CVE-2025-4802
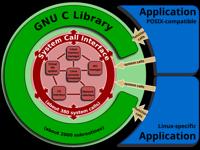
GNU C Library LD_LIBRARY_PATH Path Traversal Vulnerability
Description
Untrusted LD_LIBRARY_PATH environment variable vulnerability in the GNU C Library version 2.27 to 2.38 allows attacker controlled loading of dynamically shared library in statically compiled setuid binaries that call dlopen (including internal dlopen calls after setlocale or calls to NSS functions such as getaddrinfo).
INFO
Published Date :
May 16, 2025, 8:15 p.m.
Last Modified :
Nov. 3, 2025, 8:19 p.m.
Remotely Exploit :
No
Source :
3ff69d7a-14f2-4f67-a097-88dee7810d18
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Update the GNU C Library to a patched version.
- Ensure dynamically linked setuid binaries are secure.
- Review setuid binary configurations for safe dlopen usage.
Public PoC/Exploit Available at Github
CVE-2025-4802 has a 12 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-4802.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-4802 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-4802
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Mirror of https://github.com/nomi-sec/PoC-in-GitHub
Proof of Concept for a statically compiled setuid binary vulnerable to dlopen with LD_LIBRARY_PATH
C
None
Dockerfile Python HTML CSS JavaScript
None
Dockerfile Python HCL
Standalone Container Security Tests
A text book for fuzzing against the sudo binary as a demonstration
Makefile C
None
Dockerfile Python Smarty HTML
None
Dockerfile Python HTML
Flask app with Trivy and Bandit integrated in a CI/CD pipeline for automated security scanning and vulnerability detection.
Dockerfile Python PowerShell Shell C JavaScript CSS Roff
CI/CD Automation Project for Social Media Application (DevOps)
Dockerfile HTML
Run paperless-ngx rootless by default (no SUID)!
Dockerfile Python
📡 PoC auto collect from GitHub. ⚠️ Be careful Malware.
security cve exploit poc vulnerability
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-4802 vulnerability anywhere in the article.
-
Daily CyberSecurity
Decades-Old Flaw & New Heap Corruption: Critical glibc Bugs Revealed
The maintainers of the GNU C Library (glibc), the core library that underpins the vast majority of Linux-based systems, have disclosed details on two security vulnerabilities ranging from high-severit ... Read more
The following table lists the changes that have been made to the
CVE-2025-4802 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Nov. 03, 2025
Action Type Old Value New Value Added Reference https://lists.debian.org/debian-lts-announce/2025/05/msg00033.html -
Initial Analysis by [email protected]
Jun. 17, 2025
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:a:gnu:glibc:*:*:*:*:*:*:*:* versions from (including) 2.27 up to (including) 2.38 Added Reference Type CVE: http://www.openwall.com/lists/oss-security/2025/05/16/7 Types: Mailing List Added Reference Type CVE: http://www.openwall.com/lists/oss-security/2025/05/17/2 Types: Exploit, Mailing List Added Reference Type GNU C Library: https://sourceware.org/bugzilla/show_bug.cgi?id=32976 Types: Issue Tracking Added Reference Type GNU C Library: https://sourceware.org/cgit/glibc/commit/?id=1e18586c5820e329f741d5c710275e165581380e Types: Patch -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
May. 20, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H Removed CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
May. 17, 2025
Action Type Old Value New Value Added Reference http://www.openwall.com/lists/oss-security/2025/05/17/2 -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
May. 17, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H -
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
May. 17, 2025
Action Type Old Value New Value Added Reference http://www.openwall.com/lists/oss-security/2025/05/16/7 -
New CVE Received by 3ff69d7a-14f2-4f67-a097-88dee7810d18
May. 16, 2025
Action Type Old Value New Value Added Description Untrusted LD_LIBRARY_PATH environment variable vulnerability in the GNU C Library version 2.27 to 2.38 allows attacker controlled loading of dynamically shared library in statically compiled setuid binaries that call dlopen (including internal dlopen calls after setlocale or calls to NSS functions such as getaddrinfo). Added CWE CWE-426 Added Reference https://sourceware.org/bugzilla/show_bug.cgi?id=32976 Added Reference https://sourceware.org/cgit/glibc/commit/?id=1e18586c5820e329f741d5c710275e165581380e