernel:*:*:*:*:*:*:*:* versions from (including) 6.2 up to (excluding) 6.6.94 Added Reference Type kernel.org: https://git.kernel.org/stable/c/2c72fe18cc5f9f1750f5bc148cf1c94c29e106ff Types: Patch Added Reference Type kernel.org: https://git.kernel.org/stable/c/2f3daa04a9328220de46f0d5c919a6c0073a9f0b Types: Patch Added Reference Type kernel.org: https://git.kernel.org/stable/c/460188bc042a3f40f72d34b9f7fc6ee66b0b757b Types: Patch Added Reference Type kernel.org: https://git.kernel.org/stable/c/764a7a5dfda23f69919441f2eac2a83e7db6e5bb Types: Patch Added Reference Type kernel.org: https://git.kernel.org/stable/c/78a4b8e3795b31dae58762bc091bb0f4f74a2200 Types: Patch Added Reference Type kernel.org: https://git.kernel.org/stable/c/c076635b3a42771ace7d276de8dc3bc76ee2ba1b Types: Patch Added Reference Type kernel.org: https://git.kernel.org/stable/c/c29d5318708e67ac13c1b6fc1007d179fb65b4d7 Types: Patch Added Reference Type kernel.org: https://git.kernel.org/stable/c/f90fff1e152dedf52b932240ebbd670d83330eca Types: Patch -
CVE CISA KEV Update by 9119a7d8-5eab-497f-8521-727c672e3725
Sep. 05, 2025
Action Type Old Value New Value Added Date Added 2025-09-04 Added Due Date 2025-09-25 Added Required Action Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable. Added Vulnerability Name Linux Kernel Time-of-Check Time-of-Use (TOCTOU) Race Condition Vulnerability -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Sep. 02, 2025
Action Type Old Value New Value Added CWE CWE-367 Removed CWE CWE-362 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Sep. 02, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:L/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H Added CWE CWE-362 -
New CVE Received by 416baaa9-dc9f-4396-8d5f-8c081fb06d67
Jul. 22, 2025
Action Type Old Value New Value Added Description In the Linux kernel, the following vulnerability has been resolved: posix-cpu-timers: fix race between handle_posix_cpu_timers() and posix_cpu_timer_del() If an exiting non-autoreaping task has already passed exit_notify() and calls handle_posix_cpu_timers() from IRQ, it can be reaped by its parent or debugger right after unlock_task_sighand(). If a concurrent posix_cpu_timer_del() runs at that moment, it won't be able to detect timer->it.cpu.firing != 0: cpu_timer_task_rcu() and/or lock_task_sighand() will fail. Add the tsk->exit_state check into run_posix_cpu_timers() to fix this. This fix is not needed if CONFIG_POSIX_CPU_TIMERS_TASK_WORK=y, because exit_task_work() is called before exit_notify(). But the check still makes sense, task_work_add(&tsk->posix_cputimers_work.work) will fail anyway in this case. Added Reference https://git.kernel.org/stable/c/2c72fe18cc5f9f1750f5bc148cf1c94c29e106ff Added Reference https://git.kernel.org/stable/c/2f3daa04a9328220de46f0d5c919a6c0073a9f0b Added Reference https://git.kernel.org/stable/c/460188bc042a3f40f72d34b9f7fc6ee66b0b757b Added Reference https://git.kernel.org/stable/c/764a7a5dfda23f69919441f2eac2a83e7db6e5bb Added Reference https://git.kernel.org/stable/c/78a4b8e3795b31dae58762bc091bb0f4f74a2200 Added Reference https://git.kernel.org/stable/c/c076635b3a42771ace7d276de8dc3bc76ee2ba1b Added Reference https://git.kernel.org/stable/c/c29d5318708e67ac13c1b6fc1007d179fb65b4d7 Added Reference https://git.kernel.org/stable/c/f90fff1e152dedf52b932240ebbd670d83330eca