CVE-2025-65964
n8n Vulnerable to Remote Code Execution via Git Node Custom Pre-Commit Hook
Description
n8n is an open source workflow automation platform. Versions 0.123.1 through 1.119.1 do not have adequate protections to prevent RCE through the project's pre-commit hooks. The Add Config operation allows workflows to set arbitrary Git configuration values, including core.hooksPath, which can point to a malicious Git hook that executes arbitrary commands on the n8n host during subsequent Git operations. Exploitation requires the ability to create or modify an n8n workflow using the Git node. This issue is fixed in version 1.119.2. Workarounds include excluding the Git Node (Docs) and avoiding cloning or interacting with untrusted repositories using the Git Node.
INFO
Published Date :
Dec. 9, 2025, 12:15 a.m.
Last Modified :
Jan. 2, 2026, 9:10 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | HIGH | [email protected] | ||||
| CVSS 4.0 | CRITICAL | [email protected] |
Solution
- Update n8n to version 1.119.2 or later.
- Exclude the Git Node if updating is not possible.
- Avoid untrusted repositories with the Git Node.
Public PoC/Exploit Available at Github
CVE-2025-65964 has a 8 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-65964.
| URL | Resource |
|---|---|
| https://github.com/n8n-io/n8n/commit/d5a1171f95f75def5c3ac577707ab913e22aef04 | Patch |
| https://github.com/n8n-io/n8n/releases/tag/n8n%401.119.2 | Release Notes |
| https://github.com/n8n-io/n8n/security/advisories/GHSA-wpqc-h9wp-chmq | Exploit Vendor Advisory |
| https://n8n-docs.teamlab.info/hosting/securing/blocking-nodes/#exclude-nodes | Third Party Advisory |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-65964 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-65964
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
CVE-2025-65964 PoC - Malicious Git Hooks
Shell
CVE-2025-65964-POC
Shell
None
Shell
CVE-2025-65964
Python
CVE-2025-65964
Shell
CVE-2025-65964复现
Shell
CVE-2025-65964-poc
Shell
一个 CVE 漏洞预警知识库,无 exp/poc,部分包含修复方案。A knowledge base of CVE security vulnerability, no PoCs/exploits.
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-65964 vulnerability anywhere in the article.

-
Daily CyberSecurity
Sandbox Shattered: Critical n8n Flaw (CVSS 9.9) Allows Remote Code Execution
Security researcher Natan Nehorai of the JFrog Security Research Team has uncovered a critical Remote Code Execution (RCE) vulnerability in n8n, the popular fair-code workflow automation platform used ... Read more

-
Daily CyberSecurity
Public Exploit Released: Critical n8n Flaw CVE-2026-21858 Exposes 100k Servers
The “central nervous system” of automation for thousands of companies has a critical weakness. A new report from Cyera reveals a devastating vulnerability in n8n, the popular workflow automation platf ... Read more
-
Daily CyberSecurity
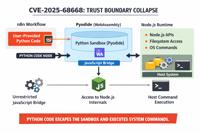
n8n Sandbox Escape: How CVE-2025-68668 Turns Workflows into Weapons
A critical vulnerability in the popular workflow automation platform n8n has been dissected in a new analysis by security researcher Rhoda Smart, revealing how a feature designed for flexibility becam ... Read more

-
Daily CyberSecurity
n8n Under Fire: Critical CVSS 10.0 RCE Vulnerability Grants Total Server Access
The popular workflow automation tool n8n has issued a critical security alert after discovering a vulnerability that could allow attackers to seize complete control of the platform. Tracked as CVE-202 ... Read more

-
Daily CyberSecurity
Critical n8n RCE Flaw (CVE-2025-65964) Allows Remote Code Execution via Git Node Configuration Manipulation
A critical security vulnerability has been discovered in n8n, the popular workflow automation tool that powers technical teams worldwide. The flaw, which carries a critical CVSS severity score of 9.4, ... Read more

-
Daily CyberSecurity
FrostBeacon Hits Russian B2B: Cobalt Strike Deployed via LNK and Chained Legacy Exploits
A new and sophisticated malware campaign dubbed “Operation FrostBeacon” is systematically targeting business-to-business (B2B) enterprises across the Russian Federation. A report from Seqrite Labs rev ... Read more
The following table lists the changes that have been made to the
CVE-2025-65964 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
Initial Analysis by [email protected]
Jan. 02, 2026
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H Added CPE Configuration OR *cpe:2.3:a:n8n:n8n:*:*:*:*:*:node.js:*:* versions from (including) 0.123.1 up to (excluding) 1.119.2 Added Reference Type GitHub, Inc.: https://github.com/n8n-io/n8n/commit/d5a1171f95f75def5c3ac577707ab913e22aef04 Types: Patch Added Reference Type GitHub, Inc.: https://github.com/n8n-io/n8n/releases/tag/n8n%401.119.2 Types: Release Notes Added Reference Type GitHub, Inc.: https://github.com/n8n-io/n8n/security/advisories/GHSA-wpqc-h9wp-chmq Types: Exploit, Vendor Advisory Added Reference Type GitHub, Inc.: https://n8n-docs.teamlab.info/hosting/securing/blocking-nodes/#exclude-nodes Types: Third Party Advisory -
New CVE Received by [email protected]
Dec. 09, 2025
Action Type Old Value New Value Added Description n8n is an open source workflow automation platform. Versions 0.123.1 through 1.119.1 do not have adequate protections to prevent RCE through the project's pre-commit hooks. The Add Config operation allows workflows to set arbitrary Git configuration values, including core.hooksPath, which can point to a malicious Git hook that executes arbitrary commands on the n8n host during subsequent Git operations. Exploitation requires the ability to create or modify an n8n workflow using the Git node. This issue is fixed in version 1.119.2. Workarounds include excluding the Git Node (Docs) and avoiding cloning or interacting with untrusted repositories using the Git Node. Added CVSS V4.0 AV:N/AC:L/AT:N/PR:L/UI:N/VC:H/VI:H/VA:H/SC:H/SI:H/SA:H/E:X/CR:X/IR:X/AR:X/MAV:X/MAC:X/MAT:X/MPR:X/MUI:X/MVC:X/MVI:X/MVA:X/MSC:X/MSI:X/MSA:X/S:X/AU:X/R:X/V:X/RE:X/U:X Added CWE CWE-829 Added Reference https://github.com/n8n-io/n8n/commit/d5a1171f95f75def5c3ac577707ab913e22aef04 Added Reference https://github.com/n8n-io/n8n/releases/tag/n8n%401.119.2 Added Reference https://github.com/n8n-io/n8n/security/advisories/GHSA-wpqc-h9wp-chmq Added Reference https://n8n-docs.teamlab.info/hosting/securing/blocking-nodes/#exclude-nodes