CVE-2025-48530
Apache HTTP Server Out-of-Bounds Write Vulnerability
Description
In multiple locations, there is a possible condition that results in OOB accesses due to an incorrect bounds check. This could lead to remote code execution in combination with other bugs, with no additional execution privileges needed. User interaction is not needed for exploitation.
INFO
Published Date :
Sept. 4, 2025, 7:15 p.m.
Last Modified :
Sept. 5, 2025, 7:10 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | 134c704f-9b21-4f2e-91b3-4a467353bcc0 |
Solution
- Implement robust bounds checking for all memory operations.
- Review and validate all array index accesses.
- Apply code changes to fix buffer overflows.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-48530.
| URL | Resource |
|---|---|
| https://source.android.com/security/bulletin/2025-08-01 | Vendor Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-48530 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-48530
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-48530 vulnerability anywhere in the article.

-
The Hacker News
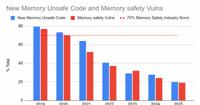
Rust Adoption Drives Android Memory Safety Bugs Below 20% for First Time
Nov 17, 2025Ravie LakshmananVulnerability / Mobile Security Google has disclosed that the company's continued adoption of the Rust programming language in Android has resulted in the number of memor ... Read more

-
security.nl
Google: Hoeveelheid memory safety-kwetsbaarheden met een factor duizend gedaald door omarming Rust
Google meldt dat door het omarmen van Rust voor Android-beveiliging de hoeveelheid memory safety-kwetsbaarheden met een factor duizend is gedaald ten opzichte van de C en C++ code van Android. Daarnaa ... Read more

-
The Cyber Express
Android Reports Major Drop in Memory Bugs as Rust Adoption Accelerates
Android has shared new insights into how the platform’s long-term shift toward Rust is reshaping both security and software development. The new data reflects a decisive move toward memory safety, and ... Read more
-
Google Online Security Blog
Rust in Android: move fast and fix things
Last year, we wrote about why a memory safety strategy that focuses on vulnerability prevention in new code quickly yields durable and compounding gains. This year we look at how this approach isn’t j ... Read more
The following table lists the changes that have been made to the
CVE-2025-48530 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Sep. 05, 2025
Action Type Old Value New Value Added CPE Configuration OR *cpe:2.3:o:google:android:16.0:*:*:*:*:*:*:* Added Reference Type Android (associated with Google Inc. or Open Handset Alliance): https://source.android.com/security/bulletin/2025-08-01 Types: Vendor Advisory -
CVE Modified by 134c704f-9b21-4f2e-91b3-4a467353bcc0
Sep. 05, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H Added CWE CWE-125 -
New CVE Received by [email protected]
Sep. 04, 2025
Action Type Old Value New Value Added Description In multiple locations, there is a possible condition that results in OOB accesses due to an incorrect bounds check. This could lead to remote code execution in combination with other bugs, with no additional execution privileges needed. User interaction is not needed for exploitation. Added Reference https://source.android.com/security/bulletin/2025-08-01