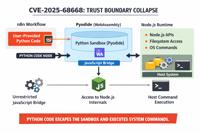
CVE-2025-68668
n8n Vulnerable to Arbitrary Command Execution in Pyodide based Python Code Node
Description
n8n is an open source workflow automation platform. From version 1.0.0 to before 2.0.0, a sandbox bypass vulnerability exists in the Python Code Node that uses Pyodide. An authenticated user with permission to create or modify workflows can exploit this vulnerability to execute arbitrary commands on the host system running n8n, using the same privileges as the n8n process. This issue has been patched in version 2.0.0. Workarounds for this issue involve disabling the Code Node by setting the environment variable NODES_EXCLUDE: "[\"n8n-nodes-base.code\"]", disabling Python support in the Code node by setting the environment variable N8N_PYTHON_ENABLED=false, which was introduced in n8n version 1.104.0, and configuring n8n to use the task runner based Python sandbox via the N8N_RUNNERS_ENABLED and N8N_NATIVE_PYTHON_RUNNER environment variables.
INFO
Published Date :
Dec. 26, 2025, 10:15 p.m.
Last Modified :
Jan. 5, 2026, 5:15 p.m.
Remotely Exploit :
Yes !
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | [email protected] | ||||
| CVSS 3.1 | CRITICAL | MITRE-CVE | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Update n8n to version 2.0.0 or later.
- Alternatively, disable the Code Node via NODES_EXCLUDE.
- Disable Python support via N8N_PYTHON_ENABLED=false.
- Configure task runner based Python sandbox.
Public PoC/Exploit Available at Github
CVE-2025-68668 has a 14 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-68668.
| URL | Resource |
|---|---|
| https://github.com/n8n-io/n8n/security/advisories/GHSA-62r4-hw23-cc8v | Patch Vendor Advisory |
| https://www.smartkeyss.com/post/cve-2025-68668-breaking-out-of-the-python-sandbox-in-n8n |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-68668 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-68668
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
None
JavaScript
None
Python Dockerfile Shell
None
HTML CSS JavaScript Shell
None
Dockerfile Python Shell
This project was built during the Cryptonic Area Cybersecurity Virtual Internship Program. This is a study of a n8n vulnerability (CVE-2025-68668)
AI Agent Sandbox Security Auditor - Runtime probe for agent execution environment isolation (OWASP Agentic Top 10)
Python
Hack
Dockerfile Python Shell Perl
n8n Ni8mare - Unauthenticated Arbitrary File Read to RCE Chain (CVSS 10.0)
exploit n8n poc rce security vulnerability cve-2026-21858 ni8mare
Dockerfile Python Shell
https://genai.owasp.org/initiatives/#ai-redteaming
Makefile Python JavaScript Dockerfile Shell
Welcome to Shellockolm-ai-CLI-MCP-Scanner - 🎯 Your React app is probably vulnerable. Find out in 30 seconds 🚀
cve cybersecurity devsecops nextjs python react security security-tools vulnerability-management vulnerability-scanner malware-detection npm supply-chain-security threat-detection model-context-protocol security-automation bug-bounty cli nodejs sbom
Python Shell HTML JavaScript TypeScript CSS PowerShell Batchfile
GRC News Assistant 3.0
这是一个每天同步Vulnerability-Wiki中docs-base中内容的项目
HTML
一个 CVE 漏洞预警知识库,无 exp/poc,部分包含修复方案。A knowledge base of CVE security vulnerability, no PoCs/exploits.
一个漏洞 PoC 知识库。A knowledge base for vulnerability PoCs(Proof of Concept), with 1k+ vulnerabilities.
poc
Dockerfile Java Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-68668 vulnerability anywhere in the article.

-
The Cyber Express
GitHub Fixes Critical RCE Bug CVE-2026-3854 Within Hours of Discovery
Cybersecurity researchers have revealed critical details about a newly identified RCE vulnerability, tracked as CVE-2026-3854, affecting both GitHub’s cloud infrastructure and GitHub Enterprise Server ... Read more

-
Daily CyberSecurity
Popular n8n Platform Hit by Triple Threat of RCE Flaws
The n8n workflow automation platform, a favorite among technical teams for its “fair-code” flexibility and AI capabilities, has been struck by a cluster of critical security vulnerabilities. Security ... Read more
-
The Cyber Express
Critical vLLM Flaw Exposes Millions of AI Servers to Remote Code Execution
A newly disclosed security flaw has placed millions of AI servers at risk after researchers identified a critical vulnerability in vLLM, a widely deployed Python package for serving large language mod ... Read more

-
Daily CyberSecurity
CVE-2026-24002: Critical Sandbox Escape Turns Grist Spreadsheets into RCE Weapons
A seemingly innocent spreadsheet formula could be the key to compromising entire organizations, thanks to a critical vulnerability uncovered by Cyera Research Labs in Grist-Core. The flaw, tracked as ... Read more

-
Daily CyberSecurity
Sandbox Shattered: Critical n8n Flaw (CVSS 9.9) Allows Remote Code Execution
Security researcher Natan Nehorai of the JFrog Security Research Team has uncovered a critical Remote Code Execution (RCE) vulnerability in n8n, the popular fair-code workflow automation platform used ... Read more

-
The Hacker News
Critical Grist-Core Vulnerability Allows RCE Attacks via Spreadsheet Formulas
A critical security flaw has been disclosed in Grist‑Core, an open-source, self-hosted version of the Grist relational spreadsheet-database, that could result in remote code execution. The vulnerabili ... Read more
-
Schneier on Security
New Vulnerability in n8n
This isn’t good: We discovered a critical vulnerability (CVE-2026-21858, CVSS 10.0) in n8n that enables attackers to take over locally deployed instances, impacting an estimated 100,000 servers global ... Read more

-
The Cyber Express
MS-ISAC Flags High-Risk Security Flaws in Fortinet Products
A new cybersecurity advisory from the Multi-State Information Sharing and Analysis Center (MS-ISAC) is alerting organizations to multiple vulnerabilities affecting Fortinet products, some of which cou ... Read more

-
SentinelOne
The Good, the Bad and the Ugly in Cybersecurity – Week 2
The Good | U.K. Government Resets Public-Sector Cybersecurity With £210M Action Plan The United Kingdom has unveiled a sweeping reset of its public-sector cybersecurity strategy, committing more than ... Read more

-
SentinelOne
The Good, the Bad and the Ugly in Cybersecurity – Week 2
The Good | U.K. Government Resets Public-Sector Cybersecurity With £210M Action Plan The United Kingdom has unveiled a sweeping reset of its public-sector cybersecurity strategy, committing more than ... Read more

-
The Cyber Express
What Is a Proxy Server? A Complete Guide to Types, Uses, and Benefits
The term proxy server is very popular these days, especially when discussions are around internet security, internet privacy, and network management. But what exactly is a proxy server? What purpose d ... Read more

-
CybersecurityNews
New Critical n8n Vulnerability Allow Attackers to Execute Arbitrary Commands
A critical vulnerability has been discovered in n8n, the popular open-source workflow automation platform, enabling authenticated attackers to execute arbitrary commands on host systems. The vulnerabi ... Read more
-
Daily CyberSecurity
n8n Sandbox Escape: How CVE-2025-68668 Turns Workflows into Weapons
A critical vulnerability in the popular workflow automation platform n8n has been dissected in a new analysis by security researcher Rhoda Smart, revealing how a feature designed for flexibility becam ... Read more

-
The Cyber Express
Critical n8n Vulnerability Allows Arbitrary Command Execution (CVE-2025-68668)
A newly disclosed n8n vulnerability has been confirmed to allow authenticated users to execute arbitrary system commands on affected servers. The issue, tracked as CVE-2025-68668, has been assigned a ... Read more

-
The Hacker News
New n8n Vulnerability (9.9 CVSS) Lets Authenticated Users Execute System Commands
Jan 06, 2026Ravie LakshmananVulnerability / DevOps A new critical security vulnerability has been disclosed in n8n, an open-source workflow automation platform, that could enable an authenticated at ... Read more
The following table lists the changes that have been made to the
CVE-2025-68668 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
CVE Modified by af854a3a-2127-422b-91ae-364da2661108
Jan. 05, 2026
Action Type Old Value New Value Added Reference https://www.smartkeyss.com/post/cve-2025-68668-breaking-out-of-the-python-sandbox-in-n8n -
Initial Analysis by [email protected]
Dec. 31, 2025
Action Type Old Value New Value Added CVSS V3.1 AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H Added CPE Configuration OR *cpe:2.3:a:n8n:n8n:*:*:*:*:*:node.js:*:* versions from (including) 1.0.0 up to (excluding) 2.0.0 Added Reference Type GitHub, Inc.: https://github.com/n8n-io/n8n/security/advisories/GHSA-62r4-hw23-cc8v Types: Patch, Vendor Advisory -
New CVE Received by [email protected]
Dec. 26, 2025
Action Type Old Value New Value Added Description n8n is an open source workflow automation platform. From version 1.0.0 to before 2.0.0, a sandbox bypass vulnerability exists in the Python Code Node that uses Pyodide. An authenticated user with permission to create or modify workflows can exploit this vulnerability to execute arbitrary commands on the host system running n8n, using the same privileges as the n8n process. This issue has been patched in version 2.0.0. Workarounds for this issue involve disabling the Code Node by setting the environment variable NODES_EXCLUDE: "[\"n8n-nodes-base.code\"]", disabling Python support in the Code node by setting the environment variable N8N_PYTHON_ENABLED=false, which was introduced in n8n version 1.104.0, and configuring n8n to use the task runner based Python sandbox via the N8N_RUNNERS_ENABLED and N8N_NATIVE_PYTHON_RUNNER environment variables. Added CVSS V3.1 AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:L Added CWE CWE-693 Added Reference https://github.com/n8n-io/n8n/security/advisories/GHSA-62r4-hw23-cc8v