CVE-2025-64513
Milvus Proxy has Critical Authentication Bypass Vulnerability
Description
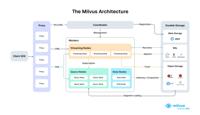
Milvus is an open-source vector database built for generative AI applications. An unauthenticated attacker can exploit a vulnerability in versions prior to 2.4.24, 2.5.21, and 2.6.5 to bypass all authentication mechanisms in the Milvus Proxy component, gaining full administrative access to the Milvus cluster. This grants the attacker the ability to read, modify, or delete data, and to perform privileged administrative operations such as database or collection management. This issue has been fixed in Milvus 2.4.24, 2.5.21, and 2.6.5. If immediate upgrade is not possible, a temporary mitigation can be applied by removing the sourceID header from all incoming requests at the gateway, API gateway, or load balancer level before they reach the Milvus Proxy. This prevents attackers from exploiting the authentication bypass behavior.
INFO
Published Date :
Nov. 10, 2025, 10:15 p.m.
Last Modified :
April 15, 2026, 12:35 a.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 4.0 | CRITICAL | [email protected] |
Solution
- Upgrade Milvus to versions 2.4.24, 2.5.21, or 2.6.5.
- Remove sourceID header from incoming requests.
- Apply mitigation at gateway or load balancer.
- Do not use the Milvus Proxy component.
Public PoC/Exploit Available at Github
CVE-2025-64513 has a 4 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-64513.
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-64513 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-64513
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
个人漏洞研究知识库,用于积累和整理 CVE 漏洞分析、复现过程、漏洞特征说明、利用脚本及相关技术文档。包含漏洞复现指南、详细证明、完整漏洞说明等资料,便于学习和参考。
Shell Java Roff Makefile C Meson PowerShell C++ Batchfile Perl
PoC for CVE-2025-64513 — Milvus Proxy Authentication Bypass Vulnerability Batch scanner to verify unauthorized access and gather Milvus version, health, and database info. For security research and defensive validation only.
CVE-2025-64513
Python
A collection of Vulnerability Research and Reverse Engineering writeups.
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-64513 vulnerability anywhere in the article.
-
Daily CyberSecurity
AI Data at Risk: Critical Milvus Flaw (CVSS 9.8) Exposes Database via Port 9091
A critical vulnerability has been discovered in Milvus, the high-performance vector database that powers many of the world’s modern AI and machine learning applications. The flaw, which carries a near ... Read more
The following table lists the changes that have been made to the
CVE-2025-64513 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
New CVE Received by [email protected]
Nov. 10, 2025
Action Type Old Value New Value Added Description Milvus is an open-source vector database built for generative AI applications. An unauthenticated attacker can exploit a vulnerability in versions prior to 2.4.24, 2.5.21, and 2.6.5 to bypass all authentication mechanisms in the Milvus Proxy component, gaining full administrative access to the Milvus cluster. This grants the attacker the ability to read, modify, or delete data, and to perform privileged administrative operations such as database or collection management. This issue has been fixed in Milvus 2.4.24, 2.5.21, and 2.6.5. If immediate upgrade is not possible, a temporary mitigation can be applied by removing the sourceID header from all incoming requests at the gateway, API gateway, or load balancer level before they reach the Milvus Proxy. This prevents attackers from exploiting the authentication bypass behavior. Added CVSS V4.0 AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H/SC:N/SI:N/SA:N/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:X/R:X/V:X/RE:X/U:X Added CWE CWE-287 Added Reference https://github.com/milvus-io/milvus/pull/45379 Added Reference https://github.com/milvus-io/milvus/pull/45383 Added Reference https://github.com/milvus-io/milvus/pull/45391 Added Reference https://github.com/milvus-io/milvus/security/advisories/GHSA-mhjq-8c7m-3f7p